Question: 4. During enumeration, information is systematically collected, and individual systems are identified. The pen testers examine the system in its entirety; this allows them
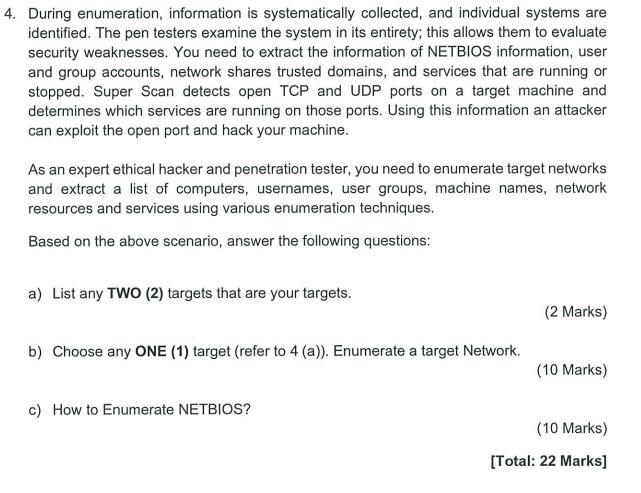
4. During enumeration, information is systematically collected, and individual systems are identified. The pen testers examine the system in its entirety; this allows them to evaluate security weaknesses. You need to extract the information of NETBIOS information, user and group accounts, network shares trusted domains, and services that are running or stopped. Super Scan detects open TCP and UDP ports on a target machine and determines which services are running on those ports. Using this information an attacker can exploit the open port and hack your machine. As an expert ethical hacker and penetration tester, you need to enumerate target networks and extract a list of computers, usernames, user groups, machine names, network resources and services using various enumeration techniques. Based on the above scenario, answer the following questions: a) List any TWO (2) targets that are your targets. b) Choose any ONE (1) target (refer to 4 (a)). Enumerate a target Network. c) How to Enumerate NETBIOS? (2 Marks) (10 Marks) (10 Marks) [Total: 22 Marks]
Step by Step Solution
3.39 Rating (152 Votes )
There are 3 Steps involved in it
a The first target is to enumerate a list of computers usernames user gr... View full answer

Get step-by-step solutions from verified subject matter experts


