1. Determine if the ITGC listed is a preventive or a detective and corrective control. ITGC...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
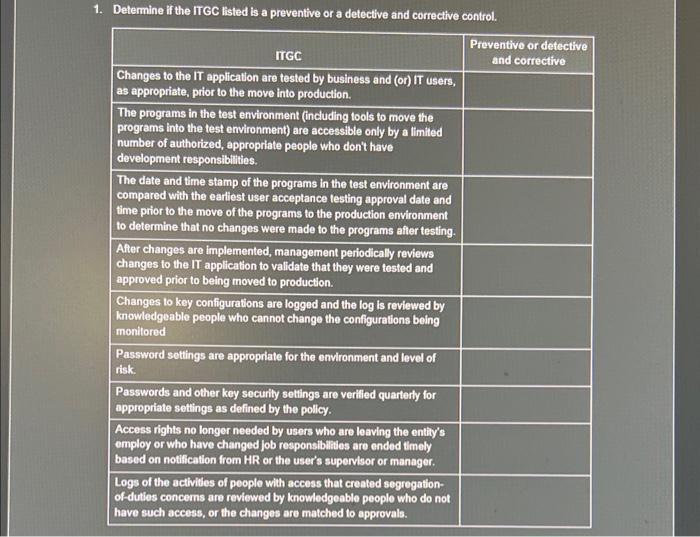
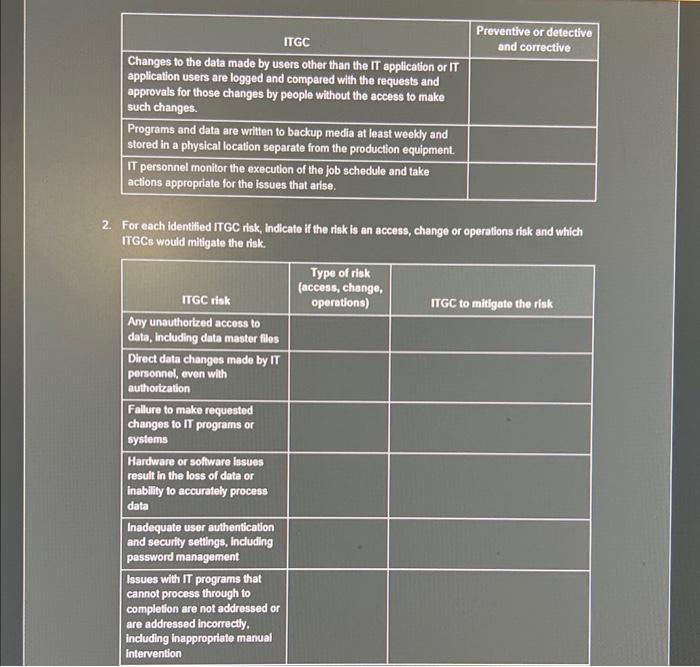
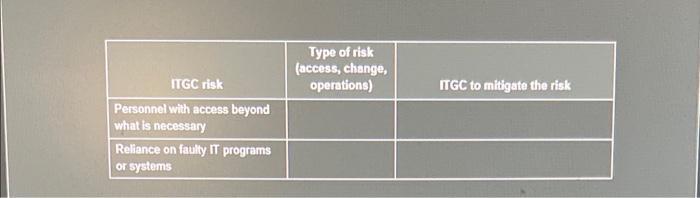
1. Determine if the ITGC listed is a preventive or a detective and corrective control. ITGC Changes to the IT application are tested by business and (or) IT users, as appropriate, prior to the move into production. The programs in the test environment (including tools to move the programs into the test environment) are accessible only by a limited number of authorized, appropriate people who don't have development responsibilities. The date and time stamp of the programs in the test environment are compared with the earliest user acceptance testing approval date and time prior to the move of the programs to the production environment to determine that no changes were made to the programs after testing. After changes are implemented, management periodically reviews changes to the IT application to validate that they were tested and approved prior to being moved to production. Changes to key configurations are logged and the log is reviewed by knowledgeable people who cannot change the configurations being monitored Password settings are appropriate for the environment and level of risk. Passwords and other key security settings are verified quarterly for appropriate settings as defined by the policy. Access rights no longer needed by users who are leaving the entity's employ or who have changed job responsibilities are ended timely based on notification from HR or the user's supervisor or manager. Logs of the activities of people with access that created segregation- of-duties concerns are reviewed by knowledgeable people who do not have such access, or the changes are matched to approvals. Preventive or detective and corrective ITGC Changes to the data made by users other than the IT application or IT application users are logged and compared with the requests and approvals for those changes by people without the access to make such changes. Programs and data are written to backup media at least weekly and stored in a physical location separate from the production equipment. IT personnel monitor the execution of the job schedule and take actions appropriate for the issues that arise. 2. For each identified ITGC risk, indicate if the risk is an access, change or operations risk and which ITGCS would mitigate the risk. ITGC risk Any unauthorized access to data, including data master files Direct data changes made by IT personnel, even with authorization Failure to make requested changes to IT programs or systems Hardware or software issues result in the loss of data or inability to accurately process data Inadequate user authentication and security settings, including password management Issues with IT programs that cannot process through to completion are not addressed or are addressed incorrectly. including Inappropriate manual intervention Preventive or detective and corrective Type of risk (access, change, operations) ITGC to mitigate the risk ITGC risk Personnel with access beyond what is necessary Reliance on faulty IT programs or systems Type of risk (access, change, operations) ITGC to mitigate the risk 1. Determine if the ITGC listed is a preventive or a detective and corrective control. ITGC Changes to the IT application are tested by business