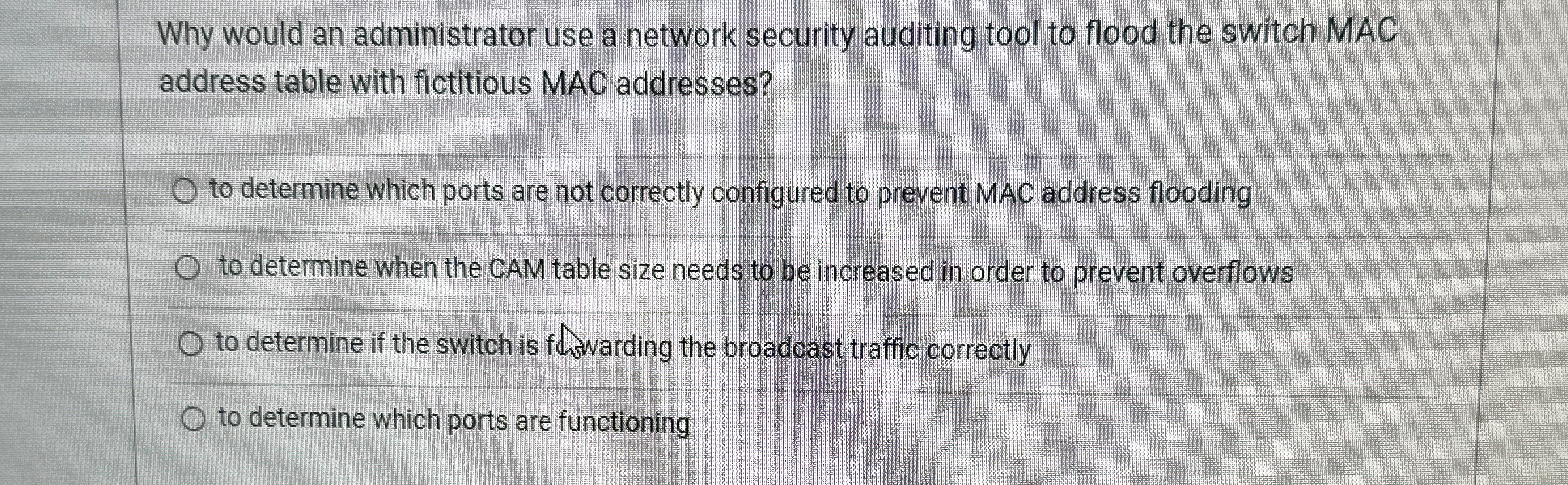
Question: Why would an administrator use a network security auditing tool to flood the switch MAC address table with fictitious MAC addresses? to determine which ports
Why would an administrator use a network security auditing tool to flood the switch MAC address table with fictitious MAC addresses? to determine which ports are not correctly configured to prevent MAC address flooding to determine when the CAM table size needs to be increased in order to prevent overflows to determine if the switch is fhavarding the broadcast traffic correctly to determine which ports are functioning
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


