(a) What is an STP attack? Cisco has two security features built into its layer 2...
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
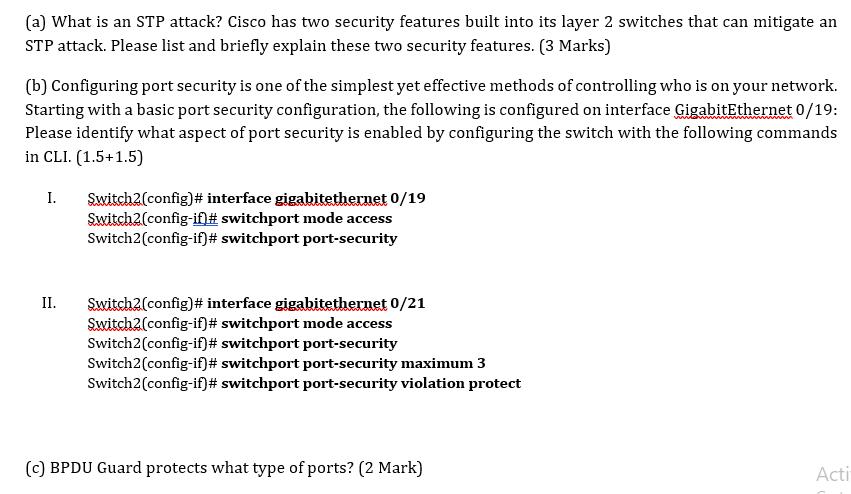
(a) What is an STP attack? Cisco has two security features built into its layer 2 switches that can mitigate an STP attack. Please list and briefly explain these two security features. (3 Marks) (b) Configuring port security is one of the simplest yet effective methods of controlling who is on your network. Starting with a basic port security configuration, the following is configured on interface GigabitEthernet 0/19: Please identify what aspect of port security is enabled by configuring the switch with the following commands in CLI. (1.5+1.5) I. Switch2(config)# interface gigabitethernet 0/19 Switch2(config-if)# switchport mode access Switch2(config-if)# switchport port-security II. Switch2(config)# interface gigabitethernet 0/21 Switch2(config-if)# switchport mode access Switch2(config-if)# switchport port-security Switch2(config-if)# switchport port-security maximum 3 Switch2(config-if)# switchport port-security violation protect (c) BPDU Guard protects what type of ports? (2 Mark) Acti (a) What is an STP attack? Cisco has two security features built into its layer 2 switches that can mitigate an STP attack. Please list and briefly explain these two security features. (3 Marks) (b) Configuring port security is one of the simplest yet effective methods of controlling who is on your network. Starting with a basic port security configuration, the following is configured on interface GigabitEthernet 0/19: Please identify what aspect of port security is enabled by configuring the switch with the following commands in CLI. (1.5+1.5) I. Switch2(config)# interface gigabitethernet 0/19 Switch2(config-if)# switchport mode access Switch2(config-if)# switchport port-security II. Switch2(config)# interface gigabitethernet 0/21 Switch2(config-if)# switchport mode access Switch2(config-if)# switchport port-security Switch2(config-if)# switchport port-security maximum 3 Switch2(config-if)# switchport port-security violation protect (c) BPDU Guard protects what type of ports? (2 Mark) Acti
Expert Answer:
Answer rating: 100% (QA)
a An STP Spanning Tree Protocol attack is a network attack that aims to disrupt or manipulate the operation of the Spanning Tree Protocol which is used in Ethernet networks to prevent loops and ensure ... View the full answer

Related Book For 

Principles Of Information Security
ISBN: 9780357506431
7th Edition
Authors: Michael E. Whitman, Herbert J. Mattord
Posted Date:
Students also viewed these computer network questions
-
Describe how the implement of the Ethernet frame classification mechanism in an Ethernet switch. For each functional block describe the main functions, actions and algorithms used. (No implementation...
-
The following additional information is available for the Dr. Ivan and Irene Incisor family from Chapters 1-5. Ivan's grandfather died and left a portfolio of municipal bonds. In 2012, they pay Ivan...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
A financial institution can borrow $100 million for 2 years at 3%. It plans to invest this money in a 1-year security with an interest rate of 4.8% per year. Calculate net interest income for the...
-
Write a paragraph describing a hypothetical project scenario and then provide an example of a change for each of the following categories: External Event Error or omission in scope of product Error...
-
The following represents selected information taken from a companys aging schedule to estimate uncollectible accounts receivable at year-end. Instructions (a) Calculate the total estimated bad debts...
-
A fluid flows through a horizontal 0.1-in.-diameter pipe. When the Reynolds number is 1500 , the head loss over a \(20-\mathrm{ft}\) length of the pipe is \(6.4 \mathrm{ft}\). Determine the fluid...
-
Kadex Corporation, a small manufacturing company, did not use the services of independent auditors during the first two years of its existence. Near the end of the third year, Kadex retained Jones &...
-
Norma Electronics sell its products for cash and on credit. It usually provides 6 % of its credit sales as allowance for bad and doubtful debts. In the month of April 2 0 x 1 , Norma Electronics...
-
An oil company produces three brands of oils: Regular, Multi grade, and Supreme. Each brand of oil is composed of one or more of four crude stocks, each having a different viscosity index. The...
-
Implement Warshall's algorithm in a file called Warshalljava. Your program should read the name of a file from the command line. The first line of the file will contain the number of vertices in the...
-
Candy making is a fun business, and so it is no surprise that it is fun to work at the Jelly Belly Candy Company of Fairfield, California. Although this company has cheesecake, buttered popcorn,...
-
Rajesh is considering two investments. The expected returns are 8% for investment A and 15% for investment B. The standard deviations are 6% and 10% for investments A and B, respectively. Which...
-
During 2018, Toyota Motor Company shares went from 7,500 to 6,500, while paying a dividend of 220. At the same time, the exchange rate went from $1 = 113 to $1 = 109. a. What was the total dollar...
-
Is the use of HRMS for narrowing down the list of candidates and sending form letters, including rejection letters, too impersonal? Why or why not?
-
During the year, the price of British gilts (government bonds) went from 102 to 106, while paying a coupon of 9. At the same time, the exchange rate went from 1:$1.40 to 1:$1.25. What was the total...
-
AIM: Write a C program to find factorial of a given number.
-
Vince, Inc. has developed and patented a new laser disc reading device that will be marketed internationally. Which of the following factors should Vince consider in pricing the device? I. Quality of...
-
Summarize that information security safeguards offer three levels of controls: managerial, operational, and technical. Managerial controls are security processes that are designed by strategic...
-
I. Present reasons why this phase of the SDLC is often the most time consuming and expensive. II. Explain the life cycle does not have a hard ending for a system once this phase has been completed....
-
What type of firewall examines every incoming packet header and can selectively filter packets based on header information, such as destination address, source address, packet type, and other key...
-
The chapter provides sample goals for an initial sales call on a prospect. (a) What other goals can you come up with that might be appropriate for an initial sales call? (b) Develop three or four...
-
What are some reasons a potential prospect might not be readily accessible? How far should you go to try to overcome such an accessibility problem before you move to the next lead?
-
List three or four criteria you could use to qualify a lead as a likely prospect. How would you find out if the lead meets these criteria?

Study smarter with the SolutionInn App


