XYZ Corporation, a leading entity in the technology industry, has recently developed a new online customer service
Question:
XYZ Corporation, a leading entity in the technology industry, has recently developed a new online customer service platform aimed at enhancing user experience and streamlining client interactions. The platform houses sensitive customer data, making it imperative for the corporation to ensure robust information security measures aligned with ISO27001 standards. As a precautionary strategy, XYZ Corporation seeks to conduct an exhaustive information security risk assessment exercise. The objective is to identify, analyze, and evaluate potential risks that could jeopardize the confidentiality, integrity, and availability of the stored data and the associated processes. This exercise is crucial to fortify the platform against unauthorized access, data breaches, and other associated risks, and to foster continuous improvement in XYZ’s information security management system. The findings from the risk assessment will be instrumental in shaping the strategic direction and implementation of potent security controls and risk mitigation strategies.
Consider that a potential risk has been identified where unauthorized access may be gained through a vulnerability in the login page of the customer service platform.
- Risk Owner: Web Security Team
- Asset/Process Affected: Login Page of Customer Service Platform
Objective: To carry out an information security risk assessment process based on the guidelines stipulated by ISO27001 under section 6.1.2.
Materials Needed:
- Risk Assessment Template
- Access to organizational assets and process information
- Computer with spreadsheet or risk assessment software
- Access to organizational security policies and criteria
Instructions:
Step 1: Establish and Maintain Information Security Risk Criteria
a. Define the risk acceptance criteria by consulting organizational policies and discussing with key stakeholders.
b. Set criteria for performing information security risk assessments, such as scope, methodology, tools, and techniques to be used.
Step 2: Ensure Consistency in Risk Assessments
a. Follow a standardized process or use consistent tools and methodologies to ensure that repeated risk assessments produce comparable results.
b. Document the methodologies and tools used for future reference.
Step 3: Identify Information Security Risks
a. Execute the risk assessment process to identify risks affecting the confidentiality, integrity, and availability of information within the organization.
b. Clearly identify and document the owners of each identified risk.
Step 4: Analyze Information Security Risks
a. For each identified risk, assess and document the potential consequences should the risk materialize.
b. Evaluate and document the likelihood of each risk’s occurrence.
c. Determine the levels of risk by calculating the potential impact and likelihood.
Step 5: Evaluate Information Security Risks
a. Compare the analyzed risks with the predefined risk criteria to ascertain whether the risks are acceptable or require treatment.
b. Prioritize the analyzed risks based on their levels and the organization’s risk acceptance criteria for further risk treatment processes.
Step 6: Documentation and Record Keeping
a. Ensure that all aspects of the risk assessment process, including criteria, identification, analysis, and evaluation, are thoroughly documented.
b. Maintain the documented information securely, ensuring that it is accessible for review, audit, and continual improvement of the risk assessment process.
Evaluation: After completing the risk assessment process, it is essential to review the results, ensuring that all steps have been followed correctly, and the information documented is accurate and comprehensive.
Notes:
- Ensure to comply with organizational policies and procedures throughout the risk assessment process.
- Maintain confidentiality and integrity of the information accessed and generated during the risk assessment.
- Continually improve and update the risk assessment process based on organizational changes, lessons learned, and emerging threats and vulnerabilities.
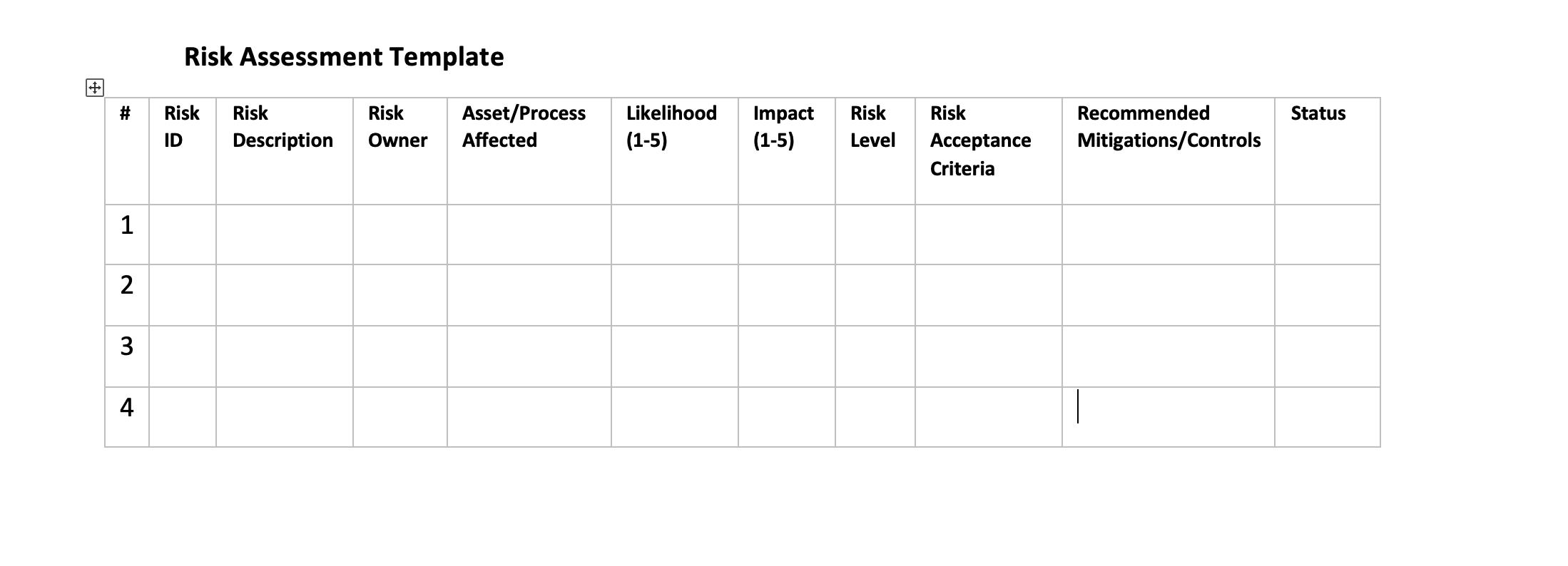
Column Descriptions:
- #: Serial number for each identified risk.
- Risk ID: A unique identifier for each risk.
- Risk Description: Detailed description of the risk, including potential threats and vulnerabilities.
- Risk Owner: Person or department responsible for managing the risk.
- Asset/Process Affected: Specific assets or processes that are impacted by the risk.
- Likelihood (1-5): A rating from 1 to 5 (1: very unlikely, 5: almost certain) representing the probability of the risk occurring.
- Impact (1-5): A rating from 1 to 5 (1: negligible, 5: severe) representing the severity of the consequences if the risk materializes.
- Risk Level: Calculation based on likelihood and impact to determine the overall risk level.
- Risk Acceptance Criteria: Criteria to decide whether the risk is acceptable or needs treatment.
- Recommended Mitigations/Controls: Suggestions to manage, mitigate, or transfer the risk.
- Status: Current status of the risk or mitigation efforts (e.g., open, closed, in-progress).

Management Accounting Information for Decision-Making and Strategy Execution
ISBN: 978-0137024971
6th Edition
Authors: Anthony A. Atkinson, Robert S. Kaplan, Ella Mae Matsumura, S. Mark Young