Question: For these problems, the table holds MIPS assembly code fragments. You will be asked to evaluate each of the code fragments, familiarizing you with the
For these problems, the table holds MIPS assembly code fragments. You will be asked to evaluate each of the code fragments, familiarizing you with the different MIPS branch instructions.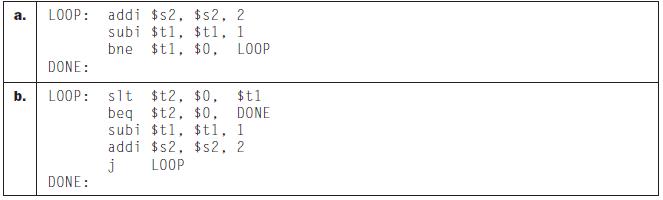
For the loops written in MIPS assembly above, assume that the register $t1 is initialized to the value N. How many MIPS instructions are executed?
a. b. LOOP: addi $s2, $s2, 2 subi $t1, $t1, 1 bne $t1, $0. LOOP DONE: LOOP: DONE: $t1 slt $t2, $0, beq $t2, $0, DONE subi $t1, $t1, 1 addi $s2, $s2, 2 j LOOP
Step by Step Solution
3.46 Rating (156 Votes )
There are 3 Steps involved in it
Loop A addi s2 s2 2 subi tl tl 1 bne t1 0 LOOP DONE Loop B slt t2 0 tl beq t2 0 DONE subi tl tl 1 ad... View full answer

Get step-by-step solutions from verified subject matter experts


