Question: This problem deals with the Kerberos interaction below, where REQUEST = (TGT, authenticator) and REPLY = E(Bob, K_AB, ticket to Bob, S_A). Note that Alice
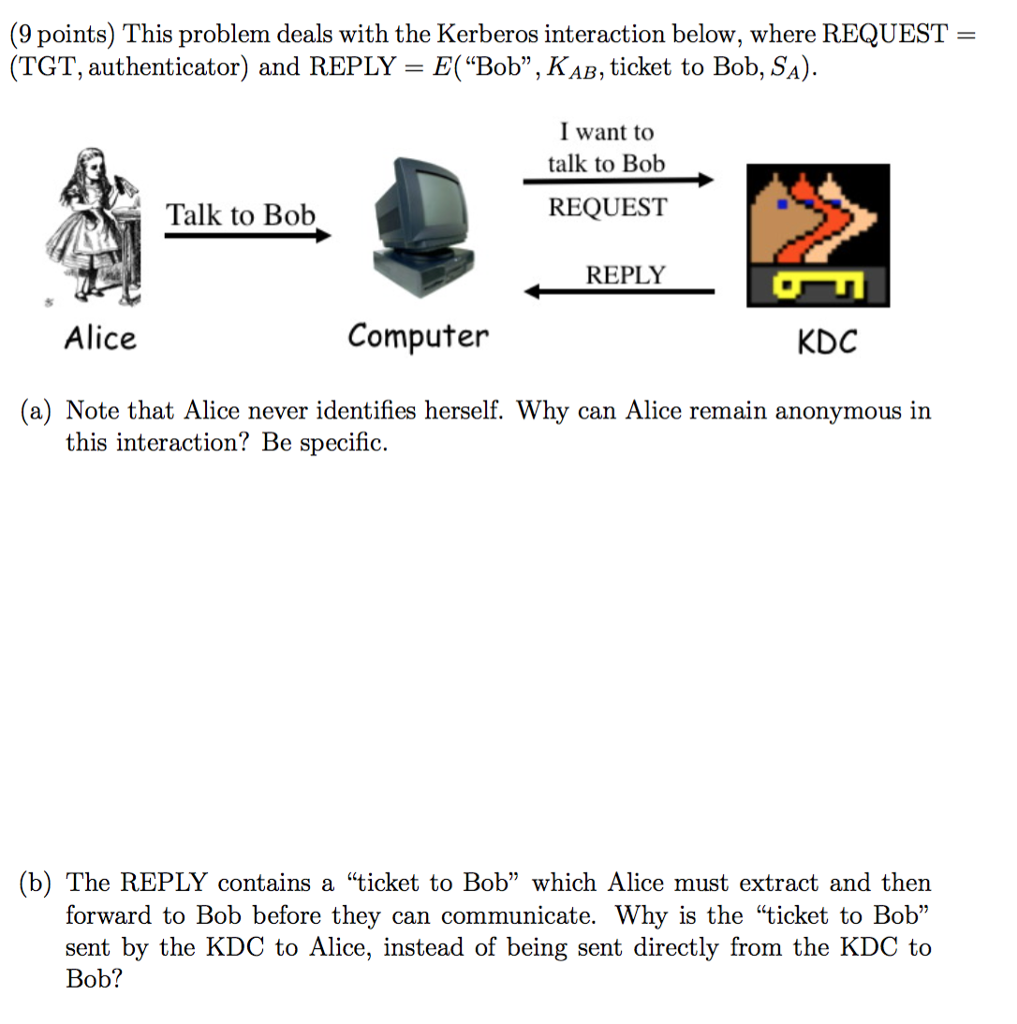
This problem deals with the Kerberos interaction below, where REQUEST = (TGT, authenticator) and REPLY = E("Bob", K_AB, ticket to Bob, S_A). Note that Alice never identifies herself. Why can Alice remain anonymous in this interaction? Be specific. The REPLY contains a "ticket to Bob" which Alice must extract and then forward to Bob before they can communicate. Why is the "ticket to Bob" sent by the KDC to Alice, instead of being sent directly from the KDC to Bob
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


