Question: c) The access control lists need to be stored in the system as well and are also a resource. Which subject should be authorized to
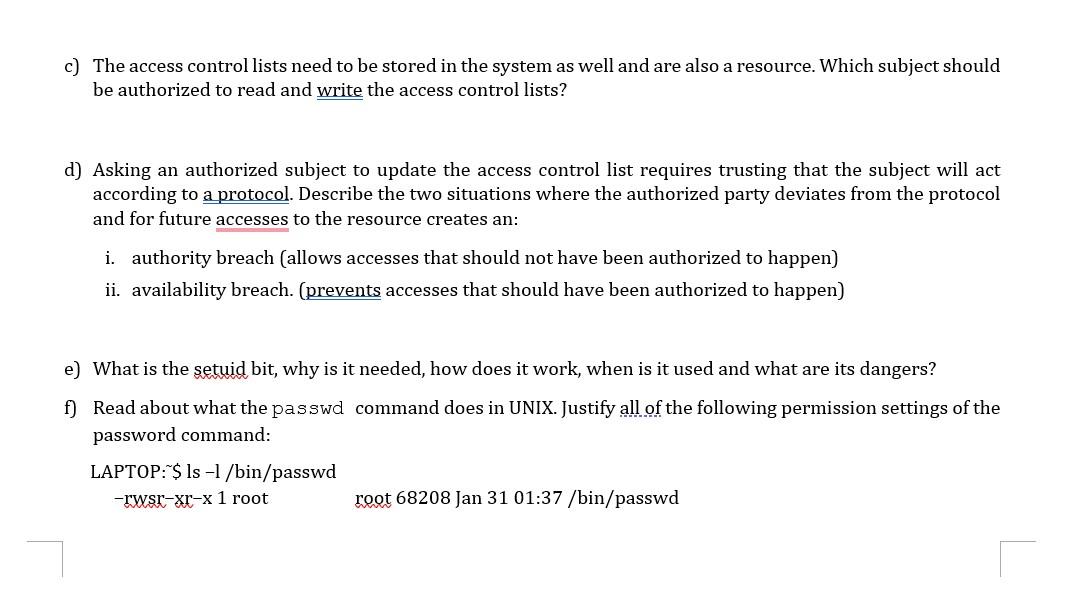
c) The access control lists need to be stored in the system as well and are also a resource. Which subject should be authorized to read and write the access control lists? d) Asking an authorized subject to update the access control list requires trusting that the subject will act according to a protocol. Describe the two situations where the authorized party deviates from the protocol and for future accesses to the resource creates an: i. authority breach (allows accesses that should not have been authorized to happen) ii. availability breach. (prevents accesses that should have been authorized to happen) e) What is the setuid bit, why is it needed, how does it work, when is it used and what are its dangers? f) Read about what the passwd command does in UNIX. Justify all of the following permission settings of the password command: LAPTOP: \$ ls - / /bin/passwd -rwsr-xr-x 1 root roet 68208 Jan 3101:37/bin/ passwd
Step by Step Solution
There are 3 Steps involved in it

Get step-by-step solutions from verified subject matter experts


