Question: This is checking for *hijacking vulnerabilities*, not general errors. Assume things are declared properly elsewhere in the code. Part 2: Recognize Control Hijacking Vulnerabilities (8
 This is checking for *hijacking vulnerabilities*, not general errors. Assume things are declared properly elsewhere in the code.
This is checking for *hijacking vulnerabilities*, not general errors. Assume things are declared properly elsewhere in the code.
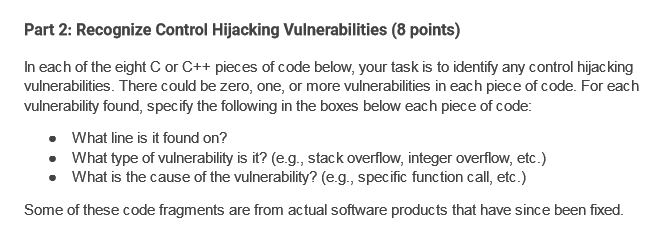
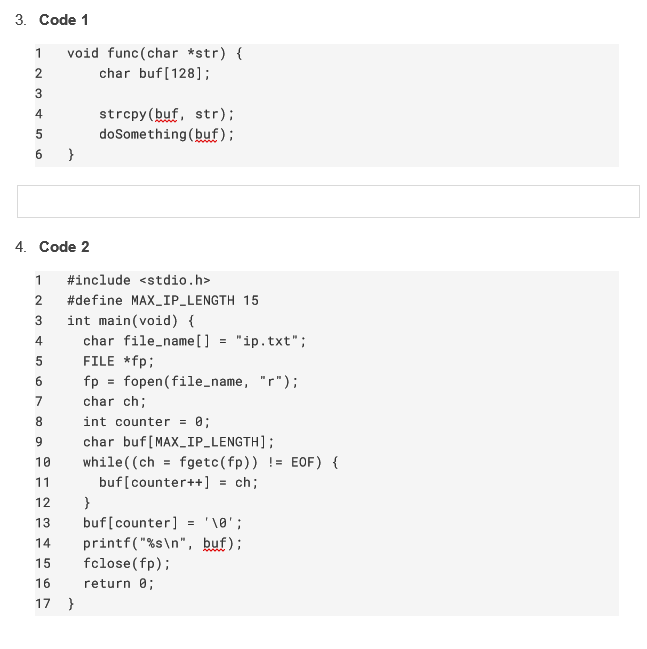
Part 2: Recognize Control Hijacking Vulnerabilities (8 points) In each of the eight C or C++ pieces of code below, your task is to identify any control hijacking vulnerabilities. There could be zero, one, or more vulnerabilities in each piece of code. For each vulnerability found, specify the following in the boxes below each piece of code: - What line is it found on? - What type of vulnerability is it? (e.g., stack overflow, integer overflow, etc.) - What is the cause of the vulnerability? (e.g., specific function call, etc.) Some of these code fragments are from actual software products that have since been fixed. 3. Code 1 4. Code 2
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


