Question: Use these key terms from the lab to complete the sentences that follow: banner enumerate Nmap port scan scan signature stack fingerprinting stealth 1. is
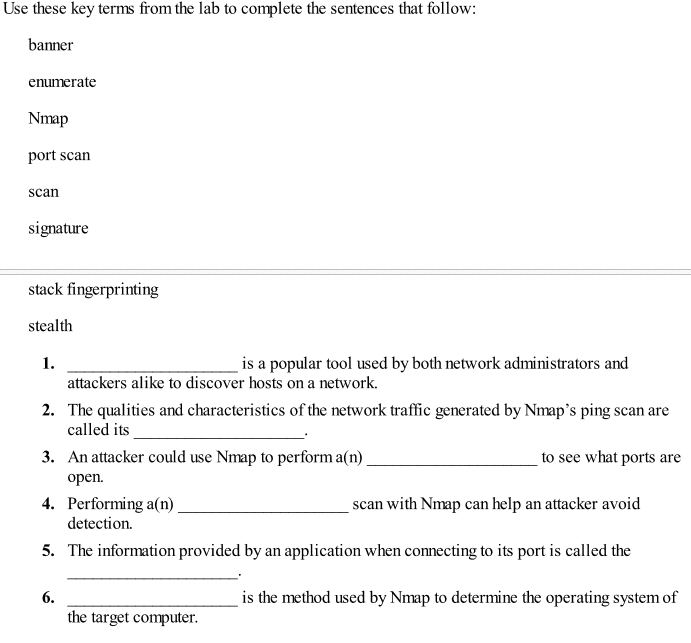
Use these key terms from the lab to complete the sentences that follow: banner enumerate Nmap port scan scan signature stack fingerprinting stealth 1. is a popular tool used by both network administrators and attackers alike to discover hosts on a network. The qualities and characteristics of the network traffic generated by Nmap's ping scan are called its An attacker could use Nmap to performa(n) open. Performing a(n) detection. The information provided by an application when connecting to its port is called the 2. 3. to see what ports are 4. scan with Nmap can help an attacker avoid 5. is the method used by Nmap to determine the operating system of the target computer
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


