List the five messages that Alice (A) and Bob (B) exchange in order for Bob to authenticate
Fantastic news! We've Found the answer you've been seeking!
Question:
List the five messages that Alice (A) and Bob (B) exchange in order for Bob to authenticate himself to Alice, by using his private key KB_pri to decrypt to prove that he is the owner of the private key, and for Alice to authenticate herself to Bob using a shared secret KAB with Bob.
Here is are some similar examples:
A, B, C
Transcribed Image Text:
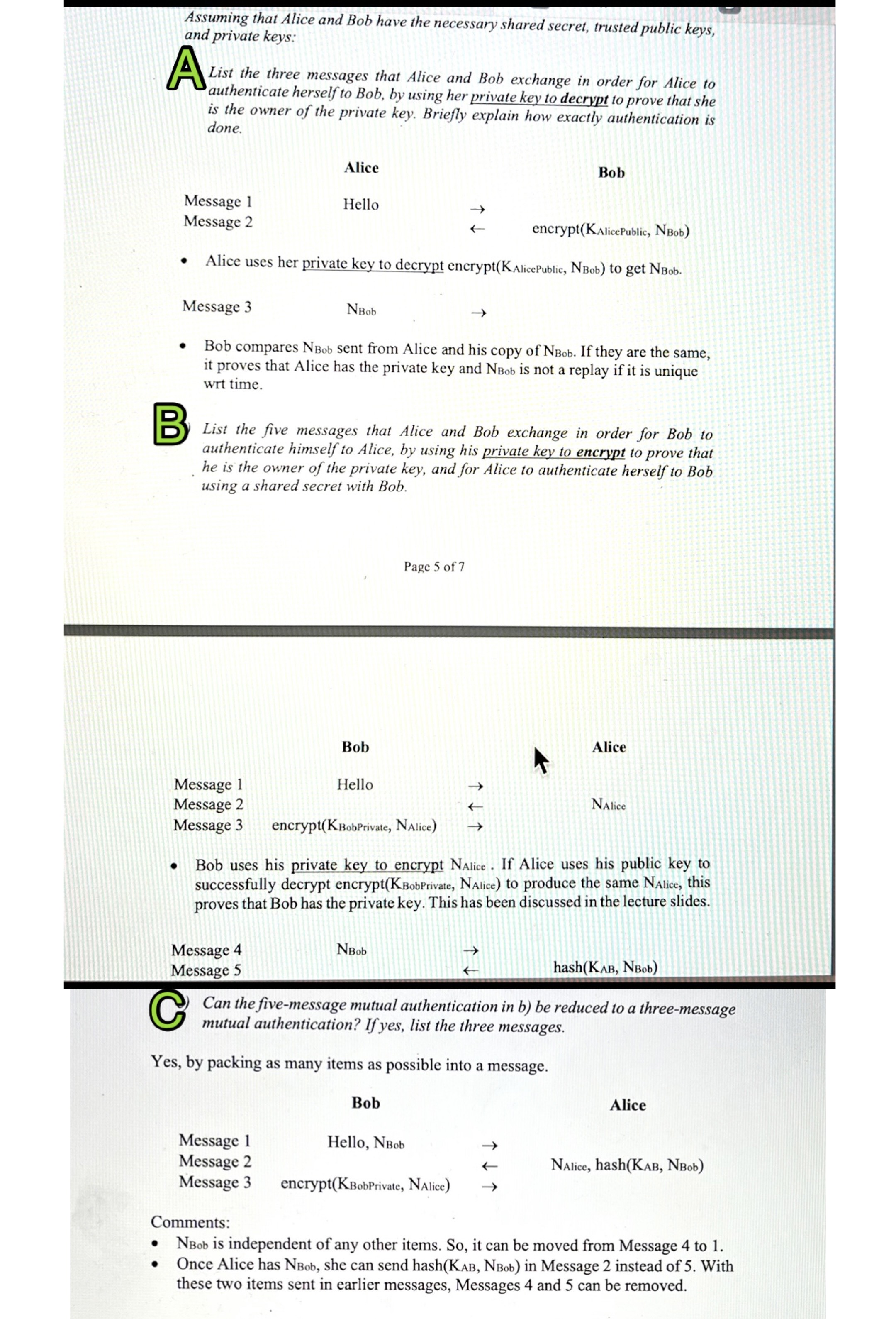
Assuming that Alice and Bob have the necessary shared secret, trusted public keys, and private keys: A List the three messages that Alice and Bob exchange in order for Alice to authenticate herself to Bob, by using her private key to decrypt to prove that she is the owner of the private key. Briefly explain how exactly authentication is done. Message 1 Message 2 encrypt(KAlice Public, NBob) Alice uses her private key to decrypt encrypt(KAlice Public, NBob) to get NBob. Alice Hello Message 3 Bob compares NBob sent from Alice and his copy of NBob. If they are the same, it proves that Alice has the private key and NBob is not a replay if it is unique wrt time. Message 4 Message 5 NBob B List the five messages that Alice and Bob exchange in order for Bob to authenticate himself to Alice, by using his private key to encrypt to prove that he is the owner of the private key, and for Alice to authenticate herself to Bob using a shared secret with Bob. Message 1 Message 2 Message 3 Bob Message 1 Message 2 Message 3 encrypt(KBobPrivate, NAlice) Hello Page 5 of 7 NBob Bob uses his private key to encrypt NAlice. If Alice uses his public key to successfully decrypt encrypt(KBobPrivate, NAlice) to produce the same NAlice, this proves that Bob has the private key. This has been discussed in the lecture slides. Bob Bob Hello, NBob hash(KAB, NBob) C Can the five-message mutual authentication in b) be reduced to a three-message mutual authentication? If yes, list the three messages. Yes, by packing as many items as possible into a message. encrypt(KBobPrivate, NAlice) Alice NAlice