Question: The figure below lists three approaches to protecting objects against security threads.Choose one and briefly describe how it might be implemented in Java. Data is
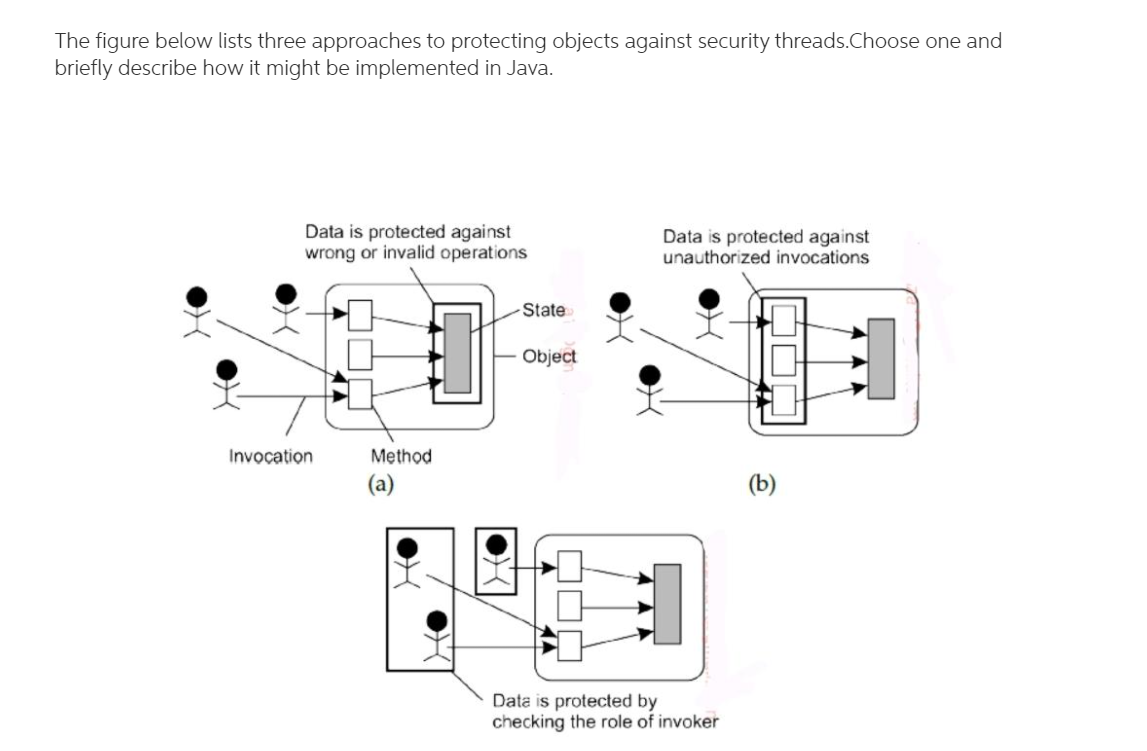
The figure below lists three approaches to protecting objects against security threads.Choose one and briefly describe how it might be implemented in Java. Data is protected against wrong or invalid operations Data is protected against unauthorized invocations State Object Invocation Method (a) (b) Data is protected by checking the role of invoker The figure below lists three approaches to protecting objects against security threads.Choose one and briefly describe how it might be implemented in Java. Data is protected against wrong or invalid operations Data is protected against unauthorized invocations State Object Invocation Method (a) (b) Data is protected by checking the role of invoker
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


