Question: You are working on a program to add security to a database that consists of key-value pairs. You already have the database class, and the
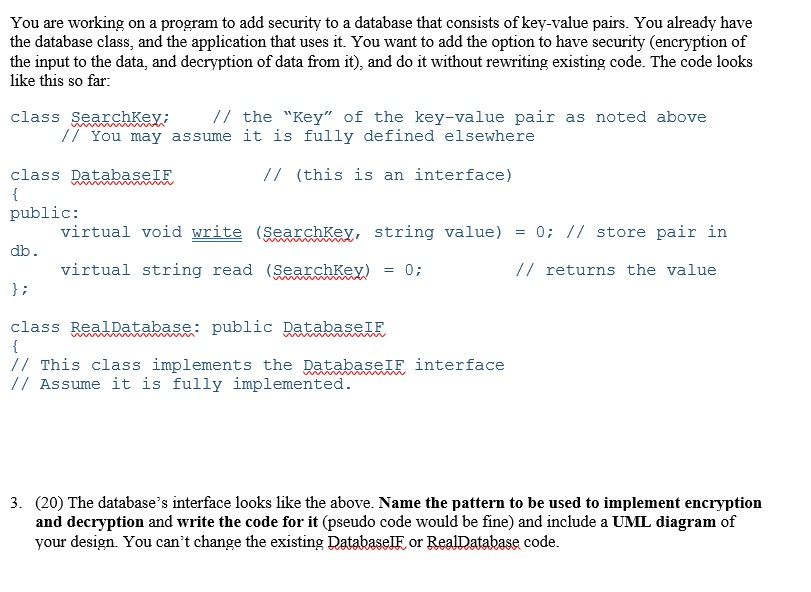
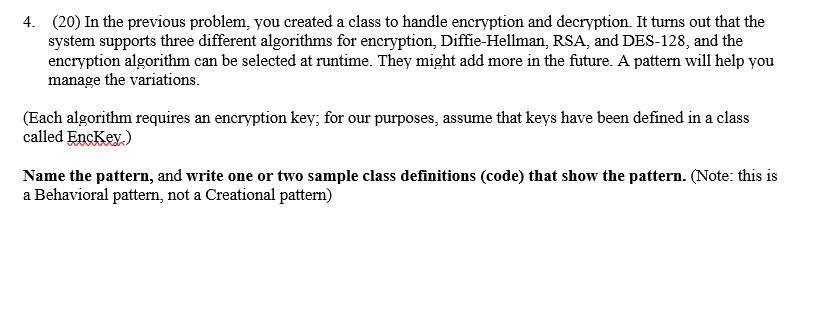
You are working on a program to add security to a database that consists of key-value pairs. You already have the database class, and the application that uses it. You want to add the option to have security (encryption of the input to the data, and decryption of data from it), and do it without rewriting existing code. The code looks like this so far: class Seaxchkex /the "Key" of the key-value pair as noted above /7 You may assume it is fully defined elsewhere // (this is an interface) class DatabaseIF public: db virtual void write (searchKey, string value) = 0; // store pair in virtual string read (SearchKex) = 0; // returns the value class RealDatabase: public DatabaseIF / This class implements the DatabaseIE interface // Assume it is fully implemented. 3. (20) The database's interface looks like the above. Name the pattern to be used to implement encryption and decryption and write the code for it (pseudo code would be fine) and include a UML diagram of your design. You can't change the existing Databaseor Rea!Database code. You are working on a program to add security to a database that consists of key-value pairs. You already have the database class, and the application that uses it. You want to add the option to have security (encryption of the input to the data, and decryption of data from it), and do it without rewriting existing code. The code looks like this so far: class Seaxchkex /the "Key" of the key-value pair as noted above /7 You may assume it is fully defined elsewhere // (this is an interface) class DatabaseIF public: db virtual void write (searchKey, string value) = 0; // store pair in virtual string read (SearchKex) = 0; // returns the value class RealDatabase: public DatabaseIF / This class implements the DatabaseIE interface // Assume it is fully implemented. 3. (20) The database's interface looks like the above. Name the pattern to be used to implement encryption and decryption and write the code for it (pseudo code would be fine) and include a UML diagram of your design. You can't change the existing Databaseor Rea!Database code
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


