Question: What are the typical steps involved in the post - mortem investigation of a compromised system? Retrieval of data from backups, analysis of network traffic,
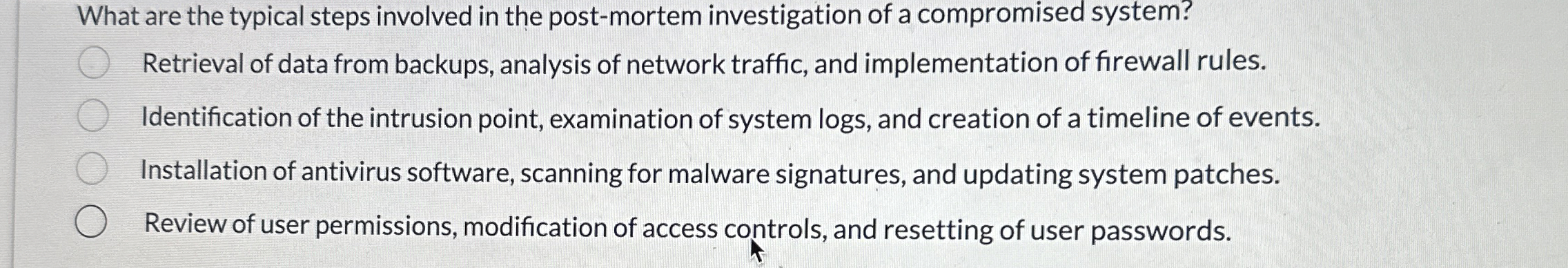
What are the typical steps involved in the postmortem investigation of a compromised system?
Retrieval of data from backups, analysis of network traffic, and implementation of firewall rules.
Identification of the intrusion point, examination of system logs and creation of a timeline of events.
Installation of antivirus software, scanning for malware signatures, and updating system patches.
Review of user permissions, modification of access controls, and resetting of user passwords.
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


