Adapted from Perlman's book) A broadcast storm is an event that causes a flurry of messages....
Fantastic news! We've Found the answer you've been seeking!
Question:
Transcribed Image Text:
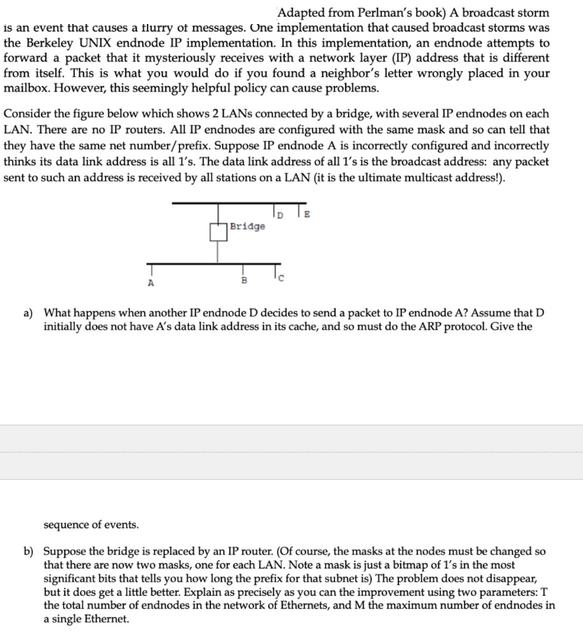
Adapted from Perlman's book) A broadcast storm is an event that causes a flurry of messages. One implementation that caused broadcast storms was the Berkeley UNIX endnode IP implementation. In this implementation, an endnode attempts to forward a packet that it mysteriously receives with a network layer (IP) address that is different from itself. This is what you would do if you found a neighbor's letter wrongly placed in your mailbox. However, this seemingly helpful policy can cause problems. Consider the figure below which shows 2 LANs connected by a bridge, with several IP endnodes on each LAN. There are no IP routers. All IP endnodes are configured with the same mask and so can tell that they have the same net number/prefix. Suppose IP endnode A is incorrectly configured and incorrectly thinks its data link address is all 1's. The data link address of all 1's is the broadcast address: any packet sent to such an address is received by all stations on a LAN (it is the ultimate multicast address!). Bridge a) What happens when another IP endnode D decides to send a packet to IP endnode A? Assume that D initially does not have A's data link address in its cache, and so must do the ARP protocol. Give the sequence of events. b) Suppose the bridge is replaced by an IP router. (Of course, the masks at the nodes must be changed so that there are now two masks, one for each LAN. Note a mask is just a bitmap of I's in the most significant bits that tells you how long the prefix for that subnet is) The problem does not disappear, but it does get a little better. Explain as precisely as you can the improvement using two parameters: T the total number of endnodes in the network of Ethernets, and M the maximum number of endnodes in a single Ethernet. Adapted from Perlman's book) A broadcast storm is an event that causes a flurry of messages. One implementation that caused broadcast storms was the Berkeley UNIX endnode IP implementation. In this implementation, an endnode attempts to forward a packet that it mysteriously receives with a network layer (IP) address that is different from itself. This is what you would do if you found a neighbor's letter wrongly placed in your mailbox. However, this seemingly helpful policy can cause problems. Consider the figure below which shows 2 LANs connected by a bridge, with several IP endnodes on each LAN. There are no IP routers. All IP endnodes are configured with the same mask and so can tell that they have the same net number/prefix. Suppose IP endnode A is incorrectly configured and incorrectly thinks its data link address is all 1's. The data link address of all 1's is the broadcast address: any packet sent to such an address is received by all stations on a LAN (it is the ultimate multicast address!). Bridge a) What happens when another IP endnode D decides to send a packet to IP endnode A? Assume that D initially does not have A's data link address in its cache, and so must do the ARP protocol. Give the sequence of events. b) Suppose the bridge is replaced by an IP router. (Of course, the masks at the nodes must be changed so that there are now two masks, one for each LAN. Note a mask is just a bitmap of I's in the most significant bits that tells you how long the prefix for that subnet is) The problem does not disappear, but it does get a little better. Explain as precisely as you can the improvement using two parameters: T the total number of endnodes in the network of Ethernets, and M the maximum number of endnodes in a single Ethernet.
Expert Answer:
Answer rating: 100% (QA)
a What happens when another IP endnode D decides to send a packet to IP endnode A Assume that D initially does not have As data link address in its ca... View the full answer

