Question: Two important differences between symmetric key encryption and public key encryption are: Select one: O a. (1) Symmetric key encryption is faster to perform
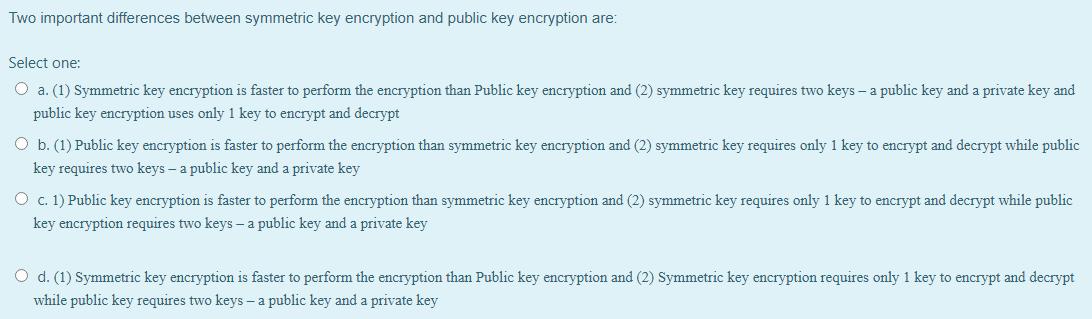
Two important differences between symmetric key encryption and public key encryption are: Select one: O a. (1) Symmetric key encryption is faster to perform the encryption than Public key encryption and (2) symmetric key requires two keys- a public key and a private key and public key encryption uses only 1 key to encrypt and decrypt O b. (1) Public key encryption is faster to perform the encryption than symmetric key encryption and (2) symmetric key requires only 1 key to encrypt and decrypt while public key requires two keys- a public key and a private key O c. 1) Public key encryption is faster to perform the encryption than symmetric key encryption and (2) symmetric key requires only 1 key to encrypt and decrypt while public key encryption requires two keys- a public key and a private key O d. (1) Symmetric key encryption is faster to perform the encryption than Public key encryption and (2) Symmetric key encryption requires only 1 key to encrypt and decrypt while public key requires two keys - a public key and a private key
Step by Step Solution
There are 3 Steps involved in it
The detailed answer for the above question is provided below The correct answer is c 1 Public key en... View full answer

Get step-by-step solutions from verified subject matter experts


