What effect might restrictions imposed by the European Community have on global companies? Regarding Data Protection. Managing
Fantastic news! We've Found the answer you've been seeking!
Question:
What effect might restrictions imposed by the European Community have on global companies? Regarding Data Protection.
Transcribed Image Text:
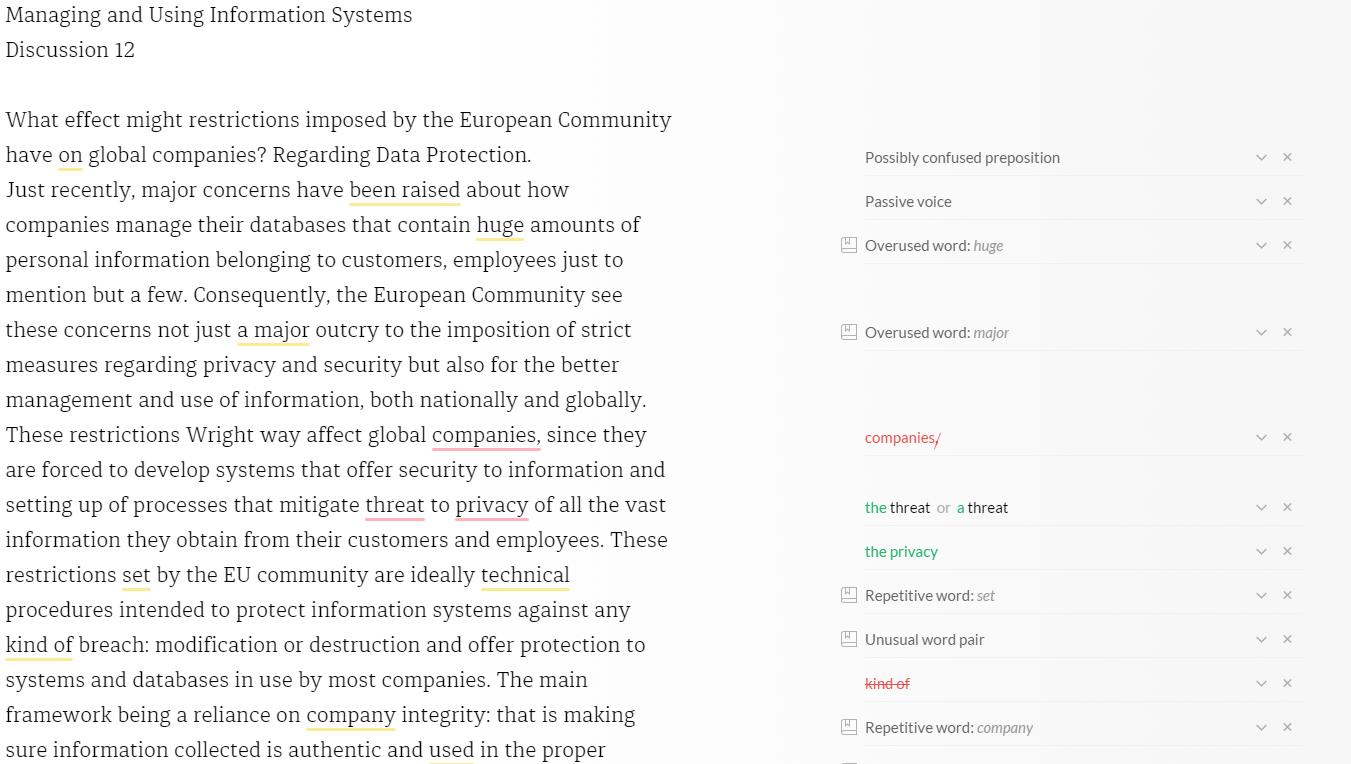
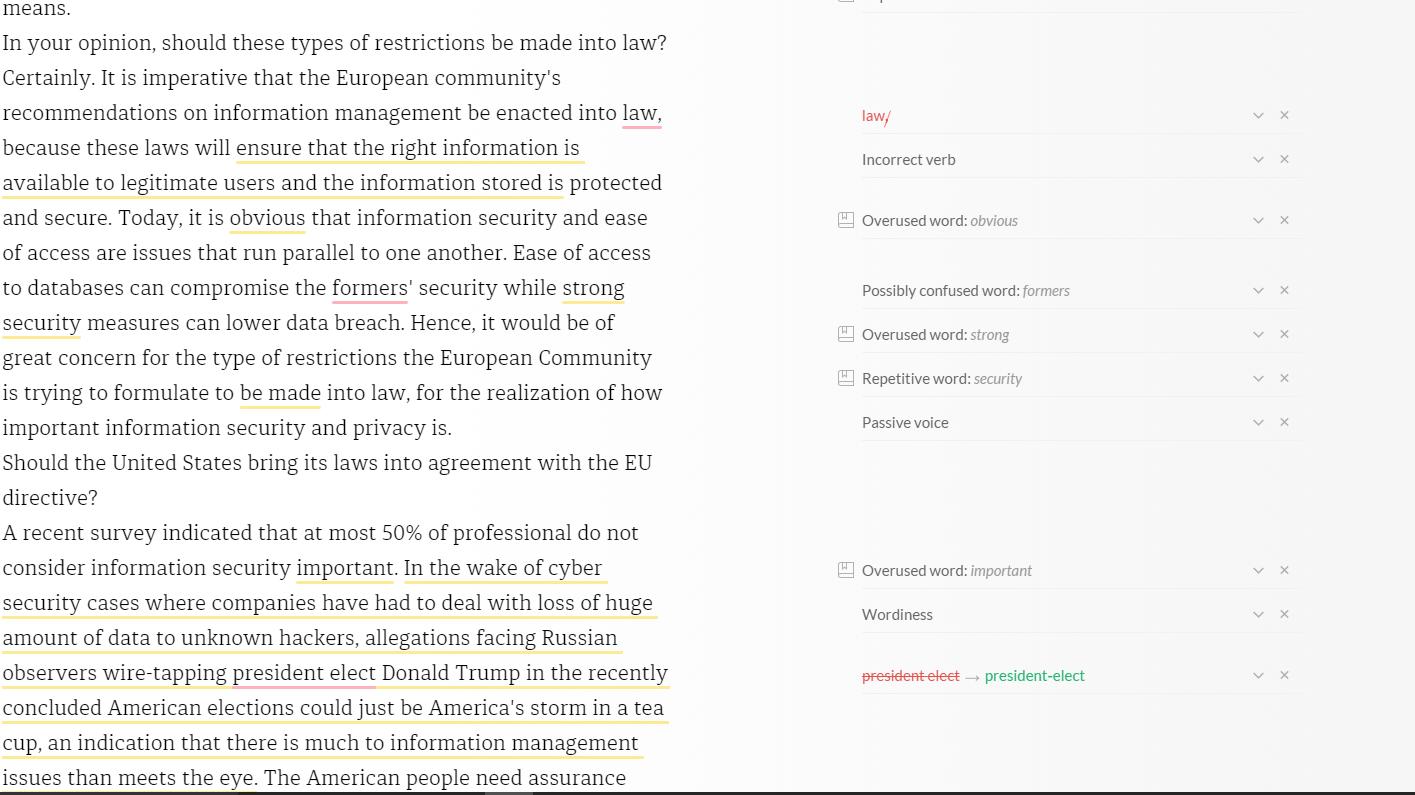
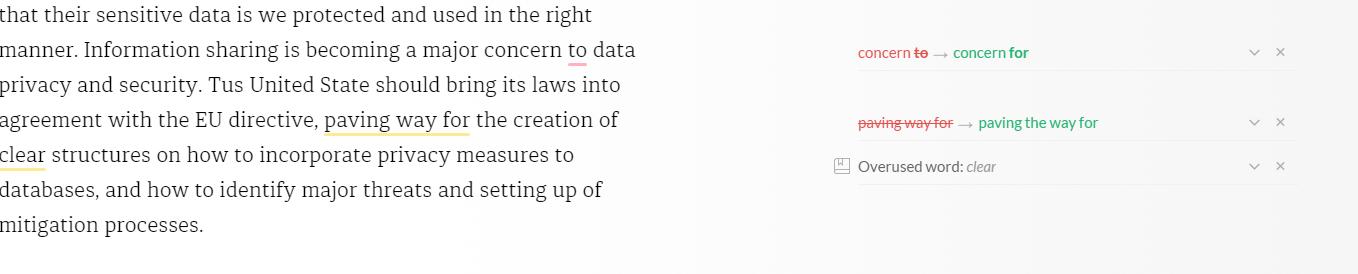
Managing and Using Information Systems Discussion 12 What effect might restrictions imposed by the European Community have on global companies? Regarding Data Protection. Just recently, major concerns have been raised about how companies manage their databases that contain huge amounts of personal information belonging to customers, employees just to mention but a few. Consequently, the European Community see these concerns not just a major outcry to the imposition of strict measures regarding privacy and security but also for the better management and use of information, both nationally and globally. These restrictions Wright way affect global companies, since they are forced to develop systems that offer security to information and setting up of processes that mitigate threat to privacy of all the vast information they obtain from their customers and employees. These restrictions set by the EU community are ideally technical procedures intended to protect information systems against any kind of breach: modification or destruction and offer protection to systems and databases in use by most companies. The main framework being a reliance on company integrity: that is making sure information collected is authentic and used in the proper Possibly confused preposition Passive voice Overused word: huge Overused word: major companies/ the threat or a threat the privacy Repetitive word: set Unusual word pair kind of Repetitive word: company V V vx ✓ X vx V X V V V X X X means. In your opinion, should these types of restrictions be made into law? Certainly. It is imperative that the European community s recommendations on information management be enacted into law, because these laws will ensure that the right information is available to legitimate users and the information stored is protected and secure. Today, it is obvious that information security and ease of access are issues that run parallel to one another. Ease of access to databases can compromise the formers security while strong security measures can lower data breach. Hence, it would be of great concern for the type of restrictions the European Community is trying to formulate to be made into law, for the realization of how important information security and privacy is. Should United States bring its laws into agreement with the