Question: . Write a method get IntValidNumber that will get the correct value input as integer numbers from the user. The input will be validated based
.
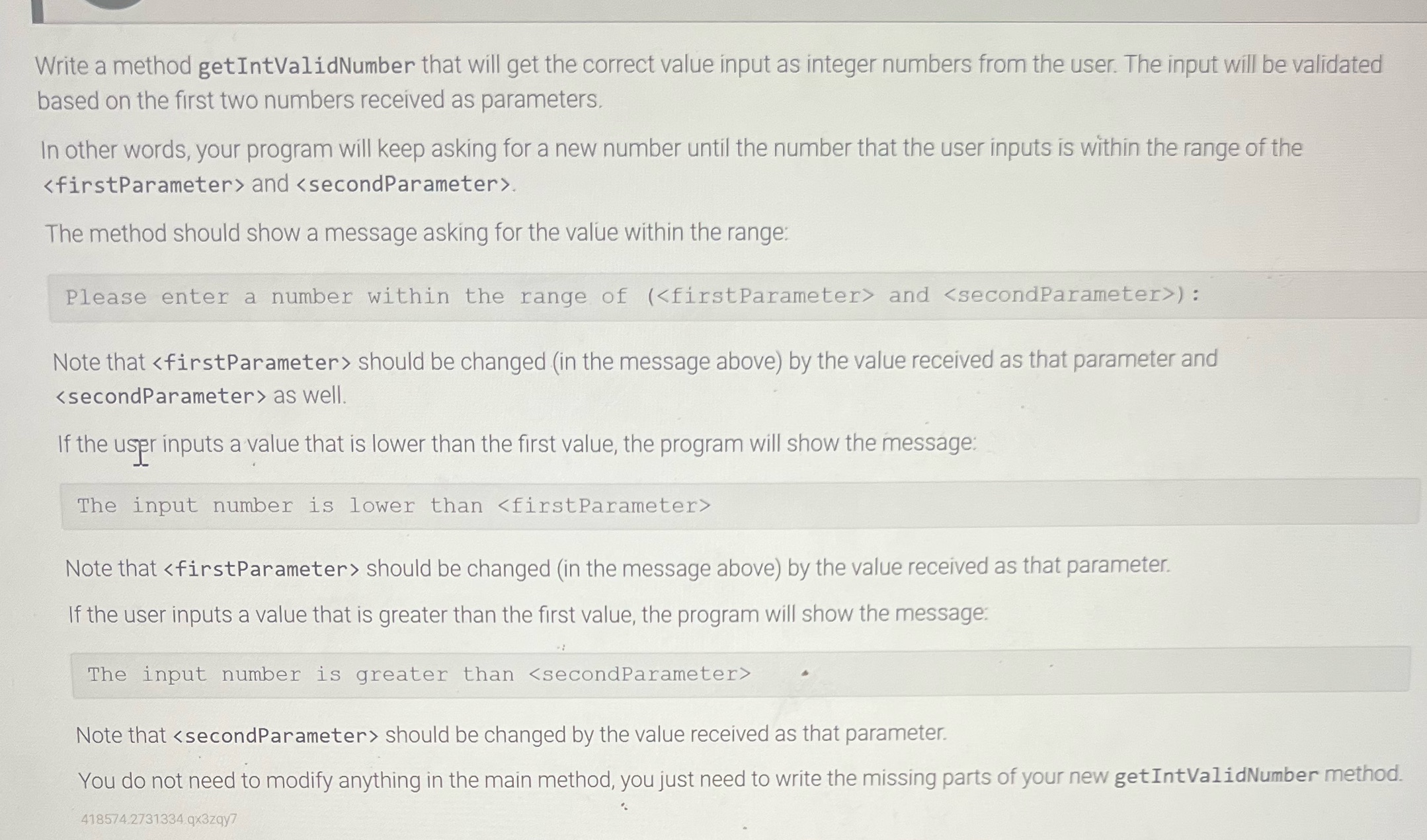
Write a method get IntValidNumber that will get the correct value input as integer numbers from the user. The input will be validated based on the first two numbers received as parameters. In other words, your program will keep asking for a new number until the number that the user inputs is within the range of the and . The method should show a message asking for the value within the range: Please enter a number within the range of ( and ): Note that should be changed (in the message above) by the value received as that parameter and as well. If the user inputs a value that is lower than the first value, the program will show the message: The input number is lower than Note that should be changed (in the message above) by the value received as that parameter. If the user inputs a value that is greater than the first value, the program will show the message: The input number is greater than Note that should be changed by the value received as that parameter. You do not need to modify anything in the main method, you just need to write the missing parts of your new get IntValidNumber method. 418574.2731334 qx3zqy7
Step by Step Solution
There are 3 Steps involved in it
Below is the getIntValidNumber method with the described functionality import javautilScanner public ... View full answer

Get step-by-step solutions from verified subject matter experts


