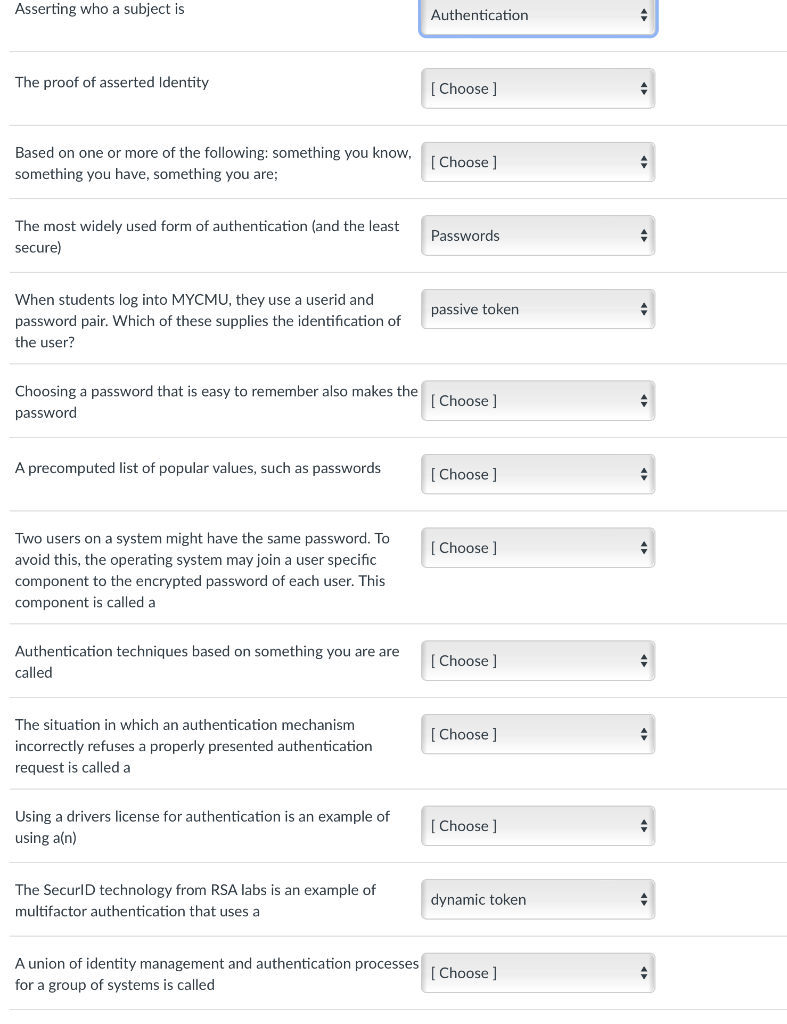
Question: Asserting who a subject is Authentication The proof of asserted Identity Choose] Based on one or more of the following: something you know, something you
![Choose] Based on one or more of the following: something you know,](https://dsd5zvtm8ll6.cloudfront.net/si.experts.images/questions/2024/09/66f514efdbc19_71166f514ef61c79.jpg)
Asserting who a subject is Authentication The proof of asserted Identity Choose] Based on one or more of the following: something you know, something you have, something you are; Choose ] The most widely used form of authentication (and the least secure) Passwords passive token When students log into MYCMU, they use a userid and password pair. Which of these supplies the identification of the user? Choosing a password that is easy to remember also makes the password Choose] A precomputed list of popular values, such as passwords [Choose ] [Choose ] Two users on a system might have the same password. To avoid this, the operating system may join a user specific component to the encrypted password of each user. This component is called a Authentication techniques based on something you are are called Choose ] [Choose] The situation in which an authentication mechanism incorrectly refuses a properly presented authentication request is called a Using a drivers license for authentication is an example of using a(n) Choose ] The SecurID technology from RSA labs is an example of multifactor authentication that uses a dynamic token 4 A union of identity management and authentication processes for a group of systems is called [Choose ] 4 [Choose ] dynamic token credential Integrity False Negative False Positive passive token federated identity management easier for an attacker to guess harder for an attacker to guess login elimination hierarchical identity management Biometric Authentication Identification Rainbow table userid Passwords multifactor authentication Dictionary Table Single Sign-On System Salt
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