EU directive? A recent survey indicated that at most 50% of professional do not consider information security important. In the wake of cyber security cases where companies have had to deal with loss of huge amount of data to unknown hackers, allegations facing Russian observers wire-tapping president elect Donald Trump in the recently concluded American elections could just be America s storm in a tea cup, an indication that there is much to information management issues than meets the eye. The American people need assurance law/ Incorrect verb Overused word: obvious Possibly confused word: formers Overused word: strong Repetitive word: security Passive voice Overused word: important Wordiness president elect → president-elect ✓ X V V V v X v X vx X X X that their sensitive data is we protected and used in the right manner. Information sharing is becoming a major concern to data privacy and security. Tus United State should bring its laws into agreement with the EU directive, paving way for the creation of clear structures on how to incorporate privacy measures to databases, and how to identify major threats and setting up of mitigation processes. concern te →→ concern for paving way for → paving the way for Overused word: clear v X v X vx Managing and Using Information Systems Discussion 12 What effect might restrictions imposed by the European Community have on global companies? Regarding Data Protection. Just recently, major concerns have been raised about how companies manage their databases that contain huge amounts of personal information belonging to customers, employees just to mention but a few. Consequently, the European Community see these concerns not just a major outcry to the imposition of strict measures regarding privacy and security but also for the better management and use of information, both nationally and globally. These restrictions Wright way affect global companies, since they are forced to develop systems that offer security to information and setting up of processes that mitigate threat to privacy of all the vast information they obtain from their customers and employees. These restrictions set by the EU community are ideally technical procedures intended to protect information systems against any kind of breach: modification or destruction and offer protection to systems and databases in use by most companies. The main framework being a reliance on company integrity: that is making sure information collected is authentic and used in the proper Possibly confused preposition Passive voice Overused word: huge Overused word: major companies/ the threat or a threat the privacy Repetitive word: set Unusual word pair kind of Repetitive word: company V V vx ✓ X vx V X V V V X X X means. In your opinion, should