Question: Write a full java program to conduct linear search and binary search using. This program is expected to use four functions and the main
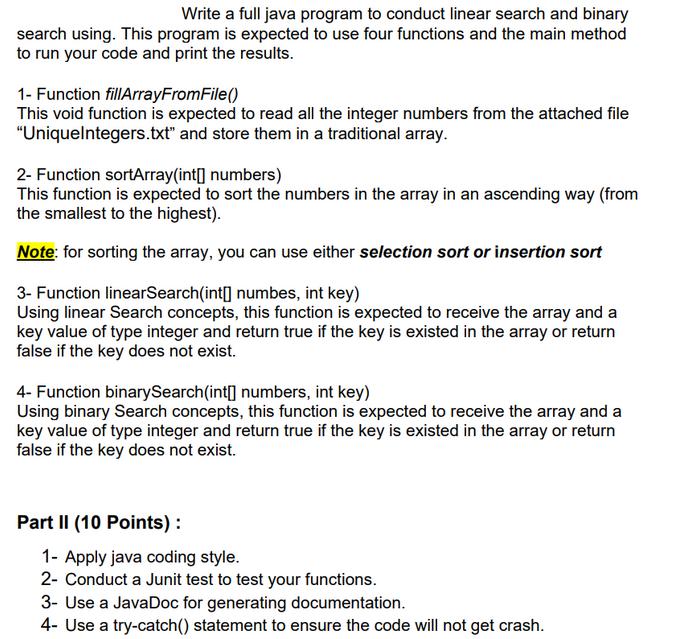
Write a full java program to conduct linear search and binary search using. This program is expected to use four functions and the main method to run your code and print the results. 1- Function fillArrayFromFile() This void function is expected to read all the integer numbers from the attached file "UniqueIntegers.txt" and store them in a traditional array. 2- Function sortArray(int[] numbers) This function is expected to sort the numbers in the array in an ascending way (from the smallest to the highest). Note: for sorting the array, you can use either selection sort or insertion sort 3- Function linearSearch(int[] numbes, int key) Using linear Search concepts, this function is expected to receive the array and a key value of type integer and return true if the key is existed in the array or return false if the key does not exist. 4- Function binarySearch(int[] numbers, int key) Using binary Search concepts, this function is expected to receive the array and a key value of type integer and return true if the key is existed in the array or return false if the key does not exist. Part II (10 Points) : 1- Apply java coding style. 2- Conduct a Junit test to test your functions. 3- Use a JavaDoc for generating documentation. 4- Use a try-catch() statement to ensure the code will not get crash.
Step by Step Solution
There are 3 Steps involved in it
Heres a breakdown of what a Java program following the requirements in your question would look like Unfortunately without the actual file UniqueInteg... View full answer

Get step-by-step solutions from verified subject matter experts


