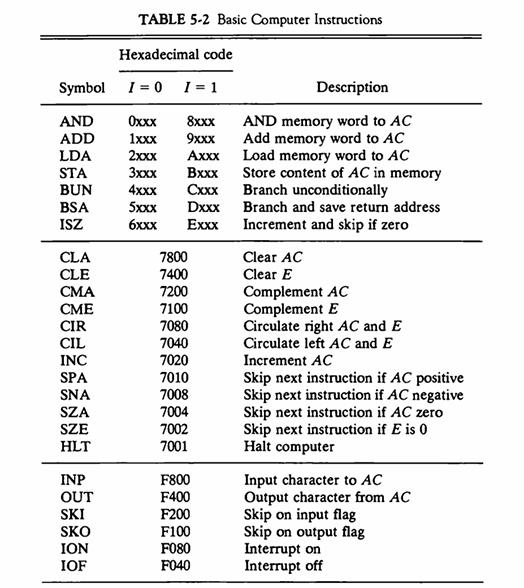
Question: Consider the instruction formats of the basic computer shown in Fig. 5-5 and the list of instructions given in Table 5-2. For each of the
Consider the instruction formats of the basic computer shown in Fig. 5-5 and the list of instructions given in Table 5-2. For each of the following 16-bit instructions, give the equivalent four-digit hexadecimal code and explain in your own words what it is that the instruction is going to perform.
a. 0001 0000 0010 0100
b. 1011 0001 0010 0100
c. 0111 0000 0010 0000
Fig. 5-5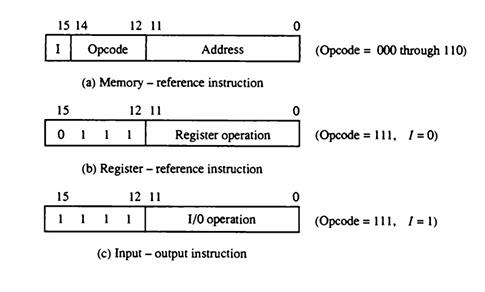
Table 5-2
15 14 I 15 0 15 1 12 11 Opcode (a) Memory-reference instruction 12 11 1 1 1 Register operation (b) Register - reference instruction 12 11 1 Address 1/0 operation (c) Input-output instruction 0 (Opcode = 000 through 110) (Opcode = 111, 1 = 0) (Opcode = 111, 1=1)
Step by Step Solution
3.41 Rating (170 Votes )
There are 3 Steps involved in it
We must first comprehend the syntax of the instructions before mapping the provided 16bit instructio... View full answer

Get step-by-step solutions from verified subject matter experts


