To subnet a network, bits from the host portion of the original network mask are changed...
Fantastic news! We've Found the answer you've been seeking!
Question:

Transcribed Image Text:
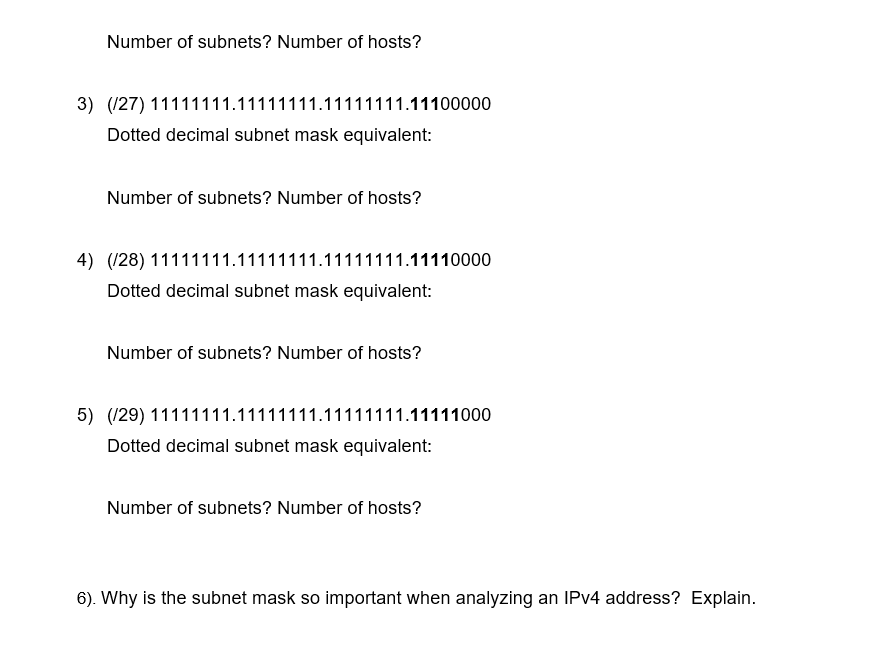
To subnet a network, bits from the host portion of the original network mask are changed into subnet bits. The number of subnet bits defines the number of subnets. Questions: Given each of the possible subnet masks depicted in the following binary format, how many subnets and how many hosts are created in each example? Hint: Remember that the number of host bits (to the power of 2) defines the number of hosts per subnet (minus 2), and the number of subnet bits (to the power of two) defines the number of subnets. The subnet bits (shown in bold) are the bits that have been borrowed beyond the original network mask of /24. The /24 is the prefix notation and corresponds to a dotted decimal mask of 255.255.255.0. 1) (25) 11111111.11111111.11111111.10000000 Dotted decimal subnet mask equivalent: Number of subnets? Number of hosts? 2) (26) 11111111.11111111.11111111.11000000 Dotted decimal subnet mask equivalent: Number of subnets? Number of hosts? 3) (27) 11111111.11111111.11111111.11100000 Dotted decimal subnet mask equivalent: Number of subnets? Number of hosts? 4) (28) 11111111.11111111.11111111.11110000 Dotted decimal subnet mask equivalent: Number of subnets? Number of hosts? 5) (29) 11111111.11111111.11111111.11111000 Dotted decimal subnet mask equivalent: Number of subnets? Number of hosts? 6). Why is the subnet mask so important when analyzing an IPv4 address? Explain. To subnet a network, bits from the host portion of the original network mask are changed into subnet bits. The number of subnet bits defines the number of subnets. Questions: Given each of the possible subnet masks depicted in the following binary format, how many subnets and how many hosts are created in each example? Hint: Remember that the number of host bits (to the power of 2) defines the number of hosts per subnet (minus 2), and the number of subnet bits (to the power of two) defines the number of subnets. The subnet bits (shown in bold) are the bits that have been borrowed beyond the original network mask of /24. The /24 is the prefix notation and corresponds to a dotted decimal mask of 255.255.255.0. 1) (25) 11111111.11111111.11111111.10000000 Dotted decimal subnet mask equivalent: Number of subnets? Number of hosts? 2) (26) 11111111.11111111.11111111.11000000 Dotted decimal subnet mask equivalent: Number of subnets? Number of hosts? 3) (27) 11111111.11111111.11111111.11100000 Dotted decimal subnet mask equivalent: Number of subnets? Number of hosts? 4) (28) 11111111.11111111.11111111.11110000 Dotted decimal subnet mask equivalent: Number of subnets? Number of hosts? 5) (29) 11111111.11111111.11111111.11111000 Dotted decimal subnet mask equivalent: Number of subnets? Number of hosts? 6). Why is the subnet mask so important when analyzing an IPv4 address? Explain.
Expert Answer:

