Question: Modify, compile, and test the client program in Table 25.17 and the server program in Table 25.16 to simulate a local DNS client and server.
Modify, compile, and test the client program in Table 25.17 and the server program in Table 25.16 to simulate a local DNS client and server. The server has a short table made of two columns, domain name and IP address. The client can send two types of requests: normal and reverse. The normal request is a string in the format “N:domain name”; the reverse request is in the format “R:IP address”. The server responds with either the IP address, the domain name, or the message “Not found.”
Table 25.16
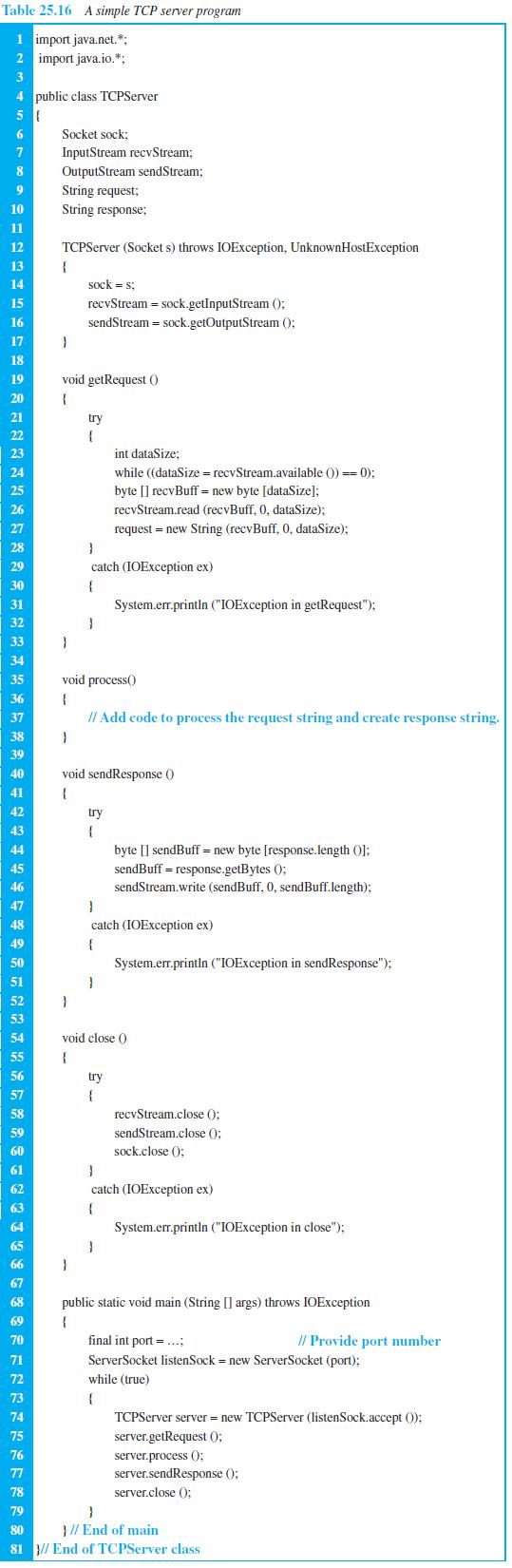
Table 25.17
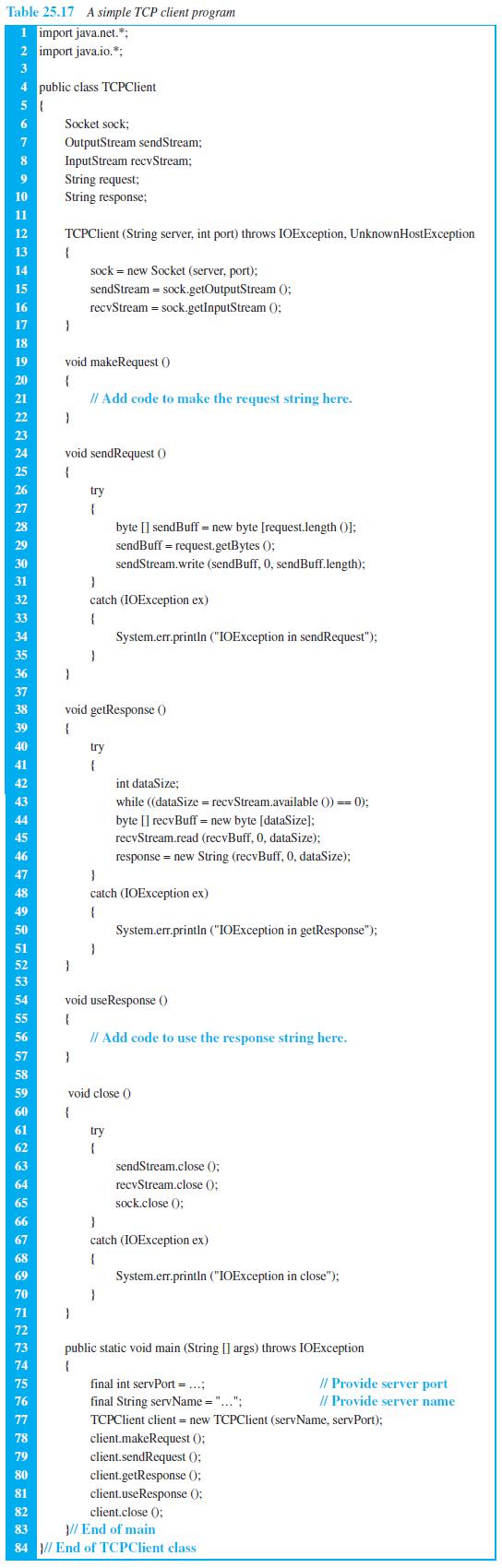
Table 25.16 A simple TCP server program 1 import java.net.*: 2 import java.io.*; 3 4 public class TCPServer 6. Socket sock; InputStream recvStream; OutputStream sendStream; 7 8 String request; 10 String response; 11 12 TCPServer (Socket s) throws IOException, UnknownHostException 13 14 sock = s; recvStream = sock.getInputStream (): sendStream = sock.getOutputStream (); 15 16 17 18 19 void getRequest () 20 21 try 22 { int dataSize; 23 24 while ((dataSize = recvStream.available () ==0); 25 byte [] recvBuff = new byte [dataSize]; 26 recvStream.read (recvBuff, 0, dataSize): 27 request = new