Question: There is no solution to this in the cryptography and network security 7th edition solutions manual. Someone answered the first part of question 4.6 but
There is no solution to this in the cryptography and network security 7th edition solutions manual. Someone answered the first part of question 4.6 but not the second part. I am stuck on this
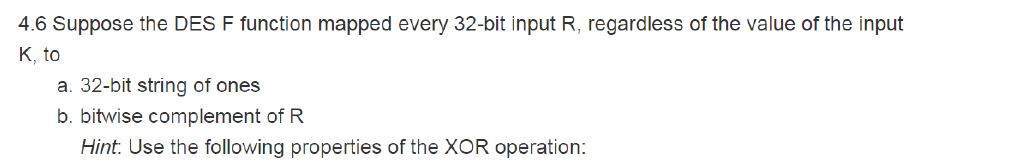
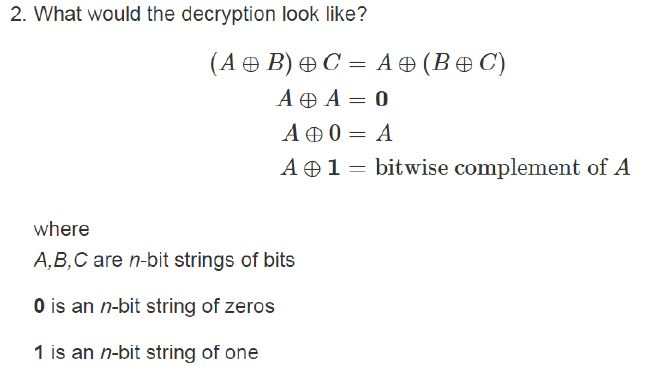
4.6 Suppose the DES F function mapped every 32-bit input R, regardless of the value of the input K, to a. 32-bit string of ones b. bitwise complement of R Hint: Use the following properties of the XOR operation: 2. What would the decryption look like? ( AB) C= A ( BC) AA=0 A 0= A A 1 = bitwise complement of A where A,B,C are n-bit strings of bits O is an n-bit string of zeros 1 is an n-bit string of one 4.6 Suppose the DES F function mapped every 32-bit input R, regardless of the value of the input K, to a. 32-bit string of ones b. bitwise complement of R Hint: Use the following properties of the XOR operation: 2. What would the decryption look like? ( AB) C= A ( BC) AA=0 A 0= A A 1 = bitwise complement of A where A,B,C are n-bit strings of bits O is an n-bit string of zeros 1 is an n-bit string of one
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


