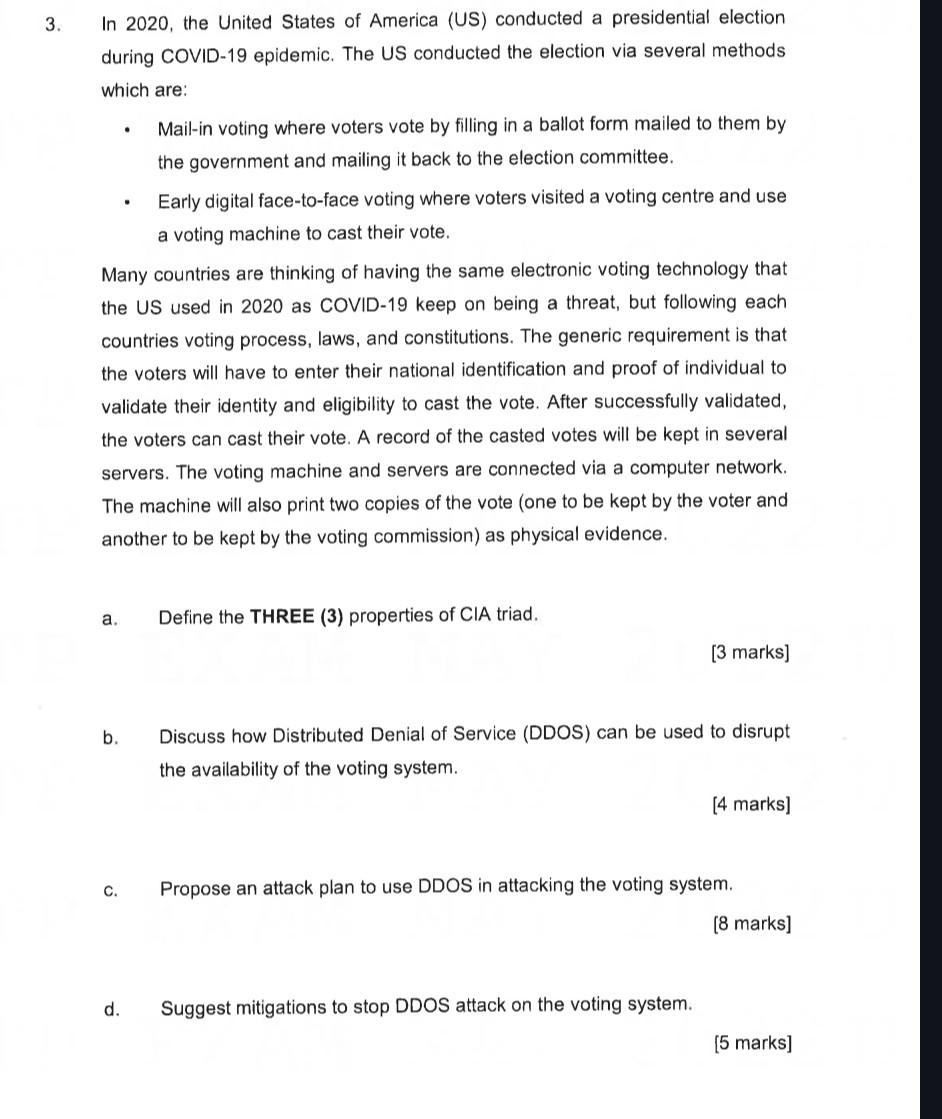
3. In 2020, the United States of America (US) conducted a presidential election. during COVID-19 epidemic....
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
3. In 2020, the United States of America (US) conducted a presidential election. during COVID-19 epidemic. The US conducted the election via several methods which are: a. b. Many countries are thinking of having the same electronic voting technology that the US used in 2020 as COVID-19 keep on being a threat, but following each countries voting process, laws, and constitutions. The generic requirement is that the voters will have to enter their national identification and proof of individual to validate their identity and eligibility to cast the vote. After successfully validated, the voters can cast their vote. A record of the casted votes will be kept in several servers. The voting machine and servers are connected via a computer network. The machine will also print two copies of the vote (one to be kept by the voter and another to be kept by the voting commission) as physical evidence. C. . d. Mail-in voting where voters vote by filling in a ballot form mailed to them by the government and mailing it back to the election committee. Early digital face-to-face voting where voters visited a voting centre and use a voting machine to cast their vote. Define the THREE (3) properties of CIA triad. [3 marks] Discuss how Distributed Denial of Service (DDOS) can be used to disrupt the availability of the voting system. Suggest mitigations to stop DDOS attack on the voting system. [4 marks] Propose an attack plan to use DDOS in attacking the voting system. [8 marks] [5 marks] 3. In 2020, the United States of America (US) conducted a presidential election. during COVID-19 epidemic. The US conducted the election via several methods which are: a. b. Many countries are thinking of having the same electronic voting technology that the US used in 2020 as COVID-19 keep on being a threat, but following each countries voting process, laws, and constitutions. The generic requirement is that the voters will have to enter their national identification and proof of individual to validate their identity and eligibility to cast the vote. After successfully validated, the voters can cast their vote. A record of the casted votes will be kept in several servers. The voting machine and servers are connected via a computer network. The machine will also print two copies of the vote (one to be kept by the voter and another to be kept by the voting commission) as physical evidence. C. . d. Mail-in voting where voters vote by filling in a ballot form mailed to them by the government and mailing it back to the election committee. Early digital face-to-face voting where voters visited a voting centre and use a voting machine to cast their vote. Define the THREE (3) properties of CIA triad. [3 marks] Discuss how Distributed Denial of Service (DDOS) can be used to disrupt the availability of the voting system. Suggest mitigations to stop DDOS attack on the voting system. [4 marks] Propose an attack plan to use DDOS in attacking the voting system. [8 marks] [5 marks]
Expert Answer:
Answer rating: 100% (QA)
The image contains questions regarding electronic voting cybersecurity and specifically the concept of the CIA triad and Distributed Denial of Service DDoS attacks Here are the answers to each of the ... View the full answer

