Question: Whatever is possible there be between the best and least lengths of ways from the base of the tree to a leaf? What activities should
Whatever is possible there be between the best and least lengths of ways from the base of the tree to a leaf? What activities should be performed to move from one hub in the tree to (a) its parent and (b) its posterity? [5 marks] Describe, and gauge the expenses of, strategies to (a) embed another thing into a current pile; (b) erase the highest thing from a non-void stack; (c) beginning from a cluster holding N things in inconsistent request, adjust those things so they structure a store, taking time not exactly that which would be required assuming the things were simply embedded into the load in a steady progression. [6 marks] A steady arranging strategy is one where things whose keys analyze as equivalent will show up in the result in as per the pattern in which that they showed up in the info list. Could a stack sort in light of the calculations you have archived be steady? Legitimize your response. [5 marks] 6 Topics in Artificial Intelligence Give a few motivations behind why a few errands are fit to being addressed by utilizing limitations. Represent your response with instances of such errands and the techniques by which imperatives are utilized to address them. [20 marks] 7 Operating System Foundations Consider the activity of a scheduler in a framework where there are framework level and client level cycles. Client cycles might be IO bound or CPU bound and may have client controlled (negative) need. Depict the information structures that the scheduler could utilize, including portions of cycle descriptors that the scheduler would work on. [10 marks] Describe exhaustively the conditions under which the scheduler would be placed and for each unique situation frame a planning calculation that may be utilized. [10 marks] 4 CST.95.11.5 8 Operating System Functions A working framework for a brilliant card is required - that is a typical run-time framework for the savvy card, which has some arrangement of uses stacked into the card at the time the card is given. What tasks should the memory the executives part of the working framework support in such a framework? [12 marks] The equipment engineers are worried about complex memory the executives equipment consuming an excessive amount of force, yet the client requests memory security between the applications. Portray a few arrangements that could satisfy these needs.
How is a page shortcoming took care of assuming that it is set off by an interaction giving a compose for which it has authorization on a machine with more than adequate free memory at the point the page shortcoming happens? [6 marks] (c) If the machine doesn't have adequate free memory at the point that the page shortcoming happens, a casualty page should be chosen for substitution. Depict the ideal calculation for dealing with this case, and make sense of why it can't be executed. [2 marks] (d) Now portray a reasonable calculation for choosing a casualty page for substitution. In your response you ought to examine its presentation, stockpiling and time overheads, showing any suspicions you make. [6 marks] (e) What is B'el'ady's Anomaly? Can the calculation portrayed in Part (d) experience the ill effects of it? Legitimize your response. (Note: You are not expected to exhibit an example of B'el'ady's Anomaly happening.) [4 marks] 5 (TURN OVER) CST0.2018.2.6 Segment C 5 Software and Security Engineering (a) Although the accompanying code orders and executes without mistake, give four justifications for why it is an unfortunate test. @Test public void testIt() { long time = System.currentTimeMillis(); twofold r = solve(40229321L); in the event that (r 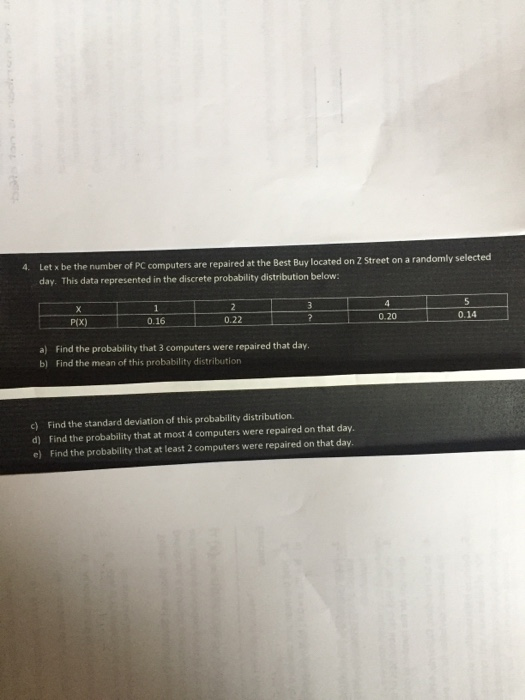
4. Let x be the number of PC computers are repaired at the Best Buy located on 2 Street on a randomly selected day. This data represented in the discrete probability distribution below: X P(X) 0.16 2 0.22 3 ? a) Find the probability that 3 computers were repaired that day. b) Find the mean of this probability distribution c) Find the standard deviation of this probability distribution. d) Find the probability that at most 4 computers were repaired on that day. e) Find the probability that at least 2 computers were repaired on that day. 4 0.20 5 0.14
Step by Step Solution
3.55 Rating (152 Votes )
There are 3 Steps involved in it
Tree Operations The best and least lengths of ways from the base of the tree to a leaf involve understanding tree traversal algorithms like depthfirst search or breadthfirst search Moving from one nod... View full answer

Get step-by-step solutions from verified subject matter experts


