Question: 1. Explain what SQL injections are and what they can do. (5 marks) 2. Find a video on YouTube (and provide the link) or
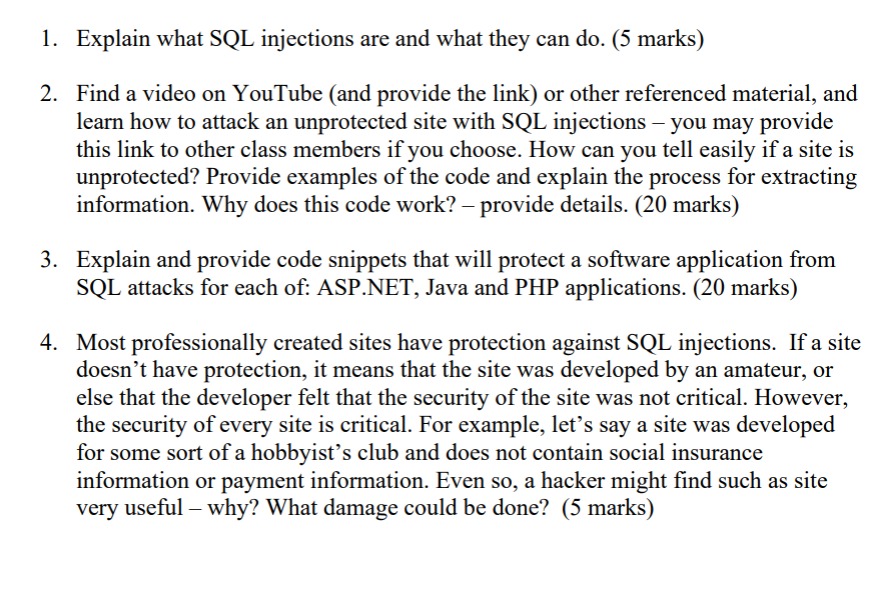
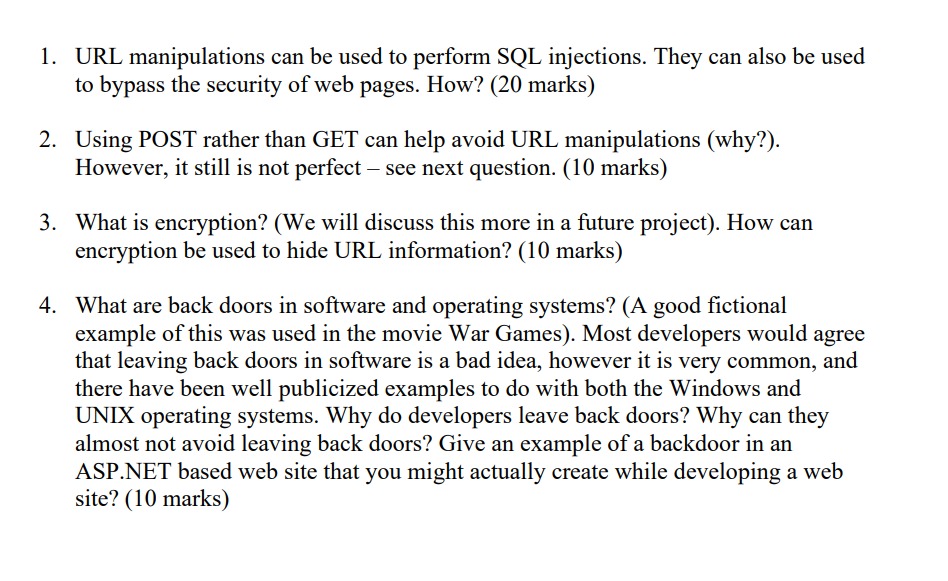
1. Explain what SQL injections are and what they can do. (5 marks) 2. Find a video on YouTube (and provide the link) or other referenced material, and learn how to attack an unprotected site with SQL injections - you may provide this link to other class members if you choose. How can you tell easily if a site is unprotected? Provide examples of the code and explain the process for extracting information. Why does this code work? - provide details. (20 marks) 3. Explain and provide code snippets that will protect a software application from SQL attacks for each of: ASP.NET, Java and PHP applications. (20 marks) 4. Most professionally created sites have protection against SQL injections. If a site doesn't have protection, it means that the site was developed by an amateur, or else that the developer felt that the security of the site was not critical. However, the security of every site is critical. For example, let's say a site was developed for some sort of a hobbyist's club and does not contain social insurance information or payment information. Even so, a hacker might find such as site very useful - why? What damage could be done? (5 marks) 1. URL manipulations can be used to perform SQL injections. They can also be used to bypass the security of web pages. How? (20 marks) 2. Using POST rather than GET can help avoid URL manipulations (why?). However, it still is not perfect - see next question. (10 marks) 3. What is encryption? (We will discuss this more in a future project). How can encryption be used to hide URL information? (10 marks) 4. What are back doors in software and operating systems? (A good fictional example of this was used in the movie War Games). Most developers would agree that leaving back doors in software is a bad idea, however it is very common, and there have been well publicized examples to do with both the Windows and UNIX operating systems. Why do developers leave back doors? Why can they almost not avoid leaving back doors? Give an example of a backdoor in an ASP.NET based web site that you might actually create while developing a web site? (10 marks)
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


