Question: Figure 31.9 in the text shows that DES creates 16 different 48-bit keys, one for each round. Why do we need 16 different keys? Why
Figure 31.9 in the text shows that DES creates 16 different 48-bit keys, one for each round. Why do we need 16 different keys? Why can€™t we use the same key in each round?
Figure 31.9
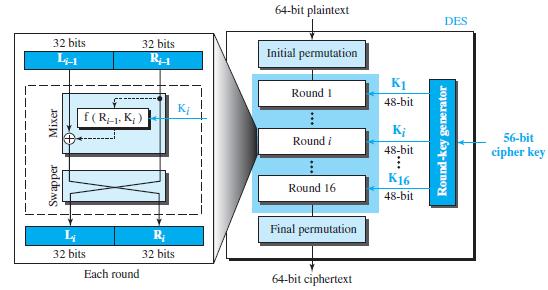
64-bit plaintext DES 32 bits 32 bits 14-1 Initial permutation K1 Round 1 48-bit K f(R-1, K; ) K; Round i 56-bit 48-bit cipher key K16 Round 16 48-bit Final permutation R; 32 bits 32 bits Each round 64-bit ciphertext
Step by Step Solution
3.29 Rating (164 Votes )
There are 3 Steps involved in it
If we apply the same key to all rounds all rounds are t... View full answer

Get step-by-step solutions from verified subject matter experts


