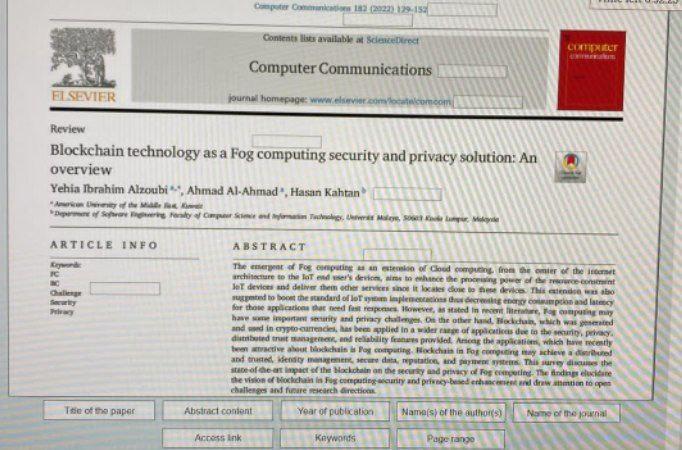
Question: Computer Com 183 (2022) 129-13 Content is available secret COMICE Computer Communications ELSEVIER journal homepage: www.viet.com Review Blockchain technology as a Fog computing security and
Step by Step Solution
There are 3 Steps involved in it
1 Expert Approved Answer
Step: 1 Unlock


Question Has Been Solved by an Expert!
Get step-by-step solutions from verified subject matter experts
Step: 2 Unlock
Step: 3 Unlock