these types of restrictions be made into law? Certainly. It is imperative that the European community s recommendations on information management be enacted into law, because these laws will ensure that the right information is available to legitimate users and the information stored is protected and secure. Today, it is obvious that information security and ease of access are issues that run parallel to one another. Ease of access to databases can compromise the formers security while strong security measures can lower data breach. Hence, it would be of great concern for the type of restrictions the European Community is trying to formulate to be made into law, for the realization of how important information security and privacy is. Should United States bring its laws into agreement with the EU directive? A recent survey indicated that at most 50% of professional do not consider information security important. In the wake of cyber security cases where companies have had to deal with loss of huge amount of data to unknown hackers, allegations facing Russian observers wire-tapping president elect Donald Trump in the recently concluded American elections could just be America s storm in a tea cup, an indication that there is much to information management issues than meets the eye. The American people need assurance law/ Incorrect verb Overused word: obvious Possibly confused word: formers Overused word: strong Repetitive word: security Passive voice Overused word: important Wordiness president elect → president-elect ✓ X V V V v X v X vx X X X that their sensitive data is we protected and used in the right manner. Information sharing is becoming a major concern to data privacy and security. Tus United State should bring its laws into agreement with the EU directive, paving way for the creation of clear structures on how to incorporate privacy measures to databases, and how to identify major threats and setting up of mitigation processes. concern te →→ concern for paving way for → paving the way for Overused word: clear v X v X vx
Expert Answer:
Answer rating: 100% (QA)
What effect might restrictions imposed by the European Community have on global companies Regarding Data Protection Just recently major concerns have ... View the full answer

Related Book For 

Auditing and Assurance services an integrated approach
ISBN: 978-0134065823
16th edition
Authors: Alvin A. Arens, Randal J. Elder, Mark S. Beasley, Chris E. Hogan
Posted Date:
Students also viewed these general management questions
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
Founded by Jeff Bezos, online giant Amazon.com, Inc. (Amazon), was incorporated in the state of Washington in July, 1994, and sold its first book in July, 1995. In May 1997, Amazon (AMZN) completed...
