Your task is to draw a dataflow diagram for the following web application. Application Description: The...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
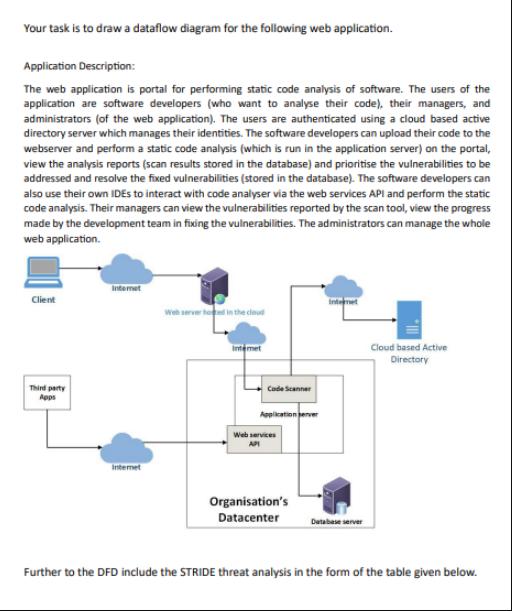
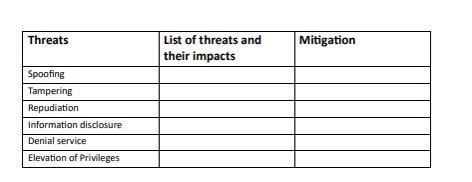
Your task is to draw a dataflow diagram for the following web application. Application Description: The web application is portal for performing static code analysis of software. The users of the application are software developers (who want to analyse their code), their managers, and administrators (of the web application). The users are authenticated using a cloud based active directory server which manages their identities. The software developers can upload their code to the webserver and perform a static code analysis (which is run in the application server) on the portal, view the analysis reports (scan results stored in the database) and prioritise the vulnerabilities to be addressed and resolve the fixed vulnerabilities (stored in the database). The software developers can also use their own IDEs to interact with code analyser via the web services API and perform the static code analysis. Their managers can view the vulnerabilities reported by the scan tool, view the progress made by the development team in fixing the vulnerabilities. The administrators can manage the whole web application. Client Third party Apps Internet Internet Web servered in the cloud Internet Code Scanner Application server Web services Organisation's Datacenter Internet Database server Cloud based Active Directory Further to the DFD include the STRIDE threat analysis in the form of the table given below. Threats Spoofing Tampering Repudiation Information disclosure Denial service Elevation of Privileges List of threats and their impacts Mitigation Your task is to draw a dataflow diagram for the following web application. Application Description: The web application is portal for performing static code analysis of software. The users of the application are software developers (who want to analyse their code), their managers, and administrators (of the web application). The users are authenticated using a cloud based active directory server which manages their identities. The software developers can upload their code to the webserver and perform a static code analysis (which is run in the application server) on the portal, view the analysis reports (scan results stored in the database) and prioritise the vulnerabilities to be addressed and resolve the fixed vulnerabilities (stored in the database). The software developers can also use their own IDEs to interact with code analyser via the web services API and perform the static code analysis. Their managers can view the vulnerabilities reported by the scan tool, view the progress made by the development team in fixing the vulnerabilities. The administrators can manage the whole web application. Client Third party Apps Internet Internet Web servered in the cloud Internet Code Scanner Application server Web services Organisation's Datacenter Internet Database server Cloud based Active Directory Further to the DFD include the STRIDE threat analysis in the form of the table given below. Threats Spoofing Tampering Repudiation Information disclosure Denial service Elevation of Privileges List of threats and their impacts Mitigation
Expert Answer:
Answer rating: 100% (QA)
Since Im not able to create visual content like diagrams Ill explain to you how to approach the drawing of a data flow diagram DFD for the web application and then how to fill out the STRIDE threat an... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these computer network questions
-
Explain THREE (3) differences between takaful and conventional insurance using your own word.
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
How much time does it take to call functions such as Math. \(\sin ()\), Math. \(\log ()\), and Math.sqrt()?
-
What is the annual interest amount for a $1,000 bond that pays 7 3 / 4 percent interest?
-
Jessica Brody is considering purchasing a home for \($200\),000 and flipping it in three years. The expected rent is \($1\),500/month and expenses are \($150\)/month. Mrs. Brody anticipates a rental...
-
Explain the circumstances under which a person should choose a regular checking account, activity checking account, or interest-bearing checking account.
-
You have been assigned to the first audit of the Chicago Company for the year ending March 31, 2011. Accounts receivable were confirmed on December 31, 2010, and at that date the receivables...
-
Henderson Co. granted its employees options for 70,000, $2 par common shares on January 1, 2017, when the share market price was $10 compared to the option exercise price of $11. The options cannot...
-
XYZ is a calendar-year corporation that began business on January 1, 2020. For the year, it reported the following information in its current-year audited income statement. Notes with important tax...
-
Using the information given here, what is the price-earnings ratio for DEF Company?) Earnings $100,000 Number of shares outstanding = 50,000 Share price = $40 Book value per share = $8
-
You are planning to renew your car in eight years from now. The new car is expected to cost $50,000 and you believe that your old car would sell for $10,000 at that time. If you are going to make...
-
What is relational coordination? How do culture and input from managers affect relational coordination?
-
In the unit readings and textbook, you have read much about the concepts of potential and kinetic energy and how they relate to work being performed. discuss how these two types of energy differ...
-
1. Why is positive culture important in the organization? 2. Briefly explain the leadership skills that a leader of an organization should possess
-
EXplain the importance of managing culture abd inclusion in the contemporary organisation
-
With the shift from an employer-interest model to a more employee-interest model with respect to workplace ethics, it is important for management to have an appreciation of the major ethical themes...
-
X-1 Find the domain of the function f(x) : x 1 2 - O (-00, -1) U (-1, ) O (-00, 1) U (1, ) O -00, -1) U (-1, 1) U (1, 0) O (- 1, 1)
-
I. Comprehend that symmetric encryption is also known as public-key encryption. II. Explain that symmetric encryption uses a single key to encrypt and decrypt, but asymmetric encryption uses two...
-
Establish that security analysts are often known as security technicians, security architects, and/or security engineers. Examine the core duties of security analysts. Based on the need, they are...
-
Compare and contrast the two most commonly used approaches to information security implementation: bottom-up and top-down. Bottom-up approaches implement security policies and/or policies from the...
-
A companys balance sheet appears as follows: Required: (a) If 10,000 of the ordinary shares were purchased at par, there being no new issue of shares for the purpose, show the journal entries to...
-
Some years ago M plc had issued 375,000 of 10 per cent debentures 2006/2010 at par. The terms of the issue allow the company the right to repurchase these debentures for cancellation at or below par,...
-
Debentures of 30,000 are issued on 1 January 2003. Redemption is to take place, on equal terms, four years later. The company decides to put aside an equal amount to be invested at 5 per cent which...

Study smarter with the SolutionInn App


