The following problems are about bit masks. 1. Masks and Shifts. 1.1 Write one C instruction...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
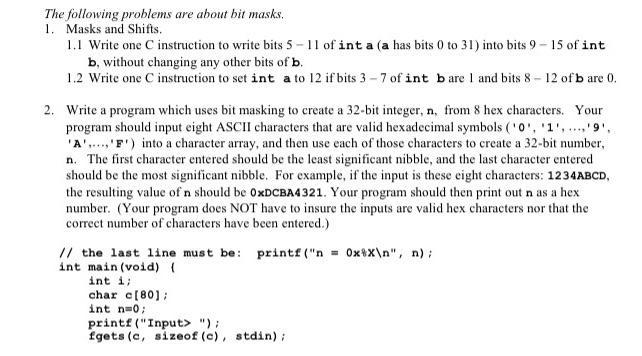
The following problems are about bit masks. 1. Masks and Shifts. 1.1 Write one C instruction to write bits 5-11 of int a (a has bits 0 to 31) into bits 9 - 15 of int b, without changing any other bits of b. 1.2 Write one C instruction to set int a to 12 if bits 3-7 of int bare 1 and bits 8-12 of b are 0. 2. Write a program which uses bit masking to create a 32-bit integer, n, from 8 hex characters. Your program should input eight ASCII characters that are valid hexadecimal symbols ('0', '1','9'. 'A'..., 'F') into a character array, and then use each of those characters to create a 32-bit number, n. The first character entered should be the least significant nibble, and the last character entered should be the most significant nibble. For example, if the input is these eight characters: 1234ABCD, the resulting value of n should be 0xDCBA4321. Your program should then print out n as a hex number. (Your program does NOT have to insure the inputs are valid hex characters nor that the correct number of characters have been entered.) // the last line must be: printf ("n=0xx\n", n); int main (void) { int i; char c[80]; int n=0; printf("Input> "); fgets (c, sizeof (c), stdin); The following problems are about bit masks. 1. Masks and Shifts. 1.1 Write one C instruction to write bits 5-11 of int a (a has bits 0 to 31) into bits 9-15 of int b, without changing any other bits of b. 1.2 Write one C instruction to set int a to 12 if bits 3-7 of int bare 1 and bits 8-12 of b are 0. 2. Write a program which uses bit masking to create a 32-bit integer, n, from 8 hex characters. Your program should input eight ASCII characters that are valid hexadecimal symbols ('0', '1','9'. 'A'..., 'F') into a character array, and then use each of those characters to create a 32-bit number, n. The first character entered should be the least significant nibble, and the last character entered should be the most significant nibble. For example, if the input is these eight characters: 1234ABCD, the resulting value of n should be 0xDCBA4321. Your program should then print out n as a hex number. (Your program does NOT have to insure the inputs are valid hex characters nor that the correct number of characters have been entered.) // the last line must be: printf ("n=0xx\n", n); int main (void) ( int i; char c[80]; int n=0; printf("Input> "); fgets (c, sizeof (c), stdin); The following problems are about bit masks. 1. Masks and Shifts. 1.1 Write one C instruction to write bits 5-11 of int a (a has bits 0 to 31) into bits 9 - 15 of int b, without changing any other bits of b. 1.2 Write one C instruction to set int a to 12 if bits 3-7 of int bare 1 and bits 8-12 of b are 0. 2. Write a program which uses bit masking to create a 32-bit integer, n, from 8 hex characters. Your program should input eight ASCII characters that are valid hexadecimal symbols ('0', '1','9'. 'A'..., 'F') into a character array, and then use each of those characters to create a 32-bit number, n. The first character entered should be the least significant nibble, and the last character entered should be the most significant nibble. For example, if the input is these eight characters: 1234ABCD, the resulting value of n should be 0xDCBA4321. Your program should then print out n as a hex number. (Your program does NOT have to insure the inputs are valid hex characters nor that the correct number of characters have been entered.) // the last line must be: printf ("n=0xx\n", n); int main (void) { int i; char c[80]; int n=0; printf("Input> "); fgets (c, sizeof (c), stdin); The following problems are about bit masks. 1. Masks and Shifts. 1.1 Write one C instruction to write bits 5-11 of int a (a has bits 0 to 31) into bits 9-15 of int b, without changing any other bits of b. 1.2 Write one C instruction to set int a to 12 if bits 3-7 of int bare 1 and bits 8-12 of b are 0. 2. Write a program which uses bit masking to create a 32-bit integer, n, from 8 hex characters. Your program should input eight ASCII characters that are valid hexadecimal symbols ('0', '1','9'. 'A'..., 'F') into a character array, and then use each of those characters to create a 32-bit number, n. The first character entered should be the least significant nibble, and the last character entered should be the most significant nibble. For example, if the input is these eight characters: 1234ABCD, the resulting value of n should be 0xDCBA4321. Your program should then print out n as a hex number. (Your program does NOT have to insure the inputs are valid hex characters nor that the correct number of characters have been entered.) // the last line must be: printf ("n=0xx\n", n); int main (void) ( int i; char c[80]; int n=0; printf("Input> "); fgets (c, sizeof (c), stdin);
Expert Answer:
Answer rating: 100% (QA)
Explanation 11 To write bits 511 of a into bits 915 of b without changing any other bits of b we can use bitwise operations like this b b 0x7F 9 a 0x7F 9 Heres how it works step by step 0x7F is a bina... View the full answer

