1- Stealing personal information from trash cans is called as --- 2- Observing users as they...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
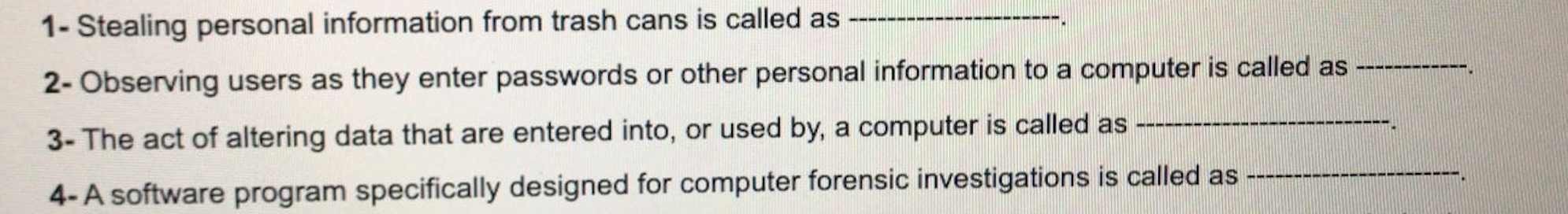
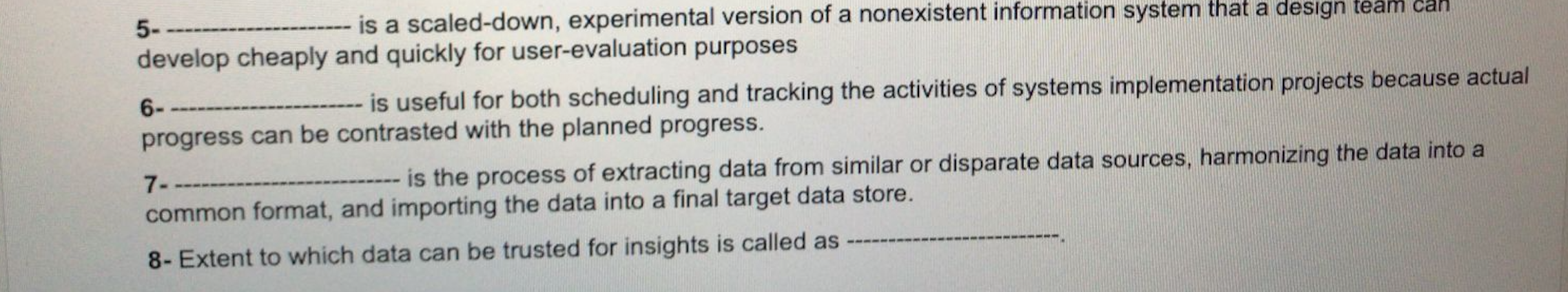
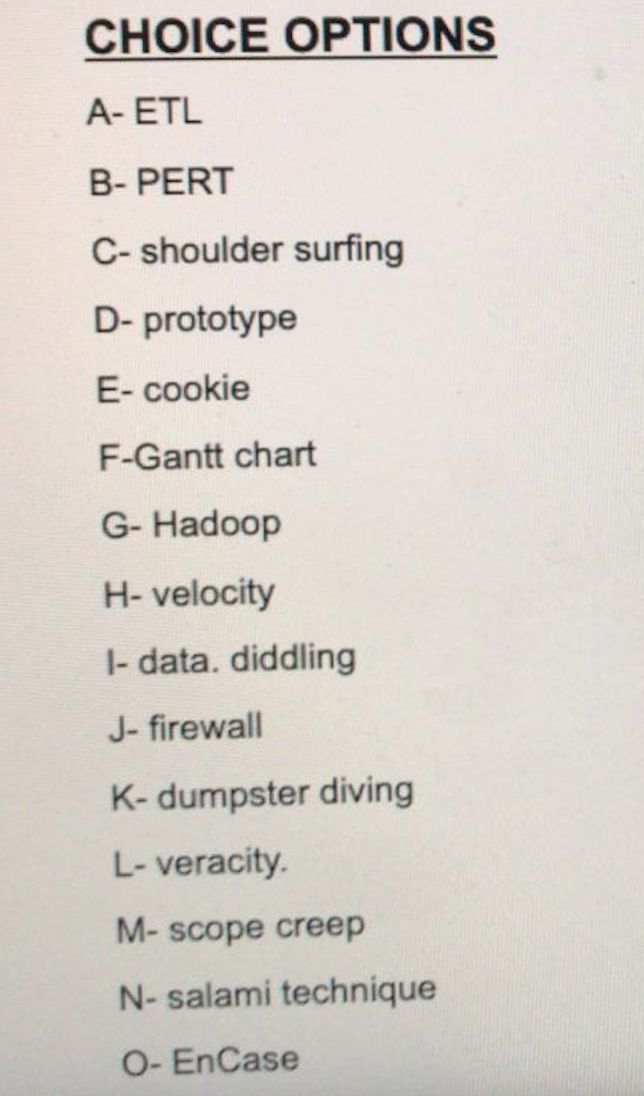
1- Stealing personal information from trash cans is called as --- 2- Observing users as they enter passwords or other personal information to a computer is called as --- ----- 3- The act of altering data that are entered into, or used by, a computer is called as 4-A software program specifically designed for computer forensic investigations is called as 5-- is a scaled-down, experimental version of a nonexistent information system that a desıgn team can -- develop cheaply and quickly for user-evaluation purposes 6- is useful for both scheduling and tracking the activities of systems implementation projects because actual progress can be contrasted with the planned progress. 7-- ---- is the process of extracting data from similar or disparate data sources, harmonizing the data into a common format, and importing the data into a final target data store. 8- Extent to which data can be trusted for insights is called as CHOICE OPTIONS A- ETL B- PERT C- shoulder surfing D- prototype E- cookie F-Gantt chart G- Hadoop H- velocity |- data. diddling J- firewall K- dumpster diving L- veracity. M- scope creep N- salami technique O- EnCase 1- Stealing personal information from trash cans is called as --- 2- Observing users as they enter passwords or other personal information to a computer is called as --- ----- 3- The act of altering data that are entered into, or used by, a computer is called as 4-A software program specifically designed for computer forensic investigations is called as 5-- is a scaled-down, experimental version of a nonexistent information system that a desıgn team can -- develop cheaply and quickly for user-evaluation purposes 6- is useful for both scheduling and tracking the activities of systems implementation projects because actual progress can be contrasted with the planned progress. 7-- ---- is the process of extracting data from similar or disparate data sources, harmonizing the data into a common format, and importing the data into a final target data store. 8- Extent to which data can be trusted for insights is called as CHOICE OPTIONS A- ETL B- PERT C- shoulder surfing D- prototype E- cookie F-Gantt chart G- Hadoop H- velocity |- data. diddling J- firewall K- dumpster diving L- veracity. M- scope creep N- salami technique O- EnCase
Expert Answer:

