Question: BOB ALICE Yes Message (m) MD Hash Function Alice public-key Alice private-key Same? Hash Function MD - Public-key Decryption + Public-key Encryption El Private-Key Alice
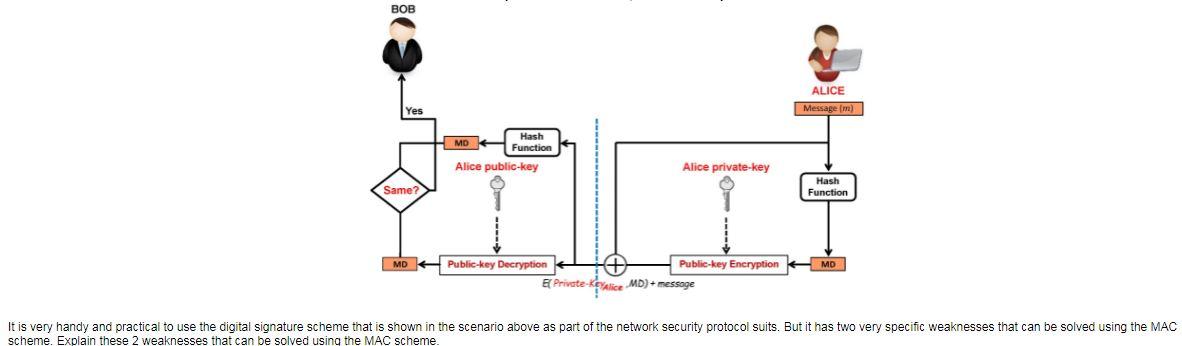
BOB ALICE Yes Message (m) MD Hash Function Alice public-key Alice private-key Same? Hash Function MD - Public-key Decryption + Public-key Encryption El Private-Key Alice MD)+ message It is very handy and practical use the digital signature scheme that is shown in the scenario above as part of the network security protocol suits. But it has two very specific weaknesses that can be solved using the MAC scheme. Explain these 2 weaknesses that can be solved using the MAC scheme
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


