(a) Define the following terms from the context of cyber security: Vulnerability Threat Attack (b) Describe...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
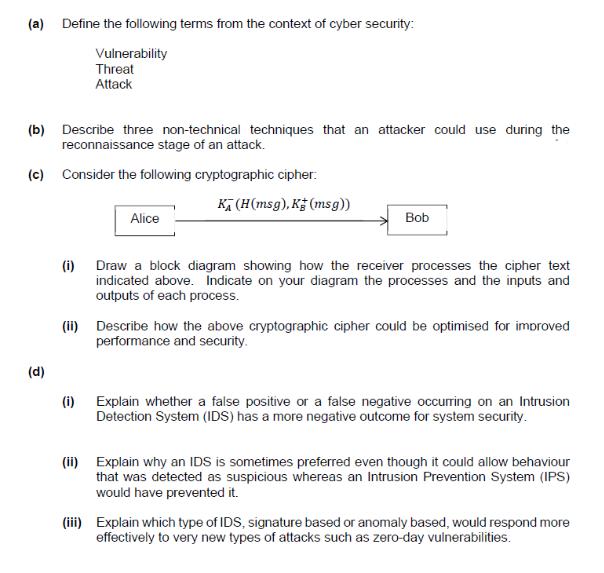
(a) Define the following terms from the context of cyber security: Vulnerability Threat Attack (b) Describe three non-technical techniques that an attacker could use during the reconnaissance stage of an attack. (c) Consider the following cryptographic cipher: (d) Alice K₁ (H(msg), K (msg)) (i) Bob (i) Draw a block diagram showing how the receiver processes the cipher text indicated above. Indicate on your diagram the processes and the inputs and outputs of each process. (ii) Describe how the above cryptographic cipher could be optimised for improved performance and security. Explain whether a false positive or a false negative occurring on an Intrusion Detection System (IDS) has a more negative outcome for system security. (ii) Explain why an IDS is sometimes preferred even though it could allow behaviour that was detected as suspicious whereas an Intrusion Prevention System (IPS) would have prevented it. (iii) Explain which type of IDS, signature based or anomaly based, would respond more effectively to very new types of attacks such as zero-day vulnerabilities. (a) Define the following terms from the context of cyber security: Vulnerability Threat Attack (b) Describe three non-technical techniques that an attacker could use during the reconnaissance stage of an attack. (c) Consider the following cryptographic cipher: (d) Alice K₁ (H(msg), K (msg)) (i) Bob (i) Draw a block diagram showing how the receiver processes the cipher text indicated above. Indicate on your diagram the processes and the inputs and outputs of each process. (ii) Describe how the above cryptographic cipher could be optimised for improved performance and security. Explain whether a false positive or a false negative occurring on an Intrusion Detection System (IDS) has a more negative outcome for system security. (ii) Explain why an IDS is sometimes preferred even though it could allow behaviour that was detected as suspicious whereas an Intrusion Prevention System (IPS) would have prevented it. (iii) Explain which type of IDS, signature based or anomaly based, would respond more effectively to very new types of attacks such as zero-day vulnerabilities.
Expert Answer:
Answer rating: 100% (QA)
a Vulnerability Definition A vulnerability in cybersecurity refers to a weakness or flaw in a system application network or process that could be exploited by a threat to compromise the security of th... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these computer network questions
-
KYC's stock price can go up by 15 percent every year, or down by 10 percent. Both outcomes are equally likely. The risk free rate is 5 percent, and the current stock price of KYC is 100. (a) Price a...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
What is meant by budgetary control?
-
Assume the role of a social science researcher in charge of developing a new crime prevention program targeted toward juveniles in the K-12 school system. Review current crime prevention programs...
-
Ramona Kim is a California Highway Patrol (CHP) officer who works in the city of San Diego. Having lost her own uncle in a car accident, she is particularly interested in educating local drivers...
-
Compressors used in as turbine are: (a) Reciprocating type (b) Centrifugal type (c) Axial flow type (d) None of the above
-
Working backward from consolidated income statements. Dealco Corporation published a consolidated income statement for the year, shown in Exhibit 13.10. The unconsolidated affiliate retained 25% of...
-
Program for find distance between two Coordinate points of (x1,y1), (x2,y2)?
-
The hollow tube assembly rotates about a vertical axis with angular velocity = = 4 rad /s and = = 2 rad /s 2 . A small 0.2-kg slider P moves inside the horizontal tube portion under the control...
-
Discuss how you would address illegal drug use in the U.S. Discuss how you would address gang crime in the U.S. Discuss/Explain the differences between domestic terrorism and international...
-
If the earth's electric field is 750 N/C downward, what must be the charge on a 3.0-kg object so that it would be "weightless"?
-
Two stone spheres are cut from a certain uniformly dense rock. The first sphere has a mass of 4 . 7 kg and a radius of 3 . 2 m . The mass of the second sphere is 2 kg . a . What is the density of the...
-
what is the heat produced in a conductor in 2 5 seconds if there is a current of 1 1 Amps and a resistance in the conductor of 7 . 2 ohms?
-
Assume your AC thermostat is set so that the temperature in your home or apartment is maintained at 75 degrees F (24 degrees C) at all times during the summer. How much would you save each month if...
-
The cosmic microwave background has a peak spectral radiance frequency of 1 6 0 . 2 3 ghz . With this in mind, why was the planck telescope made to have a 1 . 5 m diameter mirror and to achieve a...
-
Class Exercise 2 Viti Industries needs to choose a production method for its new product The firm has gathered the Tollowing production cost data and the price forecast: Variable cost per unit ($)...
-
Design an experiment to demonstrate that RNA transcripts are synthesized in the nucleus of eukaryotes and are subsequently transported to the cytoplasm.
-
Which of the following terms best describes the process of repairing known vulnerabilities? a. Monitoring b. Testing c. Patching d. Updating
-
Explain that to qualify for the HCISPP you must focus on security management topics and healthcare; this certification requires the candidate to demonstrate knowledge in six specialty domains on its...
-
Compare and contrast one of most common social engineering attacks, known as the advance-fee fraud (AFF) and phishing. Stress that AFF is also known as 4-1-9 fraud due to it being named after a...
-
The unadjusted trial balance of Helenas Hire Cars is shown below (ignore GST). Additional information 1. Petrol purchased on credit for $680 and used during the last week in June has not been paid...
-
Gavins Gardening Equipment Hires unadjusted trial balance of the business appears as shown below. Ignore GST. Additional information 1. Expired insurance amounts to $750. 2. June electricity costs of...
-
Lana Priest set up a home sewing business on 1 July 2019. Usually, Lana collects $20 per hour for sewing on the completion of each days work and pays for the maintenance of her machine with cash....

Study smarter with the SolutionInn App


