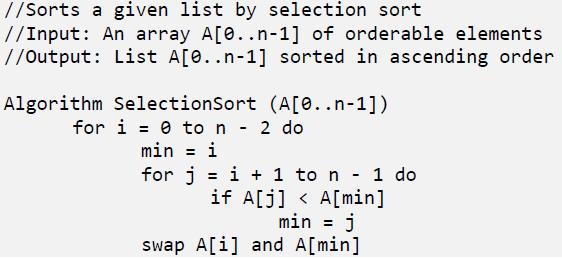
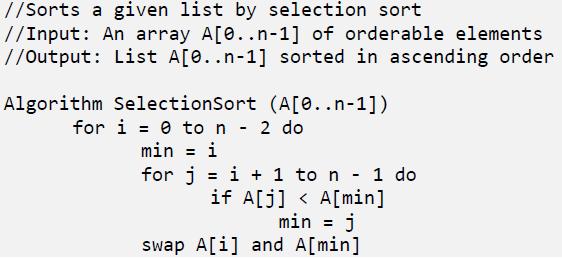
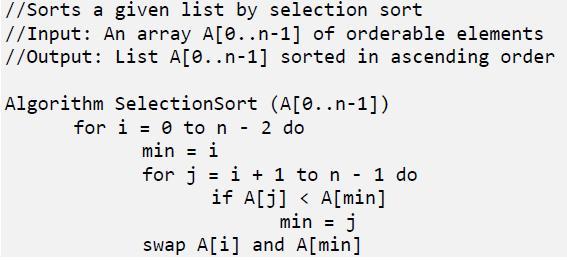
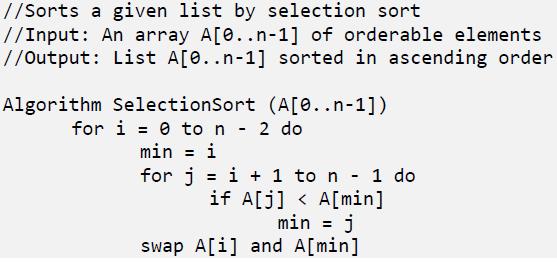
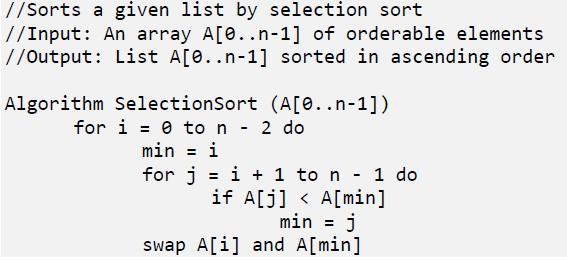
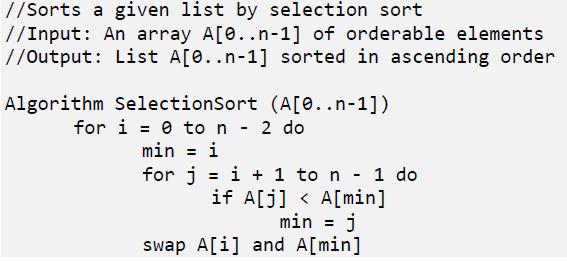
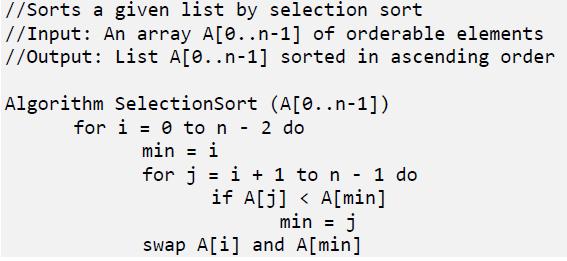
Problems Solving In Data Structures And Algorithms Using C++ 2nd Edition Hemant Jain - Solutions
Unlock the full potential of your studies with our comprehensive guide to "Problems Solving In Data Structures And Algorithms Using C++ 2nd Edition" by Hemant Jain. Access a range of resources including an online answers key and a detailed solution manual to enhance your learning experience. Dive into solutions PDF and explore solved problems with questions and answers designed to assist your understanding. Our test bank provides chapter solutions, while step-by-step answers offer clarity on every topic. Benefit from the instructor manual and textbook resources available for free download, ensuring you have all the tools needed for academic success.
![]()
![]() New Semester Started
Get 50% OFF
Study Help!
--h --m --s
Claim Now
New Semester Started
Get 50% OFF
Study Help!
--h --m --s
Claim Now
![]()
![]()