String (recvBuff, 0, dataSize); 28 29 catch (IOException ex) 30 31 System.err.println ("IOException in getRequest"); 32 33 34 35 void process() 36 { 37 // Add code to process the request string and create response string. 38 39 40 void sendResponse () 41 42 try 43 { byte [] sendBuff = new byte [response.length (O): sendBuff = response.getBytes (); 44 45 46 sendStream.write (sendBuff, 0, sendBuff.length); 47 48 catch (IOException ex) 49 50 System.er.println ("IOException in sendResponse"); 51 52 53 54 void close () 55 56 try 57 58 recvStream.close (); 59 sendStream.close (); 60 sock.close (); 61 62 catch (IOException ex) 63 64 System.err.printin ("IOException in close"); 65 66 67 68 public static void main (String [] args) throws IOException 69 { 70 final int port = ...; // Provide port number 71 ServerSocket listenSock = new ServerSocket (port); 72 while (true) 73 74 TCPServer server = new TCPServer (listenSock.accept (): 75 server.getRequest 0; 76 server.process (; server.sendResponse (); 77 78 server.close (); 79 80 } // End of main 81 }// End of TCPServer class
Step by Step Solution
3.57 Rating (171 Votes )
There are 3 Steps involved in it
This assignment shows how we can use the TCP client and server program defined in the text to s... View full answer

Get step-by-step solutions from verified subject matter experts


