Question: Which weak configuration concern is responsible for allowing an attacker's port scan traffic that targets HTTP to reach an intranet server from the Internet? A
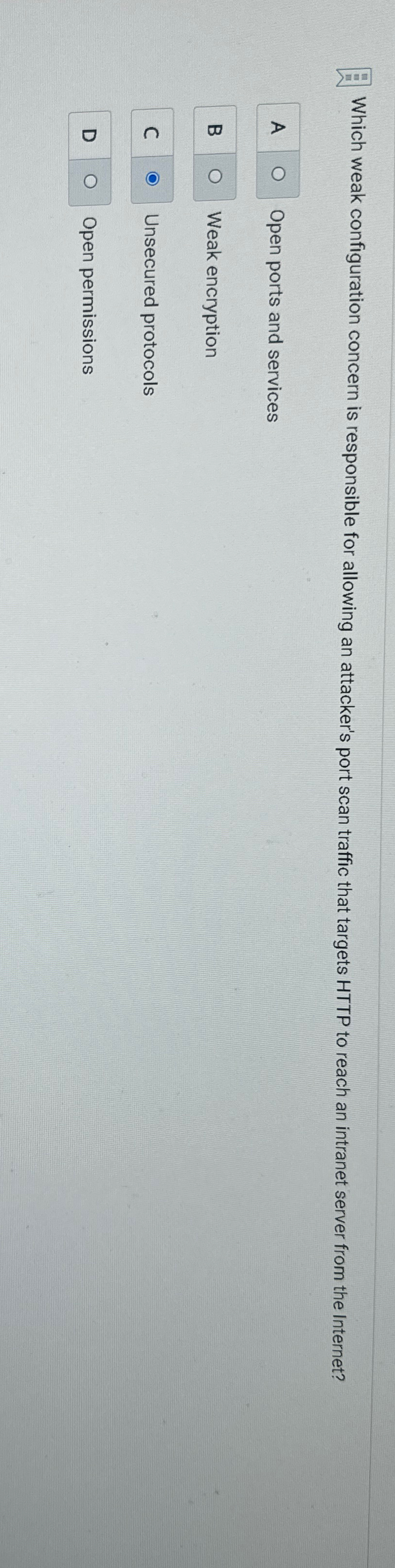
Which weak configuration concern is responsible for allowing an attacker's port scan traffic that targets HTTP to reach an intranet server from the Internet?
A Open ports and services
B Weak encryption
Unsecured protocols
D
Open permissions
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


