Question: 8. Communication Protocols You are trying to have a secure conversation with Alice, however, Mallory may be listening. (a) You and Alice are setting up
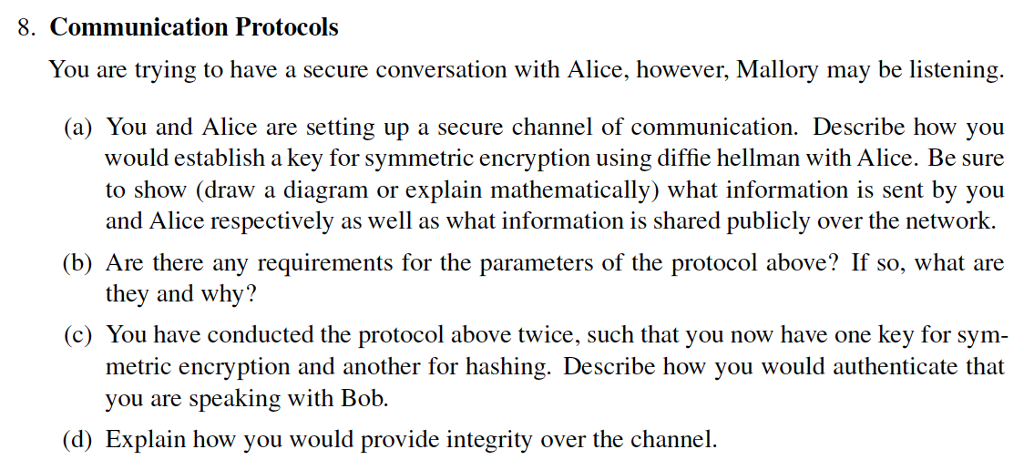
8. Communication Protocols You are trying to have a secure conversation with Alice, however, Mallory may be listening. (a) You and Alice are setting up a secure channel of communication. Describe how you would establish a key for symmetric encryption using diffie hellman with Alice. Be sure to show (draw a diagram or explain mathematically) what information is sent by you and Alice respectively as well as what information is shared publicly over the network. (b) Are there any requirements for the parameters of the protocol above? If so, what are they and why? (c) You have conducted the protocol above twice, such that you now have one key for sym- metric encryption and another for hashing. Describe how you would authenticate that you are speaking with Bob. d) Explain how you would provide integrity over the channel
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


