Question: Buffer Overflow Lab Smashing the Stack One way of manipulating the stack for unintended results is to change the return address on the stack to
Buffer Overflow Lab
Smashing the Stack
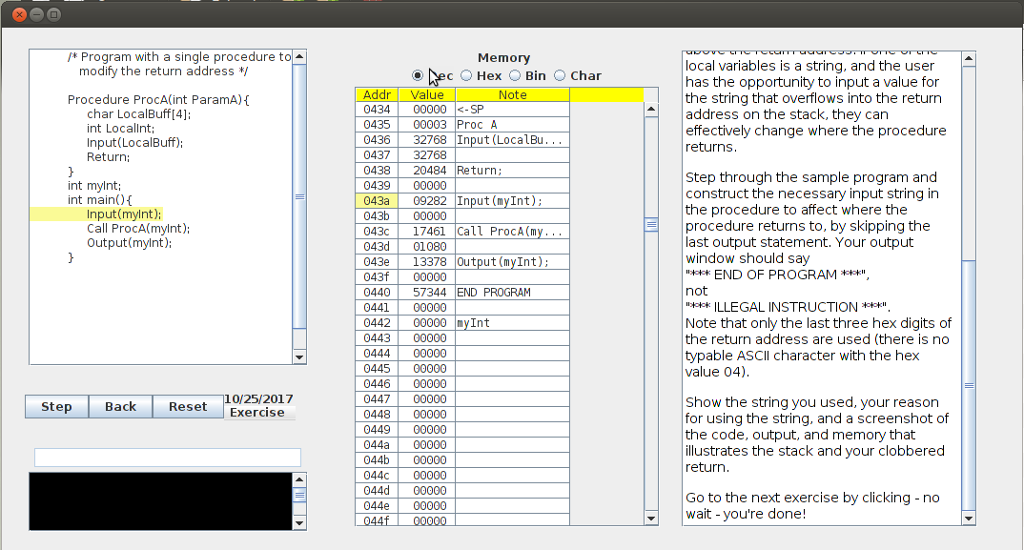
One way of manipulating the stack for unintended results is to change the return address on the stack to some pre-set location, possibly containing malicious code. When the procedure exits, it returns to whatever memory address is in the return address portion of the stack. If a malicious user can change the values of the stack to affect this address location, they can change which instruction gets executed next.
As we have previously seen, one way of changing memory locations is through a buffer overflow. Remember that local variables are pushed onto the stack above the return address. If one of the local variables is a string, and the user has the opportunity to input a value for the string that overflows into the return address on the stack, they can effectively change where the procedure returns.
EDIT: The simple machine simulator on the left shows a C-like language and corresponding memory. Memory contains both instructions and variables. This exercise has you identifying which locations are instructions and which are data.
1. Step through the sample program and construct the necessary input string in the procedure to affect where the procedure returns to, by skipping the last output statement. Your output window should say "*** END OF PROGRAM ***", not "*** ILLEGAL INSTRUCTION ***".
Note that only the last three hex digits of the return address are used (there is no typable ASCII character with the hex value 04). Show the string you used, your reason for using the string, and a screenshot of the code, output, and memory that illustrates the stack and your clobbered return.
/* Program with a single procedure to Memory local variables is a string, and the user has the opportunity to input a value for the string that overflows into the return address on the stack, they can effectively change where the procedure returns modify the return address */ ec OHex Bin Char Addr Value 04340000
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


