Question: The Open System Interconnection architecture is a conceptual model that characterizes and standardizes the computer network communication functions of a telecommunication or computer system
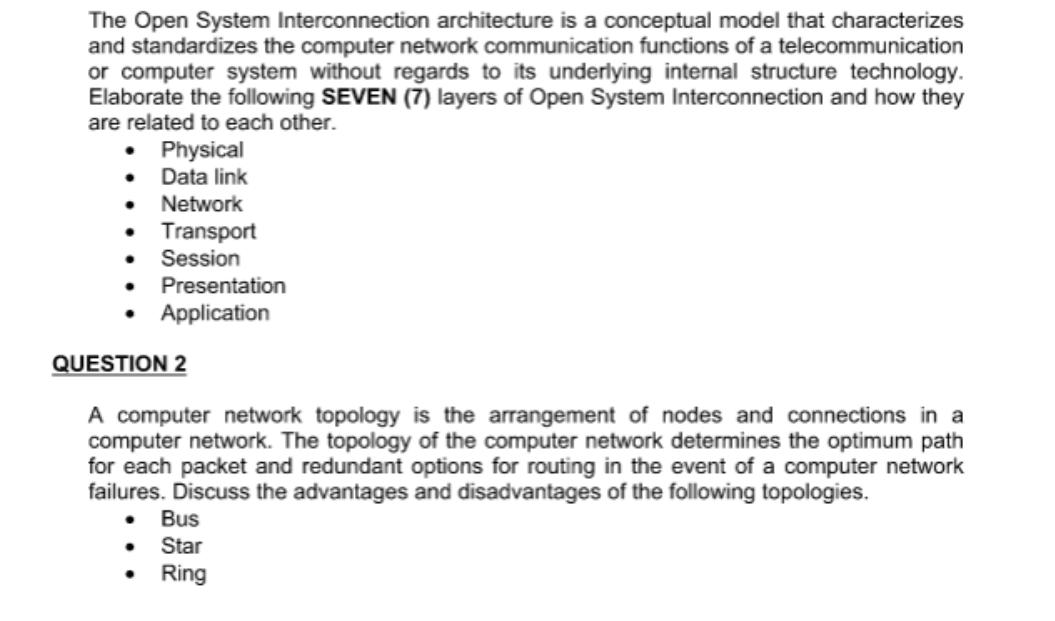
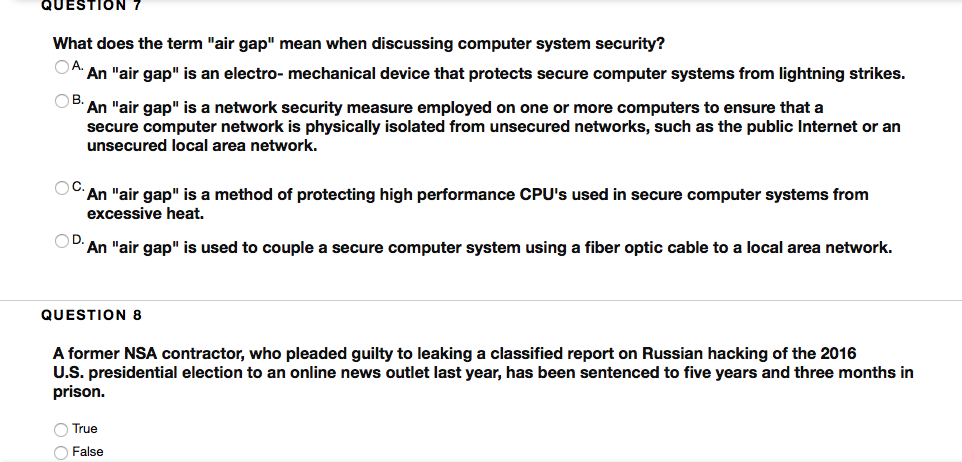
The Open System Interconnection architecture is a conceptual model that characterizes and standardizes the computer network communication functions of a telecommunication or computer system without regards to its underlying internal structure technology. Elaborate the following SEVEN (7) layers of Open System Interconnection and how they are related to each other. Physical . Data link Network Transport Session Application Presentation QUESTION 2 A computer network topology is the arrangement of nodes and connections in a computer network. The topology of the computer network determines the optimum path for each packet and redundant options for routing in the event of a computer network failures. Discuss the advantages and disadvantages of the following topologies. Bus Star Ring QUESTION 7 What does the term "air gap" mean when discussing computer system security? OA. An "air gap" is an electro- mechanical device that protects secure computer systems from lightning strikes. B. An "air gap" is a network security measure employed on one or more computers to ensure that a secure computer network is physically isolated from unsecured networks, such as the public Internet or an unsecured local area network. OC. An "air gap" is a method of protecting high performance CPU's used in secure computer systems from excessive heat. An "air gap" is used to couple a secure computer system using a fiber optic cable to a local area network. QUESTION 8 A former NSA contractor, who pleaded guilty to leaking a classified report on Russian hacking of the 2016 U.S. presidential election to an online news outlet last year, has been sentenced to five years and three months in prison. O True O False
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