Alice NAlice, hash(KAB, NBob) Comments: NBob is independent of any other items. So, it can be moved from Message 4 to 1. Once Alice has NBob, she can send hash(KAB, NBob) in Message 2 instead of 5. With these two items sent in earlier messages, Messages 4 and 5 can be removed. Assuming that Alice and Bob have the necessary shared secret, trusted public keys, and private keys: A List the three messages that Alice and Bob exchange in order for Alice to authenticate herself to Bob, by using her private key to decrypt to prove that she is the owner of the private key. Briefly explain how exactly authentication is done. Message 1 Message 2 encrypt(KAlice Public, NBob) Alice uses her private key to decrypt encrypt(KAlice Public, NBob) to get NBob. Alice Hello Message 3 Bob compares NBob sent from Alice and his copy of NBob. If they are the same, it proves that Alice has the private key and NBob is not a replay if it is unique wrt time. Message 4 Message 5 NBob B List the five messages that Alice and Bob exchange in order for Bob to authenticate himself to Alice, by using his private key to encrypt to prove that he is the owner of the private key, and for Alice to authenticate herself to Bob using a shared secret with Bob. Message 1 Message 2 Message 3 Bob Message 1 Message 2 Message 3 encrypt(KBobPrivate, NAlice) Hello Page 5 of 7 NBob Bob uses his private key to encrypt NAlice. If Alice uses his public key to successfully decrypt encrypt(KBobPrivate, NAlice) to produce the same NAlice, this proves that Bob has the private key. This has been discussed in the lecture slides. Bob Bob Hello, NBob hash(KAB, NBob) C Can the five-message mutual authentication in b) be reduced to a three-message mutual authentication? If yes, list the three messages. Yes, by packing as many items as possible into a message. encrypt(KBobPrivate, NAlice) Alice NAlice Alice NAlice, hash(KAB, NBob) Comments: NBob is independent of any other items. So, it can be moved from Message 4 to 1. Once Alice has NBob, she can send hash(KAB, NBob) in Message 2 instead of 5. With these two items sent in earlier messages, Messages 4 and 5 can be removed.
