Question: Write (Java or C/C++) UDP programs allowing two parties to establish a secure communication channel. For simplicity, let us call the programs Host and
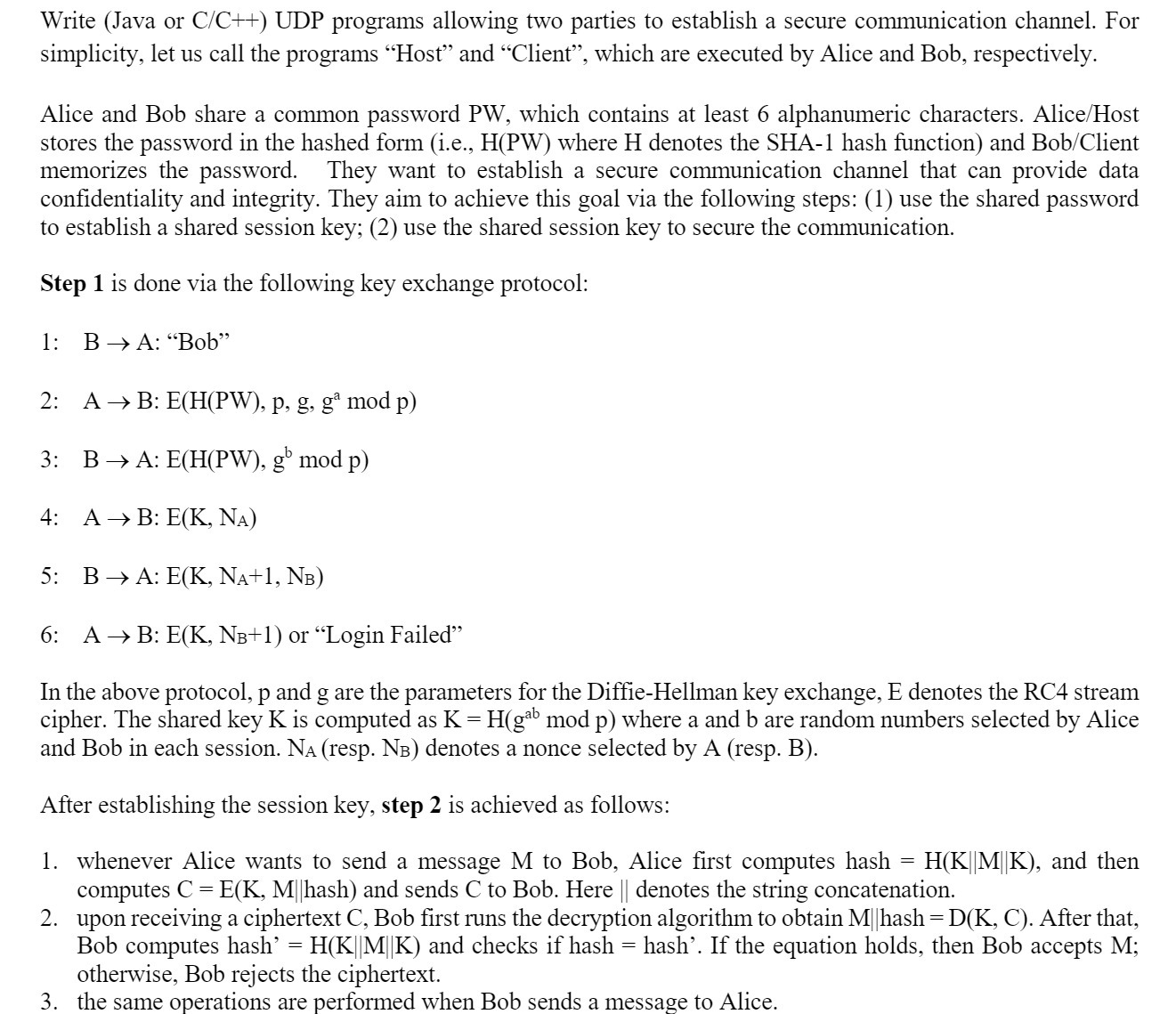
Write (Java or C/C++) UDP programs allowing two parties to establish a secure communication channel. For simplicity, let us call the programs "Host" and "Client", which are executed by Alice and Bob, respectively. Alice and Bob share a common password PW, which contains at least 6 alphanumeric characters. Alice/Host stores the password in the hashed form (i.e., H(PW) where H denotes the SHA-1 hash function) and Bob/Client memorizes the password. They want to establish a secure communication channel that can provide data confidentiality and integrity. They aim to achieve this goal via the following steps: (1) use the shared password to establish a shared session key; (2) use the shared session key to secure the communication. Step 1 is done via the following key exchange protocol: 1: BA: "Bob" 2: A B: E(H(PW), p, g, g mod p) 3: B A: E(H(PW), gb mod p) 4: AB: E(K, NA) 5: B A: E(K, NA+1, NB) 6: A B: E(K, N+1) or Login Failed" In the above protocol, p and g are the parameters for the Diffie-Hellman key exchange, E denotes the RC4 stream cipher. The shared key K is computed as K = H(gab mod p) where a and b are random numbers selected by Alice and Bob in each session. N (resp. NB) denotes a nonce selected by A (resp. B). After establishing the session key, step 2 is achieved as follows: H(K||M|K), and then E(K, M||hash) and sends C to Bob. Here || denotes the string concatenation. 1. whenever Alice wants to send a message M to Bob, Alice first computes hash computes C= 2. upon receiving a ciphertext C, Bob first runs the decryption algorithm to obtain M||hash = D(K, C). After that, Bob computes hash' = H(K||M||K) and checks if hash =hash'. If the equation holds, then Bob accepts M; otherwise, Bob rejects the ciphertext. 3. the same operations are performed when Bob sends a message to Alice. =
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


