Question: When a threat agent injects and executes malicious code within a web application by bypassing instructions that validate input, this is an example of Mobile
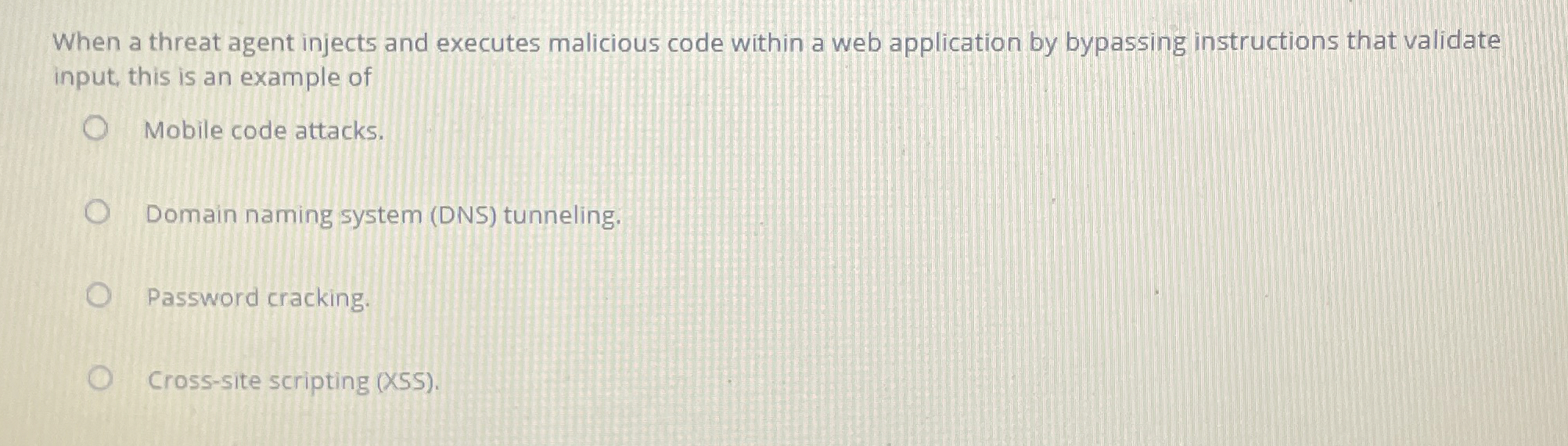
When a threat agent injects and executes malicious code within a web application by bypassing instructions that validate
input, this is an example of
Mobile code attacks.
Domain naming system DNS tunneling.
Password cracking.
Crosssite scripting XSS
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