Related Book For 

Microeconomics An Intuitive Approach with Calculus
ISBN: 978-0538453257
1st edition
Authors: Thomas Nechyba
Posted Date:
Students also viewed these computer network questions
-
You are working for the networking group of Howard Community College. The College is renting new space in the new Merriweather office building in Columbia MD. There will be new teaching labs set up...
-
Briefly describe ASCII and Unicode and draw attention to any relationship between them. [3 marks] (b) Briefly explain what a Reader is in the context of reading characters from data. [3 marks] A...
-
Should courts ever enforce illegal contracts? If illegal contracts are void as a matter of law, what is the court enforcing? If courts will use equity powers or other roundabout ways to enforce...
-
Does it seem like a good idea to let a big data computer program make hiring decisions, as some companies like Xerox are doing, as described in this chapter? What types of positions do you think this...
-
From what you've learned about effective blogging as well as planning and writing business messages in general, you should be able to identify numerous errors made by the writer of the following blog...
-
Consider the kinematic viscosity data in Table B.10. a. Perform a thorough residual analysis of these data. b. Identify the most appropriate transformation for these data. Fit this model and repeat...
-
A sample containing years to maturity and yield (percent) for 40 corporate bonds are contained in the data file named CorporateBonds (Barrons, April 2, 2012). a. Develop a scatter chart of the data...
-
When should setup begin for an operations-based exercise? Explain.
-
Bob Burley and his brother Buford ran the best restaurant in Dallas, Texas. Many out-of-towners would visit Dallas and go to Burleys Biscuits, Beef, and Veggies for a good wholesome meal. One thing...
-
This exercise studies the price competition between two major telcos in Australia: Telstra and Optus, and their relationship with NBN (National Broadband Network). NBN is a publicly-owned,...
-
Allegheny (AHERF) is presented in this chapter mainly as an example of understating expenses via: (a) Improper capitalization of expenses. (b) Understatement of cost of goods sold. (c) Understatement...
-
Why is a decreasing sales-to-PPE ratio a signal of possible overstatement of assets?
-
An increase in current liabilities as a percentage of current assets or of sales is a sign of an understatement of expenses. True/False
-
WorldCom is presented in this textbook as an illustration of overstating earnings by: (a) Holding books open after the close of a reporting period. (b) Misuse of multiple element contracts. (c)...
-
One mole of CO is initially contained on one-half of a well-insulated, rigid tank. Its temperature is 500 K. The other half of the tank is initially at vacuum. A diaphragm separates the two...
-
After the closing of a sale of a hot dog stand, the purchaser discovers that there were certain bills that were not paid. The attorney who represented the buyer had an indemnification clause and an...
-
Draw the appropriate control flow graph of the given pseudocode.Make sure to only use one number for blocks of code which are all sequential and when the first line is executed, all of those lines...
-
I recently went out to dinner with my brother and my family. We decided we wanted wings for an appetizer and had a choice of getting 10 wings for $4.95 or 20 wings for $7.95. I thought we should get...
-
Suppose you are an amateur athlete and your uncle owns the cereal company Wheaties. Your uncle offers you a job working for his company at a wage of w per hour. After looking around for other jobs,...
-
I love the Austrian candy Mozartkugeln. They are a small part of my budget, and the only factor determining my willingness to pay for additional Mozartkugeln is how many I already have. A: Suppose...
-
Who was Phar-Mors flamboyant Chief Executive Officer?
-
Which of the following generally is not considered something of value? 1. Cash, money or checks 2. Airline miles or hotel credits associated with frequent activity (e.g., frequent flier miles) 3. An...
-
Which of the following is not one of the five major categories of fraudulent disbursements? 1. Payroll schemes 2. Expense reimbursement schemes 3. Shell company schemes 4. Billing schemes

Study smarter with the SolutionInn App