Expert Answer:

Related Book For 

Financial Management for Public Health and Not for Profit Organizations
ISBN: 978-0132805667
4th edition
Authors: Steven A. Finkler, Thad Calabrese
Posted Date:
Students also viewed these computer network questions
-
Design a Java class that represents a cache with a fixed size. It should support operations like add, retrieve, and remove, and it should evict the least recently used item when it reaches capacity.
-
The Crazy Eddie fraud may appear smaller and gentler than the massive billion-dollar frauds exposed in recent times, such as Bernie Madoffs Ponzi scheme, frauds in the subprime mortgage market, the...
-
A decline in the aggregate demand has led to a decline in output in the economy equal to $10 billion. Government wants to counter this recession by reducing income taxes. Assuming that the marginal...
-
What are the important differences between Step 2 (Help) and Step 3 (People Change)?
-
You hold a diversified $100,000 portfolio consisting of 20 stocks with $5,000 invested in each. The portfolio's beta is 1.12. You plan to sell a stock with b = 0.90 and use the proceeds to buy a new...
-
What are the components of a statechart diagram?
-
On January 3, 2020, Mego Limited purchased 3,000 (30%) of the common shares of Sonja Corp. for $438,000. The following information is provided about the identifiable assets and liabilities of Sonja...
-
2. Draw logic diagrams for the following: a) Y = (A+B) + (B C) b) Y = (A+B) (A + C) c) Y = (A + B). C
-
You work in the Finance Department of the supermarket chainSuper.The company is planning to expand its business by offering online orders and home delivery. The CEO and CFO need your expertise to...
-
I use spreadsheets daily for both my personal and work life. I use them to calculate child support debt for non-custodial parents who owe a debt to the state, tribal, or non-assist. This helps us...
-
According to Scott O'Donnell, Big Apple Circus ' Vice President and General Manager, 70 percent of Big Apple Circus' overall revenues come from the touring unit, with 30 percent coming from donors,...
-
Alex's Tool and Dye Machine Co If we can't make it, you don't need it! HIGH-LOW METHOD Labor Cost Labor Hours May $ 5,410 585 June $ 4,900 595 July $ 5,570 690 August $ 5,570 680 September $ 5,590...
-
Fred is very generous. During the current year he made gifts as described below. In the case of each gift, state whether any portion of the gift constitutes a present interest for purposes of ...
-
The biggest part of this class for me was the financial concepts and models. I already knew that finances play an integral part of a company's success, but I didn't fully understand how finances were...
-
Ethics is often an integral part of internal controls. Read the case study presented below and then answer the questions using the ethical analysis framework that we referred to throughout the...
-
An auto-parts manufacturer is considering establishing an engineering computing center. This center will be equipped with three engineering workstations each of which would cost $25,000 and have a...
-
The Taos Museum of Southwestern Arts and Crafts (TMSAC) presents rotating exhibits of the works of artists and artisans from the Southwestern United States. Historically, the museum has derived its...
-
What is meant by exception reporting?
-
How much will $ 1,000 invested at 2 percent simple interest be worth in 10 years? What will it be worth if the interest rate is 3 percent?
-
Michael Roberts is a cost accountant and business analyst for Darby Design Company (DDC), which manufactures expensive brass doorknobs. DDC uses two direct-cost categories: direct materials and...
-
Omegas Fleet Feet, Inc., produces dance shoes for stores all over the world. While the pairs of shoes are boxed individually, they are crated and shipped in batches. The shipping department records...
-
The Zeta Company manufactures trendy, good-looking, moderately priced umbrellas. As Zetas senior financial analyst, you are asked to recommend a method of inventory costing. The CFO will use your...

Study smarter with the SolutionInn App