1) Two-phase locking (2PL) is widely used for concurrency control in a relational database system. Consider...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
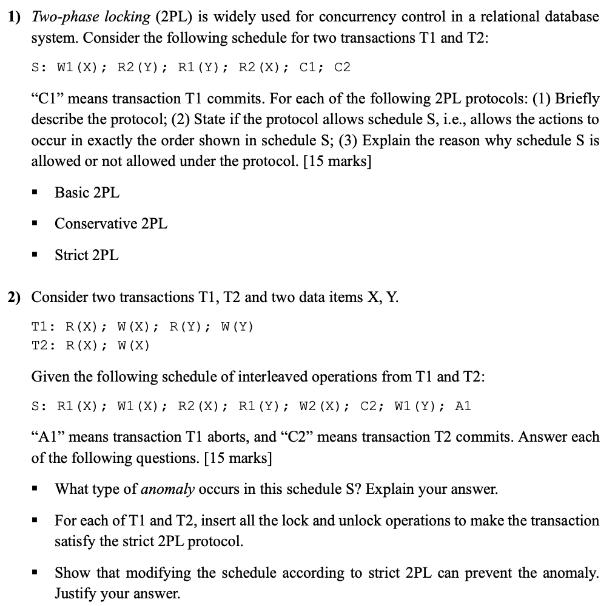
1) Two-phase locking (2PL) is widely used for concurrency control in a relational database system. Consider the following schedule for two transactions T1 and T2: S: W1 (X); R2 (Y); R1 (Y); R2 (X); C1; C2 "C1" means transaction T1 commits. For each of the following 2PL protocols: (1) Briefly describe the protocol; (2) State if the protocol allows schedule S, i.e., allows the actions to occur in exactly the order shown in schedule S; (3) Explain the reason why schedule S is allowed or not allowed under the protocol. [15 marks] Basic 2PL Conservative 2PL ■ ■ ▪ Strict 2PL 2) Consider two transactions T1, T2 and two data items X, Y. T1: R (X); W (X); R(Y); W (Y) T2: R (X); W (X) Given the following schedule of interleaved operations from T1 and T2: S: R1 (X); W1 (X); R2 (X); R1 (Y); W2 (X); C2; W1 (Y); Al "A1" means transaction T1 aborts, and "C2" means transaction T2 commits. Answer each of the following questions. [15 marks] ▪ What type of anomaly occurs in this schedule S? Explain your answer. ■ For each of T1 and T2, insert all the lock and unlock operations to make the transaction satisfy the strict 2PL protocol. ▪ Show that modifying the schedule according to strict 2PL can prevent the anomaly. Justify your answer. 1) Two-phase locking (2PL) is widely used for concurrency control in a relational database system. Consider the following schedule for two transactions T1 and T2: S: W1 (X); R2 (Y); R1 (Y); R2 (X); C1; C2 "C1" means transaction T1 commits. For each of the following 2PL protocols: (1) Briefly describe the protocol; (2) State if the protocol allows schedule S, i.e., allows the actions to occur in exactly the order shown in schedule S; (3) Explain the reason why schedule S is allowed or not allowed under the protocol. [15 marks] Basic 2PL Conservative 2PL ■ ■ ▪ Strict 2PL 2) Consider two transactions T1, T2 and two data items X, Y. T1: R (X); W (X); R(Y); W (Y) T2: R (X); W (X) Given the following schedule of interleaved operations from T1 and T2: S: R1 (X); W1 (X); R2 (X); R1 (Y); W2 (X); C2; W1 (Y); Al "A1" means transaction T1 aborts, and "C2" means transaction T2 commits. Answer each of the following questions. [15 marks] ▪ What type of anomaly occurs in this schedule S? Explain your answer. ■ For each of T1 and T2, insert all the lock and unlock operations to make the transaction satisfy the strict 2PL protocol. ▪ Show that modifying the schedule according to strict 2PL can prevent the anomaly. Justify your answer.
Expert Answer:
Answer rating: 100% (QA)
Question 1 TwoPhase Locking 2PL Protocols 1 Basic 2PL Description In Basic 2PL a transaction is divided into two phases the growing phase where locks ... View the full answer

