Question: Consider a file called in /importantfiles/csdata on a UNIX system The directory /importantfiles has permissions 777. It is owned by user dan and has
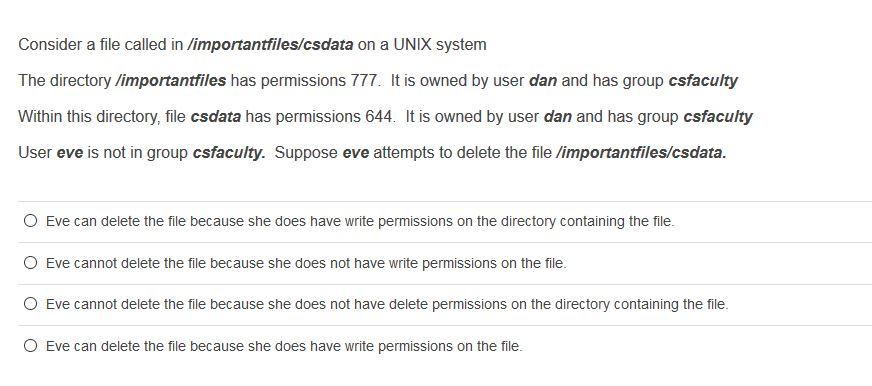
Consider a file called in /importantfiles/csdata on a UNIX system The directory /importantfiles has permissions 777. It is owned by user dan and has group csfaculty Within this directory, file csdata has permissions 644. It is owned by user dan and has group csfaculty User eve is not in group csfaculty. Suppose eve attempts to delete the file /importantfiles/csdata. O Eve can delete the file because she does have write permissions on the directory containing the file. Eve cannot delete the file because she does not have write permissions on the file. O Eve cannot delete the file because she does not have delete permissions on the directory containing the file. O Eve can delete the file because she does have write permissions on the file. Consider a file called in /importantfiles/csdata on a UNIX system The directory /importantfiles has permissions 777. It is owned by user dan and has group csfaculty Within this directory, file csdata has permissions 644. It is owned by user dan and has group csfaculty User eve is not in group csfaculty. Suppose eve attempts to delete the file /importantfiles/csdata. O Eve can delete the file because she does have write permissions on the directory containing the file. Eve cannot delete the file because she does not have write permissions on the file. O Eve cannot delete the file because she does not have delete permissions on the directory containing the file. O Eve can delete the file because she does have write permissions on the file.
Step by Step Solution
3.40 Rating (144 Votes )
There are 3 Steps involved in it
The detailed answer for the above question is provided below Answer The correct answer is c Eve cannot delete the file because she does not have delete permissions on the directory containing the file ... View full answer

Get step-by-step solutions from verified subject matter experts