Related Book For 

Accounting Information Systems
ISBN: 978-0133428537
13th edition
Authors: Marshall B. Romney, Paul J. Steinbart
Posted Date:
Students also viewed these computer network questions
-
A student addresses a bully mocking another student, " what you're doing isn't even clever or funny, everyone has a right ti express who they are.. you know like we say every morning.. liberty and...
-
Planning is one of the most important management functions in any business. A front office managers first step in planning should involve determine the departments goals. Planning also includes...
-
Managing Scope Changes Case Study Scope changes on a project can occur regardless of how well the project is planned or executed. Scope changes can be the result of something that was omitted during...
-
The following is an example of the reasoning of a rule utilitarian: "if the practice of lying is bad, then one ought not to lie now, even if in this case to lie would actually bring about better...
-
A milled-teeth steel pinion and gear pair have Sut = 113 kpsi, Sy = 86 kpsi and a hardness at the involute surface of 262 Brinell. The diametral pitch is 3 teeth/in, the face width is 2.5 in, and the...
-
What are the potential issues for Virgin America following the Alaska Airlines acquisition? Will Virgin America continue to appeal to the same types of customers? Why or why not? There are far more...
-
Consider two countries, A and B, with the technologies given by case 3 in Exercise 1. data from case 3 in exercise 1 Suppose that the wage rate in A, WA, equals \($9\) per hour; then, for mutually...
-
1. The U.S. International Trade Commissions committee in charge of the global safeguard investigation involving imports of steel has announced its recommendations to be forwarded to the president. Of...
-
Explain how advanced computational methods, such as Monte Carlo simulation and Bayesian networks, can be applied to improve hazard analysis accuracy and reduce uncertainty in risk assessment .
-
Calculate Z, HR, and sR by the Soave/Redlich/Kwong equation for the substance and conditions given by one of the parts of Pb. 6.14, and compare results with values found from suitable generalized...
-
Consider the following two assets: Asset Expected Return X Y 5.8% 14.2% If the risk free rate is 1%, what will happen to the prices of assets X and Y in an efficient market? A. Asset X's price will...
-
What does the following Java code do ? public Object function ( ) { if ( isEmpty ( ) ) return - 9 9 9 ;else { Object high;high = q [ front ] ;return high; } }
-
Name the legislations which underpin workplace and organisation policies and some procedures. ? Explain
-
Consider the following $ 1 , 0 0 0 face value bond which makes semi - annual coupon payments. Rema Bond CIBC 9 . 5 % Coupon rate Price 1 0 7 . 8 4 Maturity June 1 , 2 0 3 0 Settlement Date January 6...
-
Write a while loop to continually update this approximation (using the same formula from problem 1.1) until the relative approximate error, E = X+1 - X X is less than .00001. Use this approximation...
-
CircuitTown commenced a gift card program in January 2024 and sold $12,550 of gift cards in January, $19,900 in February, and $20,550 in March 2024 before discontinuing further gift card sales....
-
Identify the stages of meiosis on the diagram. AP A Answer Bank Homologous pairs split up in anaphase I. Crossing over happens between homologous pairs in prophase I. Homologous pairs of chromosomes...
-
2. In the circuit given in Figure 2, i,(t) = 5.67cos(5t)A and v (t) = 70.71 cos(5t 60) V a) Find the equivalent load impedance. State whether the load is inductive or capacitive. b) Calculate the...
-
As the internal auditor for No-Wear Products, you have been asked to document the companys payroll processing system. Based on your documentation, No-Wear hopes to develop a plan for revising the...
-
Cost-effective controls to provide confidentiality require valuing the information that is to be protected. This involves classifying information into discrete categories. Propose a minimal...
-
You are responsible for implementing a new employee performance measurement system that will provide factory supervisors with detailed information about each of their employees on a weekly basis. In...
-
Explain the difference between value-added and non-value-added activities in a process and provide examples.
-
Explain how the center-of-gravity method works.
-
A nnapolis Hospital is trying to reduce costs, yet it aims to improve the patient count and medical services. The hospital pharmacy, which is considered a primary process, uses two types of...

Study smarter with the SolutionInn App