Related Book For 

Database management systems
ISBN: 978-0072465631
3rd edition
Authors: Raghu Ramakrishan, Johannes Gehrke, Scott Selikoff
Posted Date:
Students also viewed these operating system questions
-
In order to measure the consistency of database, the concurrency control of transaction is considered seriously to increase the performance. The best practices are serialization or Un serialization...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
How well employees modify their thoughts and behavior to align with and support a new or changing environment is known as Multiple Choice proactive task performance. proficient task performance....
-
Consider a regenerative gas-turbine power plant with two stages of compression and two stages of expansion. The overall pressure ratio of the cycle is 9. The air enters each stage of the compressor...
-
(a) Obtain the model of the voltage vo, given the supply voltage vs, for the circuit shown in Figure. (b) Suppose vs(t) = Vus(t). Obtain the expressions for the free and forced responses for v"(t). 2R
-
Its Intoxicating Inc., is a Pennsylvania corporation that manufactures and distributes cosmetic products to various retailers. Maritim is a German company that owns and operates hotels throughout...
-
Long Board Company Manufactures designer paddle boards in a wide variety of sizes and styles. The following incomplete ledger accounts refer to transactions that are summarized for May: In addition,...
-
You have just been named Director of Data Administration of General Hardware Co. General Hardware maintains a large, central IS organization with several operational relational databases at its...
-
Suppose a person has a utility function given by U = [x + y]1/ where is a number between - and 1. This is called a constant elasticity of substitution (CES) utility function. You will encounter CES...
-
Find an equation of the largest sphere contained in the cube determined by the planes x=8, x=-4, y=-2, y=10, z=-3, and z=9
-
If facilities have lower fixed costs a few high-capacity facilities are preferred because this helps lower transportation costs. a few local facilities are preferred because this helps lower...
-
Customer preferences and requirements may be in terms of desired response time and payment terms. the employment of their own staff. the choice of transportation mode or transportation provider....
-
The demand allocation model requires the following input: number of factory locations. number of customers in each location. number of employees in total. number of destinations served by each...
-
Gravity models also assume that the transportation cost grows exponentially with the quantity shipped and the distance traveled. grows linearly with the quantity shipped and the distance traveled....
-
Decisions concerning the role of each facility are significant because they determine the amount of flexibility the supply chain has in demanding change. they determine the amount of flexibility the...
-
Which of the following factors does not contribute to cross-border takeovers being seen as more risky than their domestic counterparts? A. Structural barriers B. Higher potential political risk C....
-
Identify one local business that uses a perpetual inventory system and another that uses a periodic system. Interview an individual in each organization who is familiar with the inventory system and...
-
The following relations keep track of airline flight information: Flights (flno: integer, from: string, to: string, distance: integer, departs: time, arrives: time, price: real) Aircraft (aid:...
-
Consider a disk with a sector size of 512 bytes, 2000 tracks per surface, 50 sectors per track, five double-sided platters, and average seek time of 10 msec. 1. What is the capacity of a track in...
-
Consider the SQL query whose answer is shown in Figure 3.2. Sid Name Login Age Gpa 53831 Madayan madayan@ 11 1.8 53832 Gulda guldu@music 12 2.0 Students with age < 18 on Instance S 1....
-
The transfer function of a dynamic system is given by \[G(s)=\frac{s+1}{4 s^{4}+5 s^{3}+2 s^{2}+s+6} \] a. Using Routh's stability criterion, determine the stability of the system. b. Using MATLAB,...
-
Figure 10.40 shows a negative feedback control system. a. Design a P controller such that the damping ratio of the closed-loop system is 0.5 . b. Estimate the rise time, overshoot, and \(2 \%\)...
-
Consider the feedback system shown in Figure 10.26. a. Using Routh's stability criterion, determine the range of the control gain \(K\) for which the closed-loop system is stable. b. Use MATLAB...

Study smarter with the SolutionInn App