Question: We have a set with n elements. Using universal hashing and hash table of size m we can achieve expected access time O(1 +
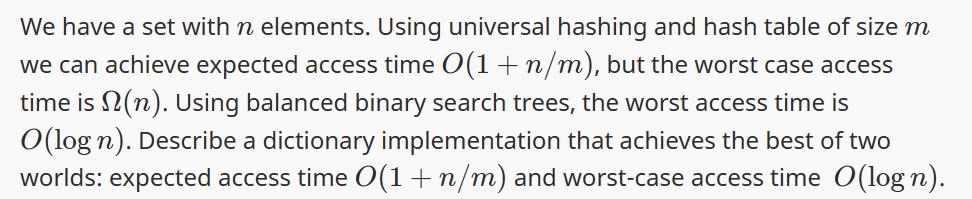
We have a set with n elements. Using universal hashing and hash table of size m we can achieve expected access time O(1 + n/m), but the worst case access time is (n). Using balanced binary search trees, the worst access time is O(log n). Describe a dictionary implementation that achieves the best of two worlds: expected access time 0(1+n/m) and worst-case access time O(logn).
Step by Step Solution
3.46 Rating (166 Votes )
There are 3 Steps involved in it
The answer provided below has been developed in a clear step by step mannerStep 1 One way to achieve ... View full answer

Get step-by-step solutions from verified subject matter experts


