Question: 1. Name the folders located on C., which are common to all Windows distributions 2. What is the purpose of the i386 folder? 3. On
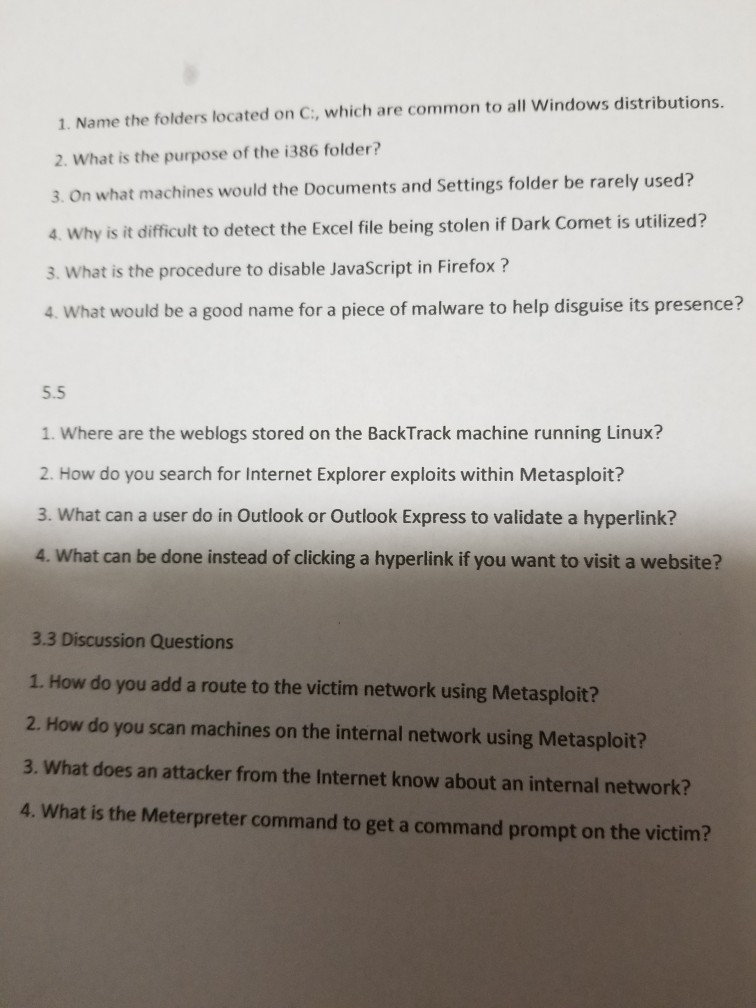
1. Name the folders located on C., which are common to all Windows distributions 2. What is the purpose of the i386 folder? 3. On what machines would the Documents and Settings folder be rarely used? 4. Why is it diffiult to detect the Excel file being stolen if Dark Comet is utilized? 3. What is the procedure to disable JavaScript in Firefox? 4. What would be a good name for a piece of malware to help disguise its presence? 5.5 1. Where are the weblogs stored on the BackTrack machine running Linux? 2. How do you search for Internet Explorer exploits within Metasploit? 3. What can a user do in Outlook or Outlook Express to validate a hyperlink? 4. What can be done instead of clicking a hyperlink if you want to visit a website? 3.3 Discussion Questions 1. How do you add a route to the victim network using Metasploit? 2. How do you scan machines on the internal network using Metasploit? 3. What does an attacker from the Internet know about an internal network? 4. What is the Meterpreter command to get a command prompt on the victim? 1. Name the folders located on C., which are common to all Windows distributions 2. What is the purpose of the i386 folder? 3. On what machines would the Documents and Settings folder be rarely used? 4. Why is it diffiult to detect the Excel file being stolen if Dark Comet is utilized? 3. What is the procedure to disable JavaScript in Firefox? 4. What would be a good name for a piece of malware to help disguise its presence? 5.5 1. Where are the weblogs stored on the BackTrack machine running Linux? 2. How do you search for Internet Explorer exploits within Metasploit? 3. What can a user do in Outlook or Outlook Express to validate a hyperlink? 4. What can be done instead of clicking a hyperlink if you want to visit a website? 3.3 Discussion Questions 1. How do you add a route to the victim network using Metasploit? 2. How do you scan machines on the internal network using Metasploit? 3. What does an attacker from the Internet know about an internal network? 4. What is the Meterpreter command to get a command prompt on the victim
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