and (or) IT users, as appropriate, prior to the move into production. The programs in the test environment (including tools to move the programs into the test environment) are accessible only by a limited number of authorized, appropriate people who don't have development responsibilities. The date and time stamp of the programs in the test environment are compared with the earliest user acceptance testing approval date and time prior to the move of the programs to the production environment to determine that no changes were made to the programs after testing. After changes are implemented, management periodically reviews changes to the IT application to validate that they were tested and approved prior to being moved to production. Changes to key configurations are logged and the log is reviewed by knowledgeable people who cannot change the configurations being monitored Password settings are appropriate for the environment and level of risk. Passwords and other key security settings are verified quarterly for appropriate settings as defined by the policy. Access rights no longer needed by users who are leaving the entity's employ or who have changed job responsibilities are ended timely based on notification from HR or the user's supervisor or manager. Logs of the activities of people with access that created segregation- of-duties concerns are reviewed by knowledgeable people who do not have such access, or the changes are matched to approvals. Preventive or detective and corrective ITGC Changes to the data made by users other than the IT application or IT application users are logged and compared with the requests and approvals for those changes by people without the access to make such changes. Programs and data are written to backup media at least weekly and stored in a physical location separate from the production equipment. IT personnel monitor the execution of the job schedule and take actions appropriate for the issues that arise. 2. For each identified ITGC risk, indicate if the risk is an access, change or operations risk and which ITGCS would mitigate the risk. ITGC risk Any unauthorized access to data, including data master files Direct data changes made by IT personnel, even with authorization Failure to make requested changes to IT programs or systems Hardware or software issues result in the loss of data or inability to accurately process data Inadequate user authentication and security settings, including password management Issues with IT programs that cannot process through to completion are not addressed or are addressed incorrectly. including Inappropriate manual intervention Preventive or detective and corrective Type of risk (access, change, operations) ITGC to mitigate the risk ITGC risk Personnel with access beyond what is necessary Reliance on faulty IT programs or systems Type of risk (access, change, operations) ITGC to mitigate the risk
Expert Answer:
Answer rating: 100% (QA)
Answer First the necessary response 1 manage the process of transformation 2 ... View the full answer

Related Book For 

Auditing and Assurance Services
ISBN: 978-0077862343
6th edition
Authors: Timothy Louwers, Robert Ramsay, David Sinason, Jerry Straws
Posted Date:
Students also viewed these general management questions
-
A risk management program must be implemented and periodically monitored to be effective. This step requires the preparation of a risk management policy statement. The cooperation of other...
