Question: Write a file secret_code.c which allows you to scan in messages encrypted with Tom's Secret Code, and then print them out (ending in a
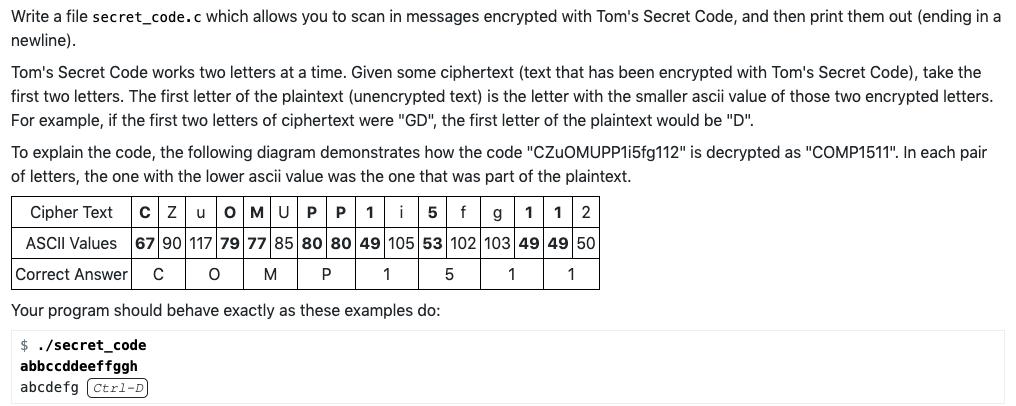
Write a file secret_code.c which allows you to scan in messages encrypted with Tom's Secret Code, and then print them out (ending in a newline). Tom's Secret Code works two letters at a time. Given some ciphertext (text that has been encrypted with Tom's Secret Code), take the first two letters. The first letter of the plaintext (unencrypted text) is the letter with the smaller ascii value of those two encrypted letters. For example, if the first two letters of ciphertext were "GD", the first letter of the plaintext would be "D". To explain the code, the following diagram demonstrates how the code "CZUOMUPP1i5fg112" is decrypted as "COMP1511". In each pair of letters, the one with the lower ascii value was the one that was part of the plaintext. Cipher Text CZUOMUPP1i5 f g 1 12 67 90 117 79 77 85 80 80 49 105 53 102 103 49 49 50 ASCII Values Correct Answer C O M P 1 5 1 1 Your program should behave exactly as these examples do: $ ./secret_code abbccddeeffggh abcdefg (ctrl-D] Write a file secret_code.c which allows you to scan in messages encrypted with Tom's Secret Code, and then print them out (ending in a newline). Tom's Secret Code works two letters at a time. Given some ciphertext (text that has been encrypted with Tom's Secret Code), take the first two letters. The first letter of the plaintext (unencrypted text) is the letter with the smaller ascii value of those two encrypted letters. For example, if the first two letters of ciphertext were "GD", the first letter of the plaintext would be "D". To explain the code, the following diagram demonstrates how the code "CZUOMUPP1i5fg112" is decrypted as "COMP1511". In each pair of letters, the one with the lower ascii value was the one that was part of the plaintext. Cipher Text CZUOMUPP1i5 f g 1 12 67 90 117 79 77 85 80 80 49 105 53 102 103 49 49 50 ASCII Values Correct Answer C O M P 1 5 1 1 Your program should behave exactly as these examples do: $ ./secret_code abbccddeeffggh abcdefg (ctrl-D]
Step by Step Solution
There are 3 Steps involved in it
Here is an implementation in C for decoding messages encrypted with Toms Secret Code c ... View full answer

Get step-by-step solutions from verified subject matter experts