-
"A 10% uniaxial tensile strain has been applied to a mouse tail tendon fascicle. Using Davis and De Vita's nonlinear viscoelastic model, plot the change in axial stress over time. Given: c1=20.3 MPa;...
-
The stockholders equity section of Haley Corporation at December 31 is as follows. HALEY CORPORATION Balance Sheet (partial) Paid-in capital Preferred stock, cumulative, 10,000 shares authorized,...
-
For each of the following individuals, determine and explain the type of residency for tax purposes for 2012. (a) Anthony entered Canada on March 1, 2012, and worked as a domestic on a southern...
-
Nick Spanos Antiques issued its \(8 \%, 10\)-year bonds payable at a price of \(\$ 440,000\) (maturity value is \(\$ 500,000\) ). The company uses the straight-line amortization method for the bonds....
-
A company has two sequential processing departments. On the cost of production reports for the departments, will the cost per unit transferred out of the first department always be equal to the cost...
-
1. Un cylindre contient 0,020 m d'oxygne molculaire temprature 25C et pression de 15 atm. Quel serait le volume de ce gaz une pression d'une atmosphre? Un patient respire cet oxygne l'aide d'un...
-
When possible, compute the truth values of the simple components in the following compound propositions. If no truth value can be computed, write a question mark (?) under the letter or letters with...
-
At January 1, 2021, Rothschild Chair Company, Inc., was indebted to First Lincoln Bank under a $33 million, 10% unsecured note. The note was signed January 1, 2018, and was due December 31, 2024....
-
The most appropriate risk attribution approach for the fixed-income manager is to: A. decompose historical returns into a top-down factor framework. B. evaluate the marginal contribution to total...
-
In managing the fund at his previous employer, Deweys investment process can be best described as: A. an activist strategy. B. a top-down strategy. C. a bottom-up strategy. Jack Dewey is managing...
-
The Barboa Fund can be best described as a fund segmented by: A. size/style. B. geography. C. economic activity. Three years ago, the Albright Investment Management Company (Albright) added four new...
-
Based on Exhibit 1, the target semideviation for the portfolio is closest to: A. 2.78%. B. 3.68%. C. 4.35%. Alexandra Jones, a senior adviser at Federalist Investors (FI), meets with Erin Bragg, a...
-
Identify the likely appropriate price benchmark for the LIM trade. Justify your response. Bradley also performs a cost analysis on the LIM trade. Noting the time gap between his trade instructions...
-
Identify three specific ways globalization has affected the marketing environment.
-
Differentiate the following terms/concepts: a. Personality types and money attitudes b. Planners and avoiders c. Moderating and adapting to biases d. "Perfectible judges" and "incorrigible judges"
-
Data analytics is a powerful tool in fraud detection and is often used to search for signs of fraud in the purchasing function. To learn more about data analytics as a fraud detection tool in...
-
If the auditor assesses control risk as high for a transaction-related audit objective, what does that imply for detection risk and the level of substantive testing?
-
How does the auditor use information obtained from the control risk assessment and testing of controls to plan audit procedures?
-
Recording effects of transactions in T-accounts Record the transactions below for Amena Company by recording debit and credit amounts directly in the following T-accounts: Cash; Accounts Receivable;...
-
Identifying type and normal balances of accounts For each of the following (1) identify the type of account as an asset, liability, equity, revenue, or expense, (2) enter debit (Dr.) or credit (Cr.)...
-
Preparing a trial balance After recording the transactions of Exercise 3-2 in T-accounts and calculating the ending balance of each account, prepare a trial balance. Use May 31, 2008, as its report...

Study smarter with the SolutionInn App