Question: When you study malware to discover how it functions, what operation are you performing? Establishing rules of engagement Penetration testing Vulnerability testing D Reverse engineering
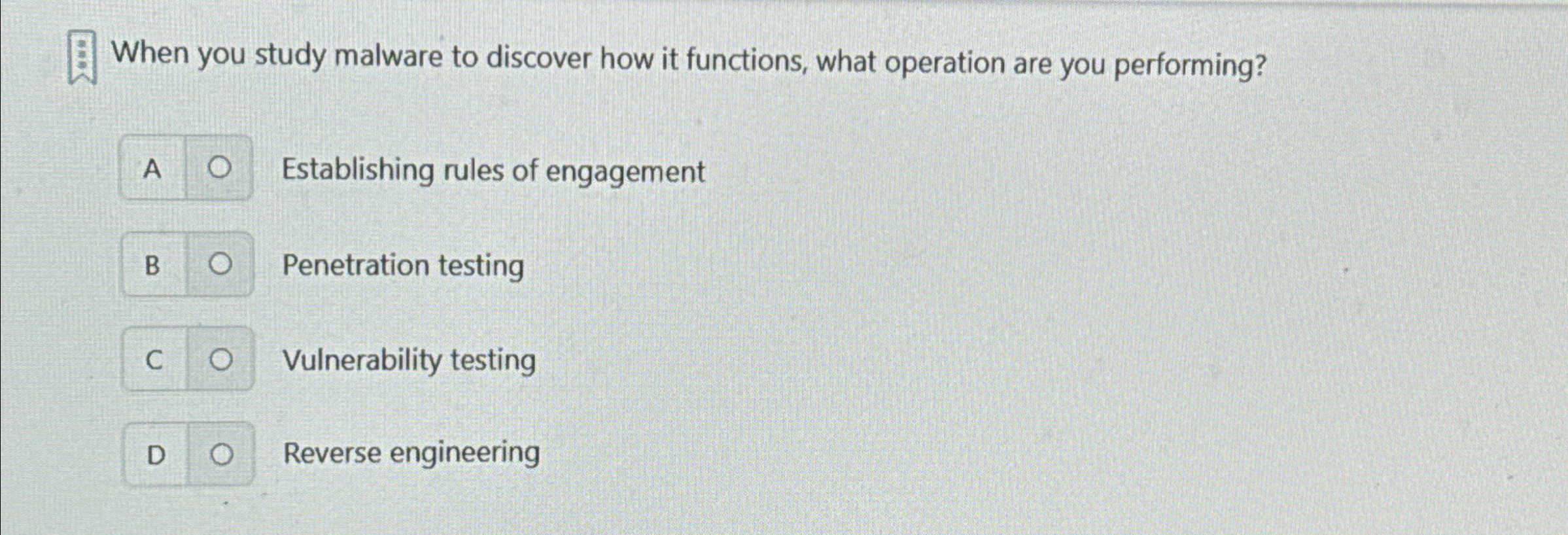
When you study malware to discover how it functions, what operation are you performing?
Establishing rules of engagement
Penetration testing
Vulnerability testing
D
Reverse engineering
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


