Question: This is all the information I've received. How would I go about approaching this? How would you fill the table? Thank you for your assistance!
This is all the information I've received. How would I go about approaching this? How would you fill the table? Thank you for your assistance!
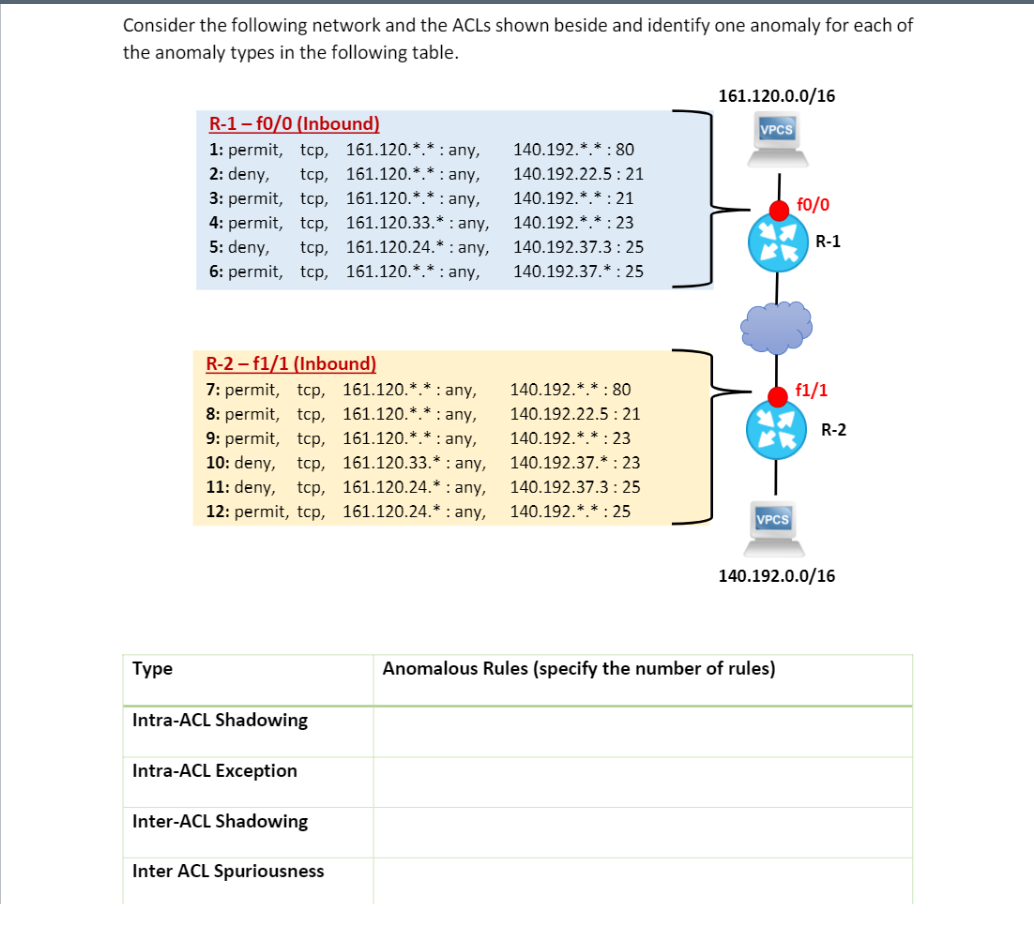
Consider the following network and the ACLs shown beside and identify one anomaly for each of the anomaly types in the following table. 161.120.0.0/16 VPCS R-1 - f0/0 (Inbound) 1: permit, top, 161.120.** : any, 2: deny, tcp, 161.120.*.* : any, 3: permit, top, 161.120.** : any, 4: permit, top, 161.120.33.* : any, 5: deny, top, 161.120.24.* : any, 6: permit, top, 161.120.** : any, 140.192.**:80 140.192.22.5:21 140.192.*.*:21 140.192.* *:23 140.192.37.3:25 140.192.37.* : 25 f0/0 R-1 f1/1 R-2-f1/1 (Inbound) 7: permit, top, 161.120.** : any, 8: permit, tcp, 161.120.** : any, 9: permit, tcp, 161.120.**: any, 10: deny, top, 161.120.33.* : any, 11: deny, tcp, 161.120.24.* : any, 12: permit, tcp, 161.120.24.* : any, R-2 140.192.** : 80 140.192.22.5 : 21 140.192.**:23 140.192.3 *:23 140.192.37.3:25 140.192.**:25 VPCS 140.192.0.0/16 Type Anomalous Rules (specify the number of rules) Intra-ACL Shadowing Intra-ACL Exception Inter-ACL Shadowing Inter ACL Spuriousness
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