Related Book For 

The Legal Environment Of Business A Managerial Approach Theory To Practice
ISBN: 9781260247800
4th Edition
Authors: Sean Melvin, Enrique Guerra-Pujol
Posted Date:
Students also viewed these programming questions
-
Googles ease of use and superior search results have propelled the search engine to its num- ber one status, ousting the early dominance of competitors such as WebCrawler and Infos- eek. Even later...
-
Read the case study "Southwest Airlines," found in Part 2 of your textbook. Review the "Guide to Case Analysis" found on pp. CA1 - CA11 of your textbook. (This guide follows the last case in the...
-
Telstar Limited was incorporated on 2 January 2015. On 3 January 2015, the company ordered plant from Germany at a cost of E1 million. The plant was loaded free on board in Hamburg on 1 March 2015,...
-
Find Io in the circuit shown. 12 A 4 12 4 12 4
-
Express the given trigonometric functions in terms of the same function of the reference angle. sin 243, cot 318
-
A typical loaded commercial jet airplane has an inertia of \(2.1 \times 10^{5} \mathrm{~kg}\). (a) Based on the time intervals involved, which do you expect to require more energy: getting the plane...
-
On November 1, 2015, Ambrose Company sold merchandise to a foreign customer for 100,000 FCUs with payment to be received on April 30, 2016. At the date of sale, Ambrose entered into a six-month...
-
What are some ways in which earnings management on construction contracts can be minimized?
-
You recently received the following e-mail from a client and friend: Hey Great Student, I cannot believe it is almost year end! Only a few days before its 2019. As you recall, I was lucky enough to...
-
Note: u(t) is the unit step function. (1 point) All the capacitors were discharged prior to assembly. Calculate the indicated values and expression. R = 2 2. Note: u(t) is the unit step function. R...
-
On December 29th, 2022, an IT company, Cloud Systems, Inc. signs a contract to provide computer and network maintenance to a local school district for three years beginning on January 1st, 2023. On...
-
A satellite has a mass of 5941 kg and is in a circular orbit 4.79 105 m above the surface of a planet. The period of the orbit is 2.1 hours. The radius of the planet is 4.29 106 m. What would be...
-
2. The gas phase reaction; (A + 3B 2C) is carried out isothermal mixed flow reactor (CSTR) at 2 atm. Feed stream includes 15% A, 60%B and 25% inerts in moles. a) Define the steady-state exit...
-
Consider the following option Stock price =100 Strike K-95 Volatility=20% Expiry T = 3 months Dividend yield = 2% Stock expected return = 6% Risk free = 3% 1) Calculate price of European call a. (20...
-
Tiger Tech, Inc. is an early-stage privately-held entity that is developing renewable energy technologies. Year 1 At the end of Year 1, a group of institutional investors get together and invest in...
-
For the circuit shown below, to what value must the variable resistor be adjusted in order to turn the SCR off? Assume IH = 10 mA and VAK = 0.7 V. Calculate the resistance in kilohms to 2 decimal...
-
Find the inverse, if it exists, for the matrix. -1
-
Assume that you are Miguels general manager in this chapters Theory to Practice problem. In groups (or individually), draft a one- to two-page code of ethics that would be appropriate for Java Road....
-
Bonifay and Fordham bought a box of .32-caliber bullets from a Walmart in Florida. Four hours later, the two men robbed an auto-parts store and killed Coker with those bullets. When they bought the...
-
Chambers worked for Travelers as a managing director. Questions arose regarding her management style and effectiveness, and she was fired. Among her claims against Travelers, she claimed that she was...
-
Use the \(\gamma\)-matrices in the Weyl representation to show that the Dirac equation (14.31) is equivalent to Eq. (14.25). Data from Eq. 14.31 Data from Eq. 14.25 (y"Pu-m)(p) = (iy" - m)(p) = 0
-
Prove that the boosted right-handed spinor \(\psi_{\mathrm{R}}(\boldsymbol{p})\) is related to the corresponding rest spinor by Eq. (14.21).
-
Prove the identity \((\sigma \cdot \boldsymbol{p})^{2}=\mathrm{I}^{(2)} p^{2}\), where \(\sigma=\left(\sigma_{1}, \sigma_{2}, \sigma_{3} ight)\) are the Pauli matrices, \(\boldsymbol{p}\) is the...

Study smarter with the SolutionInn App