Related Book For 

Posted Date:
Students also viewed these programming questions
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
The following problems are about the steady state response of LTI systems due to periodic signals. (a) The transfer function of a LTI system is If the input to this system is x(t) = 1 + cos(t +...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Hydrocarbon A has the formula C 9 H 12 and absorbs 3 equivalents of H 2 to yield R, C 9 H 18 , when hydrogenated over a Pd/C catalyst. On treatment of A with aqueous H 2 SO 4 in the presence of...
-
In searching the bottom of a pool at night, a watchman shines a narrow beam of light from his flashlight, 1.3 m above the water level, onto the surface of the water at a point 2.5 m from his foot at...
-
Refer to the slope in Problem 16.7. Assume that the shear strength of the soil is improved by soil stabilization methods, and the new properties are as follows: = 22 kN/m 3 , ' = 32 , and c' = 75...
-
The following data are for Huang Wong Ping Retail Outlet Stores. The account balances (in thousands) are for 2017. 1. Compute (a) the cost of goods purchased and (b) the cost of goods sold. 2....
-
(Accounting for Restricted Stock) Tweedie Company issues 10,000 shares of restricted stock to its CFO, Mary Tokar, on January 1, 2010. The stock has a fair value of $500,000 on this date. The service...
-
Q2 If Z is a normal N (0, 1), then the X = tz; process is continuous and is marginally distributed as a normal N (0, t). Is X a Brownian motion?
-
Calculate NPV Method. Use a 10% discount rate. Please show how you received the calculations Year Project A Project B 2014 ($3,000,000) ($3,000,000) 2015 $0 $975,000 2016 $600,000 $975,000 2017...
-
For this case scenario, you are taking on the persona of Ms. Tess Smith, an Organizational Development Specialist, for Cobb Medical Center. The Medical Center has a well-established Wellness Clinic...
-
To ensure that all project information records are accurate and up-to-date, the following information validation processes are implemented: 1. Data Collection - All project-related data will be...
-
1. What is a submittal? Provide an example of a submittal and explain how they verify a contractor's performance. 2. Contracts, RFP's and Specifications can be used as guides to lead your project...
-
Reflecting on your own professional experience, as well as what you have been reading from Lencioni, describe a time when there was damaging conflict on a team of which you were a member. This...
-
For this week's discussion conversations, I would like you to turn to the case study "Talent Gap: Ten-Year Employment Trends, Costs, and Global Implications" provided to us by PMI. Once you have read...
-
In all the exercises, show your working and give your final answer correct to four decimal places if required. 1. Using Laplace transforms, solve for x only in the following pair of simultaneous...
-
Write the given system without the use of matrices. D) - ()- d (x sin t + 8 (2+ 1)
-
The transfer function of an IIR filter is (a) Calculate the impulse response h[n]of the filter. (b) Would it be possible for this filter to have linear phase? Explain. (c) Sketch the magnitude...
-
Consider the following problems related to filtering of periodic signals: (a) A periodic signal x(t)of fundamental frequency Ω 0 = Ï/4 is the input of an ideal band-pass filter with...
-
An LTI discrete time system has the impulse response h[n] = (1) n u[n]. Use the convolution sum to compute the output response y[n],n 0, when the input is x[n] = u[n] u[n 3] and the initial...
-
Repeat problem 41 with the specimen of size \(100 \times 100 \times 10 \mathrm{~mm}^{3}\) and the dimensions of the cavity \(104 \times 104 \times 9 \mathrm{~mm}^{3}\). Elastic constants of the...
-
Repeat problem 41 with elastic constants of the plastic as \(E=10 \mathrm{GPa}\) and \(v=0.485\). Problem 42: A rectangular plastic specimen of size \(100 \times 100 \times 10 \mathrm{~mm}^{3}\) is...
-
A rectangular plastic specimen of size \(100 \times 100 \times 10 \mathrm{~mm}^{3}\) is placed in a rectangular metal cavity. The dimensions of the cavity are \(101 \times 101 \times 9...

Study smarter with the SolutionInn App