Question: The Process Node (Otur_process_s) struct maintains their state using the state member. This 16-bit unsigned short that contains information that have been combined together
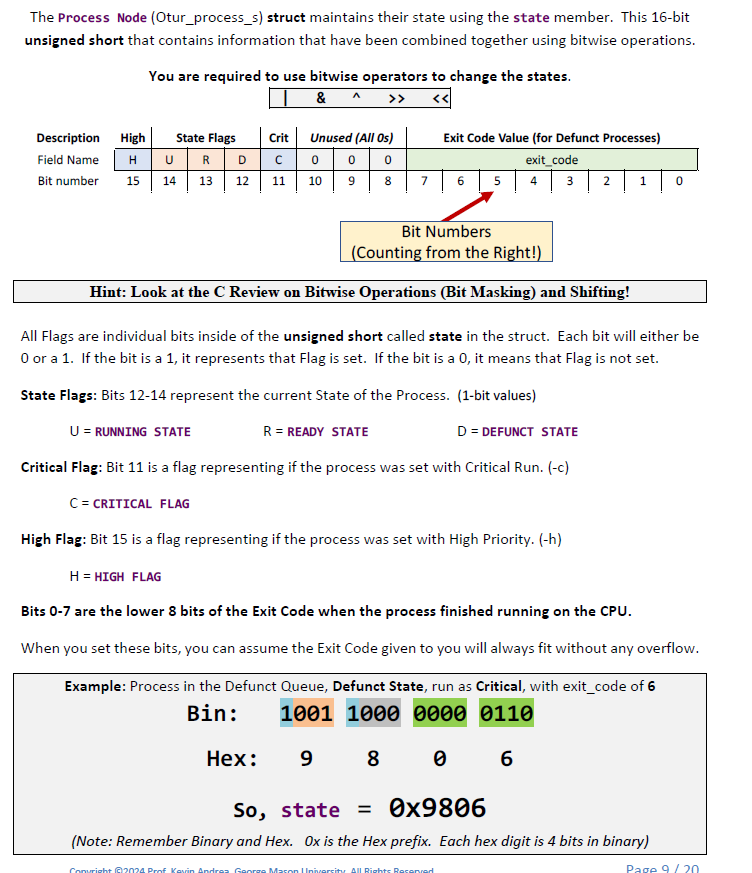
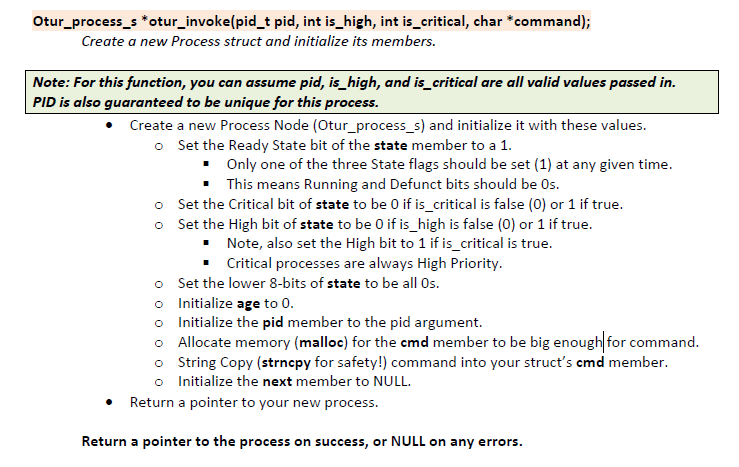
The Process Node (Otur_process_s) struct maintains their state using the state member. This 16-bit unsigned short that contains information that have been combined together using bitwise operations. You are required to use bitwise operators to change the states. & ^ >> Description High State Flags Field Name H U RD Bit number 15 14 13 12 Crit Unused (All Os) C00 0 10 9 U = RUNNING STATE 11 Bit Numbers (Counting from the Right!) Hint: Look at the C Review on Bitwise Operations (Bit Masking) and Shifting! Hex: Exit Code Value (for Defunct Processes) exit_code 4 3 2 1 8 7 6 5 All Flags are individual bits inside of the unsigned short called state in the struct. Each bit will either be 0 or a 1. If the bit is a 1, it represents that Flag is set. If the bit is a 0, it means that Flag is not set. State Flags: Bits 12-14 represent the current State of the Process. (1-bit values) R = READY STATE D = DEFUNCT STATE Critical Flag: Bit 11 is a flag representing if the process was set with Critical Run. (-c) C = CRITICAL FLAG High Flag: Bit 15 is a flag representing if the process was set with High Priority. (-h) H = HIGH FLAG Bits 0-7 are the lower 8 bits of the Exit Code when the process finished running on the CPU. When you set these bits, you can assume the Exit Code given to you will always fit without any overflow. Example: Process in the Defunct Queue, Defunct State, run as Critical, with exit_code of 6 1001 1000 0000 0110 Bin: 9 8 6 0 0 So, state = 0x9806 (Note: Remember Binary and Hex. Ox is the Hex prefix. Each hex digit is 4 bits in binary) yright 2024 Prof Kevin Mason University All Rights Resens Page 9/20 Otur_process_s *otur_invoke(pid_t pid, int is_high, int is_critical, char *command); Create a new Process struct and initialize its members. Note: For this function, you can assume pid, is_high, and is_critical are all valid values passed in. PID is also guaranteed to be unique for this process. Create a new Process Node (Otur_process_s) and initialize it with these values. o Set the Ready State bit of the state member to a 1. o o Only one of the three State flags should be set (1) at any given time. This means Running and Defunct bits should be Os. Set the Critical bit of state to be 0 if is_critical is false (0) or 1 if true. Set the High bit of state to be 0 if is_high is false (0) or 1 if true. Note, also set the High bit to 1 if is_critical is true. Critical processes are always High Priority. o Set the lower 8-bits of state to be all Os. o Initialize age to 0. o Initialize the pid member to the pid argument. o Allocate memory (malloc) for the cmd member to be big enough for command. o String Copy (strncpy for safety!) command into your struct's cmd member. o Initialize the next member to NULL. Return a pointer to your new process. Return a pointer to the process on success, or NULL on any errors.
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