Related Book For 

Statistical Techniques in Business and Economics
ISBN: 978-0078020520
16th edition
Authors: Douglas Lind, William Marchal
Posted Date:
Students also viewed these accounting questions
-
Develop a user-friendly computer program for systems of equations using the fourth-order RK method. Use this program to duplicate the computation In Example 25.10.
-
Can activities 5 and 6 of Figure be eliminated? What risks does a project manager incur if these activities areeliminated? CONTRACTOR PROGRAM OFFICE REQUEST FOR HEDULES REVEL ROLIGH VERFY THAT ALL...
-
Can bar charts and PERT diagrams be used to smooth out departmental manpower requirements?
-
Automobiles air bags are filled via the decomposition of sodium azide, according to the following equation: 2 NaN3 (s) 2 Na (s) +3 N2 (g) Calculate the work (in L atm) when 2.25 g of sodium azide...
-
Work out the following problems: a. What is the number of protons in helium? in iron? b. Will an H bond form between H3CCH=O and H2O? Draw a simple figure to support your answer. c. Draw the...
-
The unit cell of nickel arsenide is shown here. (a) What type of lattice does this crystal possess? (b) What is the empirical formula? -3.57 A- ( 120 side view top view Ni As
-
A car rental agency has 19 compact cars and 12 intermediate-size cars. If four of the cars are randomly selected for a safety check, what is the probability of getting two of each kind?
-
Outdoor Life manufactures snowboards. Its cost of making 1,890 bindings is as follows: Direct materials . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . ....
-
Kohn Corporation statement of income and retained earnings year ended December 31, 19x2: Net Sales Expenses Cost of Goods Sold Selling, General and Administrative Depreciation Interest Net Income...
-
Maverick Ltd is a supplier of leisure boats both to the retail trade and to the public. On Monday, Cruise Ltd, one of Maverick Ltd's regular suppliers, agreed to supply Maverick Ltd with 15 carbon...
-
Sarah, her husband and four young children live in Wellington. Sarah gets a lucrative job offer in London and the family decide to move there. Sarah is a chartered accountant and her husband Morehu...
-
Describe a strategic goal that could support the mission statement: " To provide a high-quality, low-cost product to our customers." Who would be responsible for this goal, and what kind of power...
-
Define the service package of the local hospital or individual doctor's office you are familiar with. What is its strongest element? What is its weakest one? Why? How can/should it be improved? To...
-
a) Digitizing the Request for Proposal (RFP) procedure can have a number of advantages, such as time and money savings, increased effectiveness, and more transparency. What are some of the key...
-
Based on my spark type result given below how it fits with what you are learning about communication and leadership in healthcare. Your Primary Sparketype The Nurturer Your Primary Sparketype...
-
Considering the information shared, how can you utilize the information in your workplace. Select three different points made by the speaker and give examples of similar non-verbal communication in...
-
PROBLEM ONE Make journal entries for each of the following. Attach a page for the problem one journal entries. a. $500,000 4% bond is issued at 100. b. $500,000 4% bond is issued at 98. c. $500,000...
-
A liquid flows upward through a valve situated in a vertical pipe. Calculate the differential pressure (kPa) between points A and B. The mean velocity of the flow is 4.1 m/s. The specific gravity of...
-
A carbon monoxide detector in the Wheelock household activates once every 200 days on average. Assume this activation follows the exponential distribution. What is the probability that: a. There will...
-
The following table gives information on the Consumer Price Index and the monthly take-home pay of Bill Martin, an employee at Ford Motor Corporation, from 198284 and 2012. a. What is the purchasing...
-
Using the period 200002 as the base period compute a simple index of international sales for each year from 2003 to2012. Domestic Sales International Sales Employees $ million) 5 ($ million) 11,856...
-
Which elements an agile software team must consider to attribute effort to a product?
-
Why is the rounded Fibonacci series used to assign story points instead of the natural numbers?
-
Variants and exception handlers are alternate flows for a use case. In which situations should one or the other be used?

Study smarter with the SolutionInn App