-
In many industrial production processes, measurements are made periodically on critical characteristics to ensure that the process is operating properly. Observations vary from item to item being...
-
A password may become known to other users in a variety of ways. Is there a simple method for detecting that such an event has occurred? Explain your answer.
-
A strain relaxation test and a creep test are being conducted on a mouse Achilles tendon. If a strain of \epsi 0 = 60% is applied in the strain relaxation test and a stress of \ sigma 0 = 1 MPa is...
-
Survivor, Inc., an all-equity firm, has eight shares of stock outstanding. Yesterday, the firms assets consisted of nine ounces of platinum, currently worth $1,750 per ounce. Today, the company...
-
C. N. Itall has been a systems analyst for Tun-L-Vision Corporation for many years. When you came on board as part of the systems analysis team and suggested prototyping as part of the SDLC for a...
-
Consider the following cash flow profile and assume MARR is 10 percent/year. a. Determine the IRR(s) for this project. b. Is this project economically attractive? EOY 0 1 2 3 4 5 6 NCF -$101 $411...
-
A.J's Wildlife Emporium manufactures two unique bird feeders (Deluxe and Super Duper) that are manufacture and assembled in up to three different workstations (X, Y, Z) using a small batch process....
-
Peanut Company acquired 80 percent of Snoopy Company's outstanding common stock for $276,800 on January 1, 20X8, when the book value of Snoopy's net assets was equal to $346,000. Peanut uses the...
-
Parent Co. owns 75% of Sub Co. and uses the cost method to account for its investment. The following are summarized income statements for the year ended December 31, Year 7. Additional Information: ...
-
80) On January 1, 2020, Juniper Company sells $2 million of 8% bonds at face value with interest to be paid at the end of each year. Prepare the journal entries and show any changes to assets,...
-
While out at lunch, two Government employees, Rishi and Martha, discuss confidential details about a vendor who bid on a recent procurement. Their conversation is overheard by a competing vendor who...
-
In August of 2019, the Parliamentary Joint Committee on Corporations and Financial Services commenced an inquiry into auditing regulation in Australia. This inquiry was instigated by the ASIC...
-
The sales of a new magazine are predicted by the equation St27t+216 + 1990 where S is the number of magazines sold in week t. Find the first values of t (with t > 0) which generate local maximum and...
-
What are skills we will use in the future to work with a person to empower them from a strength- based perspective. Explain briefly.
-
A chemical tanker truck crashes into a flooded, abandoned quarry (no soil or sediment on the bottom). It was carrying 1000 kg of benzene which is all released into the quarry and quickly becomes a...
-
What is the interest income/revenue earned on 12/31/20X1? What is the Fair Value Adjustment journal entry on 12/31/20X1 to mark the investment to market (after your interest payment), if any is made?...
-
Drainee purchases direct materials each month. Its payment history shows that 65% is paid in the month of purchase with the remaining balance paid the month after purchase. Prepare a cash payment...
-
What are some of the ratios that can be used in preliminary analytical procedures?
-
Orange is a public entity whose shares are traded on a national exchange. A Public Company Accounting Oversight Board inspection revealed a deficiency in audits conducted by Oranges auditor, LeGrow....
-
Which of the following statements best describes auditors responsibility for detecting a clients noncompliance with a law or regulation? a. The responsibility for detecting noncompliance exactly...
-
Which mechanism of bacterial genetic transfer does not require recombination with the bacterial chromosome?
-
Explain why small deletions and duplications are less likely than large ones to have a detrimental effect on an individuals phenotype. If a small deletion within a single chromosome happens to have a...
-
Explain why inversions and reciprocal translocations do not usually cause a phenotypic effect. Then explain how they can do so in certain cases.

Study smarter with the SolutionInn App