Question: We worked on the DESX, which we created by adding an XOR in front of and behind the DES. Let's cancel the first of these
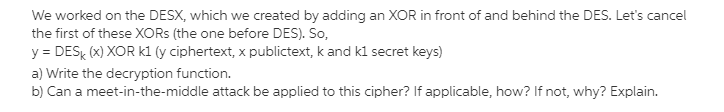
We worked on the DESX, which we created by adding an XOR in front of and behind the DES. Let's cancel the first of these XORs (the one before DES). So, y = DESK (X) XOR kl (y ciphertext, x publictext, k and ki secret keys) a) Write the decryption function. b) Can a meet-in-the-middle attack be applied to this cipher? If applicable, how? If not, why? Explain. We worked on the DESX, which we created by adding an XOR in front of and behind the DES. Let's cancel the first of these XORs (the one before DES). So, y = DESK (X) XOR kl (y ciphertext, x publictext, k and ki secret keys) a) Write the decryption function. b) Can a meet-in-the-middle attack be applied to this cipher? If applicable, how? If not, why? Explain
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


